Has Cybersecurity Become the Definition of Insanity?
After years of breaches, stolen data, CIO/CISO resignations and huge impacts to business reputation, it’s time for the industry to rethink its approach to network security.
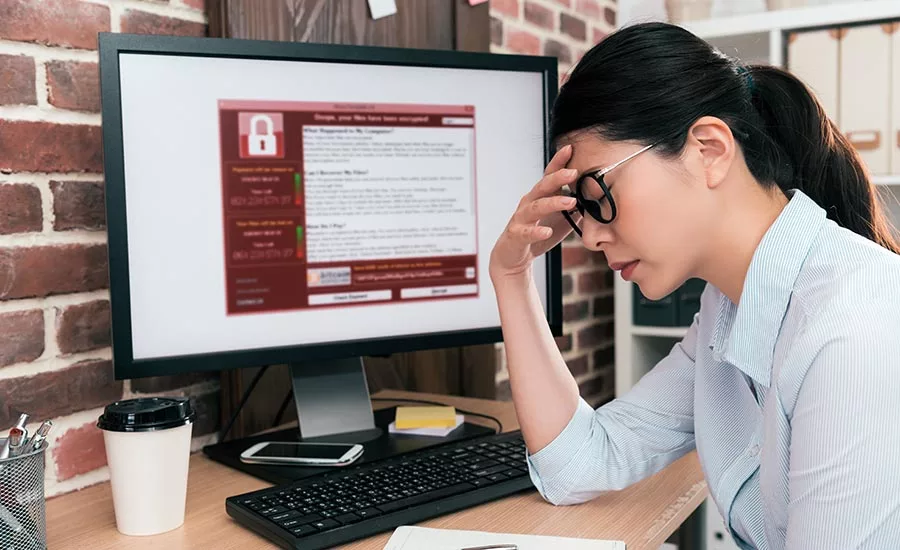
It shouldn’t take a data breach to make an organization realize that it’s time for a new approach. The IT industry has seen new technologies, a whole host of cybersecurity mistakes and watched countless organizations publicly apologize to its customers for stolen data. Yet, the industry still hasn’t changed the way it thinks about cybersecurity. The current thinking around cybersecurity falls into the definition of insanity, with many organizations doing the same thing over and over again, expecting different results, still being shocked when their company is the latest to hit the hacking headlines.
What the state of the industry shows us is that the current security model is broken. To overcome the complexities, organizations need to adopt an entirely new mindset when it comes to network security, and instead focus on the data.
The Industry Has Failed
This won’t come as a surprise to many. By overcomplicating network security for far too long, the industry has been left behind, trying the same methodologies over and over again and failing to make the changes required to keep critical and sensitive data safe.
We’ve all learned the lessons from the high profile data breaches that have formed the topic of huge debates over the last few years. OPM and Target were not only two massive breaches, but were clear signs that current attempts to secure corporate networks were – and are – just not enough. Quite simply, this is because organizations are trying to protect something they no longer own. For the last 15 years, security thinking has focused on the network. The premise being that it’s the network that is insecure, so by building up our network defenses, we can also protect the data that runs over it.
However, we don’t always own the networks over which our data runs, so therefore focusing on this aspect is leaving many other doors wide open. The corporate network used to remain in the data center, but in the digital economy present today, the corporate network spans over corporate locations worldwide, including data centres, private clouds and public clouds. This data is not just distributed to employees, but to third parties whose devices and policies cannot be easily controlled. Add legacy security measures into the mix which simply weren’t constructed to address the complexity and diversity of today’s corporate network, and it’s clear why this is not enough.
It’s time to make a change: the industry needs to take a step in the right direction and put data at the forefront of security.
Start with a Security Overlay
In an effort to keep their data and infrastructure secure, organizations have adopted an approach of layering technology on top of technology. However, the technology stack itself has become far too complicated, and the number of resources, operational overhead and cost needed to manage it have only contributed to the failing security mindset.
However, the change that needs to be made is simple. Organizations must start with a security overlay that covers the networks, independent of the infrastructure, rather than building the security strategy around the infrastructure. From a data security perspective, the network must become irrelevant, and with this flows a natural simplicity in approach.
As well as enabling organizations to better secure their data, this approach also has economic and commercial benefits. Taking intelligence out of the network allows it to focus on the core task of managing traffic, saving money and resources that can better be invested in a true security model with data protection at its centre.
A New Era of Cybersecurity
To begin this mindset change, organizations need to start thinking about security as an overlay on top of existing infrastructure. They also need to introduce a software-defined approach to data security, enabling a centralized orchestration of security policy. This centralized orchestration enforces capabilities such as software-defined application access control, cryptographic segmentation, data-in-motion privacy and a software-defined perimeter, and means that data is completely protected on its journey across any network, while hackers are restricted from moving laterally across the network once a breach has occurred. To further protect the network, organizations can also adopt innovative approaches such as Layer 4 encryption which renders the data itself useless, and therefore worthless to hackers, without impacting the operational visibility of the enterprise network and data flows.
There is no longer room for over-complicated network security. Put simply, the industry has no chance of progression if it continues to try the same methods over and over again, without making any changes and adapting to the new cybersecurity threat landscape. It’s time for organizations to dumb it down and adopt a simple software-defined overlay approach to security.