Email obfuscation tactics elude security protections

Image via Unsplash
Cyber attackers have used email obfuscation techniques for decades to conceal malicious code or data within a file, script or network traffic. There are many email obfuscation methods, such as putting addresses into images, captchas or texts that bots cannot read. Such traditional email obfuscation tactics are well known, and security controls have historically been good at patching and stopping them. But recently our threat researchers have uncovered some newly evolving techniques that are designed to evade modern security controls. Below, we detail this new attack technique including real-world examples our researchers have observed.
JavaScript-based obfuscation involves addresses that are dynamically placed onto a webpage, effectively hiding them from bots. Attackers can set an ID for the HTML tag containing the email address, with the email encoded in base64, a binary-to-text encoding scheme. Base64 represents binary data in an ASCII string format by translating it into a visual representation to ensure that humans can read the printable data.
The hidden encoding is designed to carry binary data across channels that can only reliably support text content, making it an ideal choice for embedding binary data within scripts or HTML documents. Encoding text into character sets like base64 is an effective obfuscation technique because obfuscation through encoding makes the analysis and detection of malicious content more difficult for security tools and analysts. Attackers leverage base64 and similar encoding techniques to hide malware, evade filters, embed malicious code and facilitate data exfiltration.
New phishing attacks incorporate homographic techniques
When designing an attack, the attackers will ask themselves, “How can I create content in a way that is clearly visible and understandable to the user, but the technical controls won’t be able to make sense of it?”
One effective way of doing so involves a homograph attack, which is a type of cyberthreat that exploits the similarity between characters from different scripts to deceive users into visiting malicious websites or opening harmful files. This technique relies on the use of homographs, which are characters that look alike but belong to different character sets, such as Latin and Cyrillic alphabets.
For example, an attacker might register a domain that visually resembles a legitimate domain by substituting similar-looking characters from different alphabets. The deceptive domain can then be used in phishing emails to trick users into believing they are visiting a trusted site. When recipients of the email click on the link, they may be led to a site that installs malware on their device or steals sensitive information.
Homograph attacks are particularly dangerous because they can be difficult to detect with a casual glance, making even the most alert users susceptible to phishing attempts. One example of the new threat we have identified involves the real-world advanced attack seen below that was sent to a company CFO in three layers, including homograph techniques, base64 encoding and CDN obfuscated credential harvesting pages.
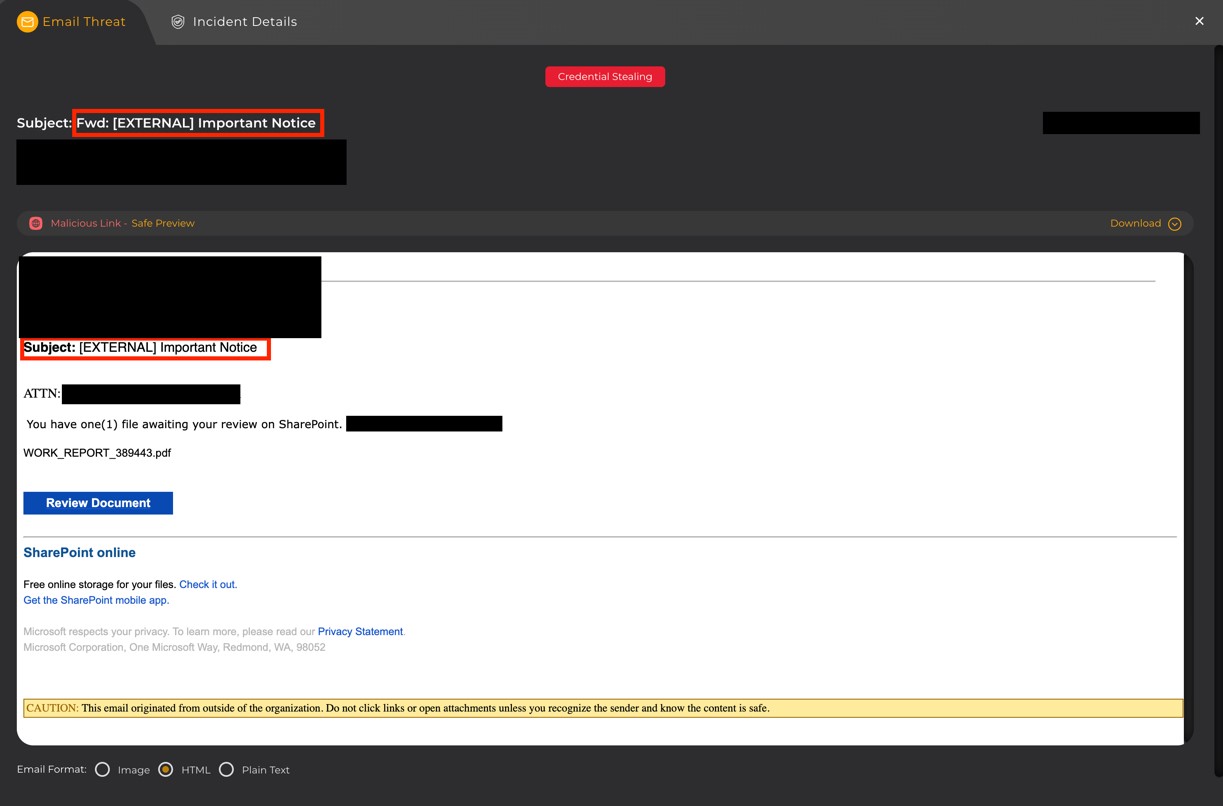 Figure 1: Redacted example of the new email obfuscation technique. This phishing email appears to be an innocuous work order hosted in SharePoint that needs review by the CFO: “You have one(1) file awaiting your review on SharePoint.” Image courtesy of Kowski
Figure 1: Redacted example of the new email obfuscation technique. This phishing email appears to be an innocuous work order hosted in SharePoint that needs review by the CFO: “You have one(1) file awaiting your review on SharePoint.” Image courtesy of KowskiIn the subject line, we find utf-8 encoded characters “‚Äã‚Äã‚Äã‚Äã” repeated between each highlighted letter of the subject:
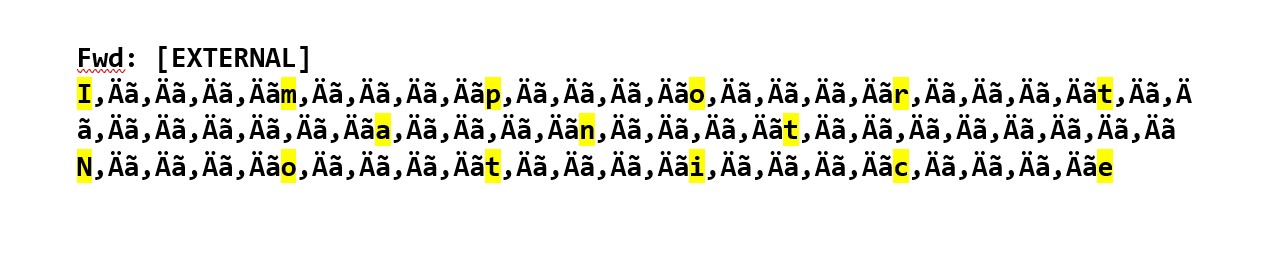 Image courtesy of Kowski
Image courtesy of KowskiThe attacker has crafted a subject line that looks like “Important Notice” to the human eye. Yet the technical controls see a somewhat random pattern of character strings. This strategy borrows inspiration from the old homograph attacks that swapped a lower case ‘L’ for an upper case ‘i’ in a domain name.
When the body of this email is viewed in an Image or Plaintext view, there isn’t much to see. But when you use the HTML view to peer behind it to the original message, you can see the body of this attack. In this situation, you won’t see a clear message, you will see a base64 encoded set of data. This tactic makes the body of this message unintelligible unless it is rendered by tools designed to decode this data, such as a browser or an HTML-rendered preview in your email client of choice.
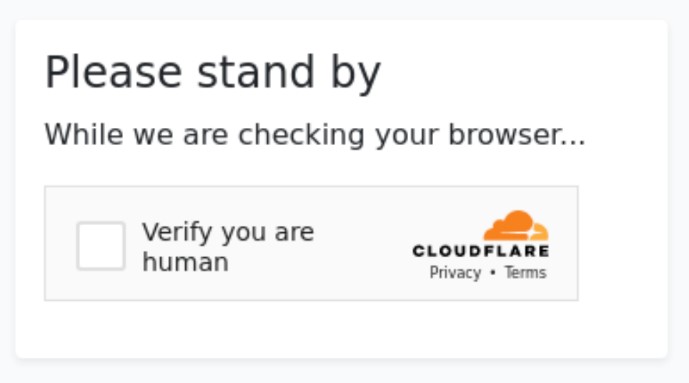 Figure 2: Image of a spoofed Cloudflare CDN message that requires the user to check a box in order to proceed. Image courtesy of Kowski
Figure 2: Image of a spoofed Cloudflare CDN message that requires the user to check a box in order to proceed. Image courtesy of KowskiThe web link provides the last piece of this puzzle, with obfuscation techniques delivered through a Content Delivery Network or CDN, which is a distributed network of servers that cache website content to speed data delivery. CDN tools have opened the floodgates to attackers, making it very economical to frustrate legacy security controls. Newer security protections must move past this CDN page to the true destination, where the malicious intent of the real page can be analyzed.
From this threat analysis, we can conclude that these new sophisticated attacks involve three different evasive obfuscation techniques and malicious email content. Therefore, security solutions must enable users to view attacks in these various formats and download original messages for more in-depth scrutiny. As attackers continue to refine their methods, the arms race will only persist between cybersecurity teams and bad actors, highlighting the need for vigilance, education and cutting-edge technology to secure our digital world.
