Security Top Stories
Electronic Access Control Tailors Security Protocols, Boosts User-Friendliness
Facilities of all stripes, ranging from churches and school districts, to healthcare centers to manufacturing plants, continue to move from hard keys to electronic access, or to upgrade their existing electronic access systems.
January 1, 2017
The Watchful Eye of Retail Surveillance in the Digital Age
Video surveillance, remote monitoring and facial recognition are critical security tools in retail security and loss prevention.
January 1, 2017
The High Cost of Not Doing Enough to Prevent Cyber Attacks
If you have a basic security program and think you can get by with the bare minimum standard security measures in place, you are mistaken.
December 13, 2016
Top Security Guarding Companies Report 2016
The security officer industry faces a ‘Watershed Moment’ as consolidation alters the landscape.
December 1, 2016
Banks Ramping Up Cyber Focus, Working to Coordiante Efforts
Securing banks and financial facilities takes building leadership capacity around security and underscoring its importance to executives.
December 1, 2016
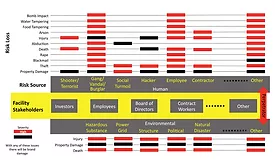
Using Environmental Risk Mapping and Analysis to Enable Effective Decision Making
Uninformed is unprepared. Build your own metrics and maps in order to make thoughtful, business-minded security decisions.
December 1, 2016
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing