Security Top Stories
How is Enterprise Security leveraging technology to manage mass note messages in and out of their facilities?
Read More
Security Robots on Patrol
How a security robot, the first one employed in Arizona, acts as a visual deterrent as well as an information-gathering machine.
October 8, 2018
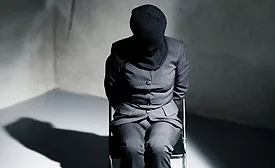
Our Executive is Missing: Kidnap and Ransom Basics for Security Professionals, Part 2
The second of a three-part series to help protective professionals understand how K&R can be successfully resolved.
October 3, 2018
Public-Private Partnerships and The Fight Against Terrorism
How strong relationships with the private sector are a pillar of the FBI’s strategy to combat global terrorism.
October 1, 2018
Clear, Purge & Destroy: When Data Must be Eliminated
Part 1 of a 2-part series on information disposal requirements
October 1, 2018
How to Manage Lone Worker Safety in a Dynamic World
Employees who are out of sight cannot be out of mind
September 25, 2018
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing