Home » C-suite security
Articles Tagged with ''C-suite security''
Changing Cultures, Changing Security at FM Global
National crises like 9/11 and the Virginia Tech shootings compelled Whit Chaiyabhat into a career of public service and risk management advocacy.
December 1, 2018
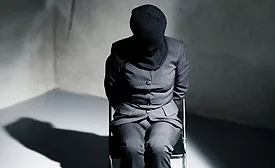
Our Executive is Missing: Kidnap and Ransom Basics for Security Professionals, Part 3
This is the third of a three-part series to help enterprise protective professionals understand how K&R can be successfully resolved.
November 14, 2018
Our Executive is Missing: Kidnap and Ransom Basics for Security Professionals, Part 2
The second of a three-part series to help protective professionals understand how K&R can be successfully resolved.
October 3, 2018
Our Executive is Missing: Kidnap and Ransom Basics for Security Professionals
The first of a three-part series to help protective professionals understand how K&R can be successfully resolved.
September 13, 2018
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing