Why passwords are on the way out, and why we need them anyways
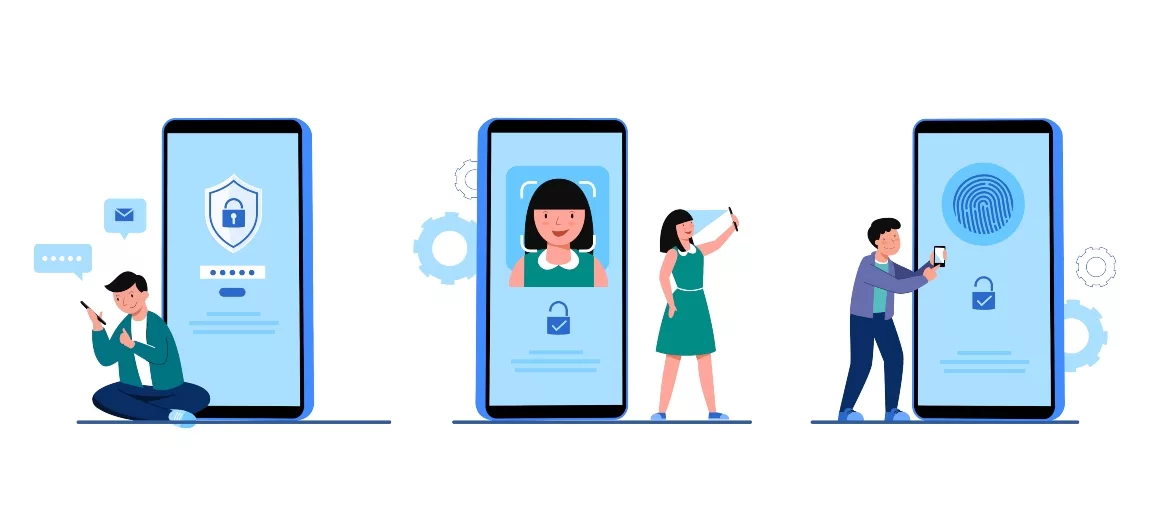
Image by jcomp via Freepik
In May, Microsoft, Apple and Google announced plans to expand support for the FIDO2 passwordless authentication standard. In a time of constantly increasing cyber risk, that is good news: during the first quarter of 2022, data breaches and account compromises increased by 14%. Organizations are looking for better ways to stay secure, and — after many years of service — the humble password just isn’t cutting it anymore.
Unfortunately, a passwordless future isn’t here yet — but in the meantime, organizations still need ways to protect their systems and employees from compromise. Fortunately, they can do that by utilizing passwords more effectively and combining them with other methods of authentication.
The Problem with Passwords
To understand the problem with passwords, we have to understand three qualities of a great authentication mechanism: strength, uniqueness and ease of use. A strong authentication mechanism is one that is hard to replicate or steal; a unique one is only used for a single purpose; one that’s easy to use is fast, hard to misplace and not difficult to recover.
When it comes to passwords, strength, uniqueness and ease of use are limited by the capacity — and sometimes laziness — of human beings. First, we can only remember so many unique characters, putting a limit on password strength. Second, we can only remember logins for so many websites and applications, putting a limit on uniqueness. Third, passwords can be annoyingly cumbersome to use, especially when they have to be changed or reset.
But most importantly, passwords have become trivially easy for cyber actors to compromise, whether by phishing, keylogging, or data exfiltration — moreover, with today’s processing power, most passwords are easy to crack, as evidenced by the 15 billion stolen passwords for sale on the Dark Web. It’s clear that passwords have weaknesses: but what about the alternatives?
What a Passwordless Future Means
In the near future, Microsoft, Apple and Google will be implementing increased support for the Fast Identity Online Alliance’s FIDO2 standard and the WebAuthn API. Ultimately, that means users of the three tech ecosystems will be able to:
- Store a unique passkey on their personal device for multiple apps and services, while unlocking their device using biometrics or a pin code.
- Use the same authentication standard across all major desktop operating systems, mobile devices and browsers.
- Use their device to enroll new devices quickly and painlessly.
FIDO2 forms a seamless tapestry of secure access combining the three traits that passwords lack: strength, uniqueness and ease of use. As a harbinger of things to come, it is exciting — but it does not solve the problems organizations face in the present.
Why Passwords Are Still Necessary (For Now)
Despite all the progress that has been made towards a passwordless future, it isn’t here just yet — expanded FIDO2 integration is still in beta — and when it does roll out, organizations will still be using legacy apps and equipment that lack support.
Many enterprises will need time to make the transition to a passwordless future. Fortunately, those who still have to use passwords can start using them in smarter ways:
- Choose better passwords: Commonly used passwords are easy to guess, and even easier to brute force — aside from containing special characters, passwords should be at least 12 characters long.
- Update passwords regularly: Passwords should be updated every three months at a minimum, and they should be substantially different from previous passwords.
- Use multi-factor authentication (MFA): Just because you aren’t ready to replace passwords doesn’t mean you can’t supplement them with biometrics, smartcards, or text messages.
While 61% of breaches can be traced to compromised credentials, this also means that better passwords are all it takes to significantly reduce the chance of a security incident.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!
.webp?height=96&t=1657123061&width=96)





