Business email compromise costs $43 billion

In a new public service announcement, the Federal Bureau of Investigation (FBI) said that the amount of money lost to business email compromise (BEC) scams continue to grow each year, with a 65% increase in the identified global exposed losses between July 2019 and December 2021.
Banks located in Thailand and Hong Kong were the primary international destinations of fraudulent funds. China, which ranked in the top two destinations in previous years, ranked third in 2021, followed by Mexico and Singapore.
From June 2016 until July 2019, IC3 received victim complaints regarding more than 241,000 domestic and international incidents, with a total exposed dollar loss of over $43 billion.
*Click the image for greater detail
Image courtesy of the FBI
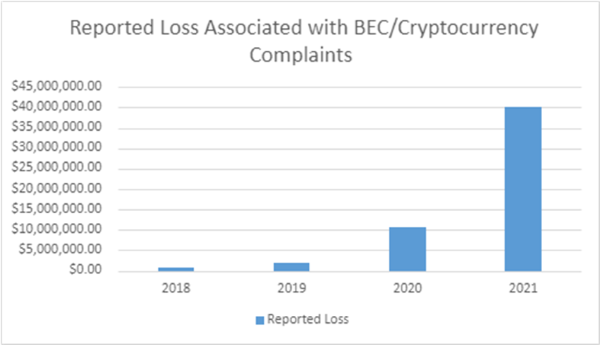
The IC3 has also received an increased number of BEC complaints involving cryptocurrency, which is popular among illicit actors due to the high degree of anonymity associated with it and the speed at which transactions occur.
Two iterations of the BEC scam where cryptocurrency was utilized included a direct transfer to a cryptocurrency exchange (CE) or a "second hop" transfer to a CE. The victim is unaware that the funds are being sent to be converted to cryptocurrency in both situations.
Andy Gill, Senior Security Consultant at ARES Consulting>, says that the number of incidents reported by the ICI is likely low, as many incidents of this nature likely go unreported and are swept under the rug.
"BEC attacks continue to be one of the most active attack methods utilized by criminals because they work. If they didn't work as well as they do, the criminals would switch tactics to something with a larger ROI," Gill says.
Victims prefer not to especially report incidents if the amount is quite small, but those who fall for larger financial fraud BEC that amounts to thousands or even sometimes millions of U.S. dollars must report the incident in the hope that they could recoup some of the losses, says Joseph Carson, chief security scientist and Advisory CISO at Delinea. A major challenge with BEC security incidents is that victims have to prove that the account was compromised and that the incident was not just human error, which can be difficult to gather as cybercriminals are pretty good at hiding tracks.
"Most organizations who become victims of BEC are not resourced internally to deal with incident response or digital forensics, so they typically require external support," Carson adds. "Moving forward, I highly recommend that organizations seek expertise in the private sector for incident response and digital forensics and, at the same time, report the BEC crime to law enforcement. This will help accelerate the investigation with expert resources while the crime navigates the law enforcement chain of response."
A strong privileged access management (PAM) solution can help reduce the risk of BEC by adding additional security controls to sensitive, privileged accounts along with multi-factor authentication (MFA) and continuous verification, Carson explains. "It is also important that cyber awareness training is a top priority and always practice identity proofing techniques to verify the source of the requests."
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






