How to stop ransomware - Seven steps to protect your enterprise

Any connected device, including smart phones, laptops, servers, industrial machinery, etc., can be targeted by cybercriminals for ransomware attacks on company networks and systems.
Today’s attackers are looking for multi-million-dollar payouts and use increasingly sophisticated methods to achieve their goals. In a world where the types of attacks organizations face are constantly evolving and targeted at prey of all sizes, from individuals all the way up to large corporations (even cybersecurity companies), enterprises must ensure their cybersecurity infrastructure is ready to protect against potential threats.
So how do cybercriminals enter your network?
There are numerous paths for ransomware infection, but three of the most common are:
- Phishing and Social Engineering: In recent years phishing attacks have grown increasingly sophisticated and more difficult to detect. A hacker can easily send out thousands of phishing emails and only needs one user to click on a malicious attachment or to visit an infected website to gain access to an employee’s computer. Once access is gained, the hacker has a backdoor into the network and can extend the attack vertically within the network.
- Password Compromises: Even more common than successful phishing attacks are password breaches. Weak and stolen passwords are the leading factor in data breaches year after year and attempts to improve password security have failed to correct this problem. A new solution is clearly needed. Implementing stronger passwords to eliminate easy-to-guess passwords has not improved the situation. Instead, it has resulted in password reuse, with these reused passwords vulnerable to credential stuffing attacks. Multi-factor authentication systems introduced to improve security have also proven insufficient as hackers have been able to implement successful attacks against them as well. Truly resolving this problem requires passwordless solutions using digital certificates.
- Attacks on Software Vulnerabilities: While phishing and password breaches remain at the top of the list, hackers still frequently gain access to corporate networks by exploiting software vulnerabilities. Researchers and hackers continue to find vulnerabilities in widely used software products, with web servers, operating systems, web browsers and email tools being common targets. In many cases, these vulnerabilities could have been eliminated by keeping systems up to date with the most recent security patches. All too often, organizations fail to keep up with software patches containing security fixes, leaving vulnerabilities in place and creating easy targets for hackers.
How to Protect Your Network and Stop Malware?
There are seven steps that will help your company fight off ransomware attacks:
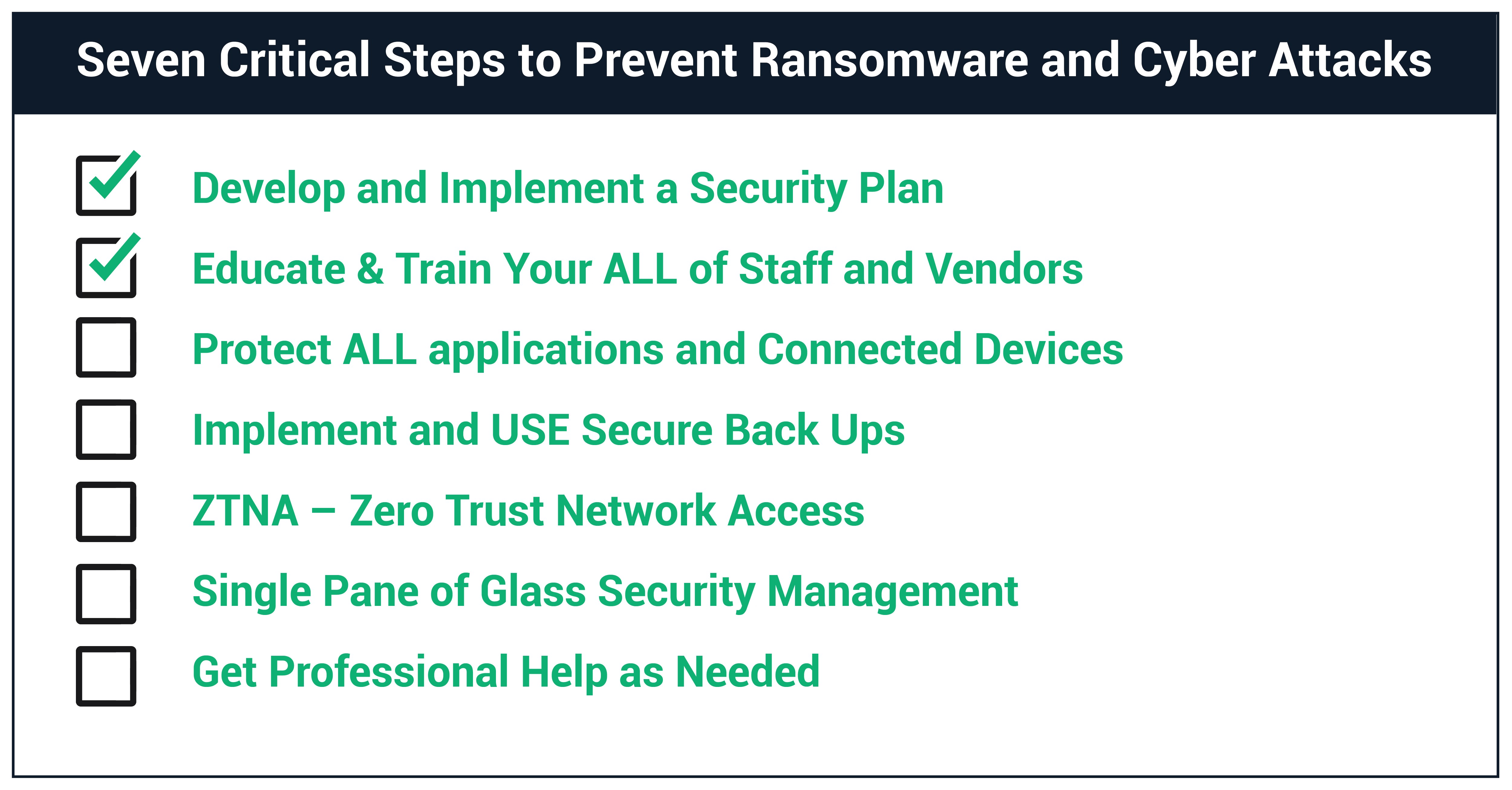 Image courtesy of Sectigo
Image courtesy of Sectigo
Step One: Develop a Security Plan. As no digitally connected company is too small or too big to be targeted by cybercriminals, organizations must develop and IMPLEMENT a comprehensive cybersecurity program that encompasses everyone in the company, from customer service to engineers to executive management. Yes, bigger companies are frequently targeted, but that does not mean that smaller businesses and organizations are immune.
Step Two: Educate. Ensure your staff, especially your remote workers, understand the basics of security policies and digital hygiene, including training to help them recognize and avoid social engineering and phishing attacks.
Step Three: Protect with Strong Authentication. Make sure your web applications and all connected devices (including those connected via VPN) are protected by strong authentication. This includes working with all visitors, contractors, and business partners to ensure that THEIR mobile devices are protected against cyber-attacks.
Step Four: Implement Secure Backups. Make sure these backups cannot be discovered and attacked by ransomware as well. This could include offline backups along with “secure” online storage and data backup options.
Step Five: Use Zero Trust Network Access. Incorporate principles of Zero Trust Network Access (ZTNA), which assumes all traffic both inside and outside the firewall might be hostile, and no endpoints are trusted until they can authenticate. It requires that every network is treated similarly to how you would treat the hostile public internet. Implementation of ZTNA requires digital identities – Public Key Infrastructure (PKI) – at its foundation.
Step Six: Use the “Single Pane of Glass” Approach. Having 24/7 visibility into the entire security process is especially critical for large international organizations with assets distributed throughout numerous offices, warehouses, and industrial facilities. It is critical that IT managers have the capability to easily view and manage security for thousands of machines and their users, no matter where they are located. A single expired or misconfigured security certificate can bring the whole company down – or even worse – enable a hacker to penetrate your networks and systems.
Step Seven: Use a Third-Party Security Company. Research and utilize a well-respected security company to handle your business’s security. However, as evidenced by the recent SolarWinds and Kasaya attacks, IT and security managers need to realize that if one of these security companies is successfully breached, their computer systems and data could also be at risk. This is where offline backups can save the day and bring an organization online quicker.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







