Cybersecurity experts in Luxembourg earn the highest salaries and more data on cyber jobs around the world

A new report from Techshielder analyzed several metrics to determine the best cities for cybersecurity jobs, including average salary, job availability and cost of living as well as the most in-demand skills for 2021.
The report, names Washington D.C. as the best city for cybersecurity jobs thanks to its many job opportunities and overall high average salary in these roles. Singapore was found to have the highest job availability for cybersecurity professionals, while Luxembourg pays cybersecurity experts the highest salaries.
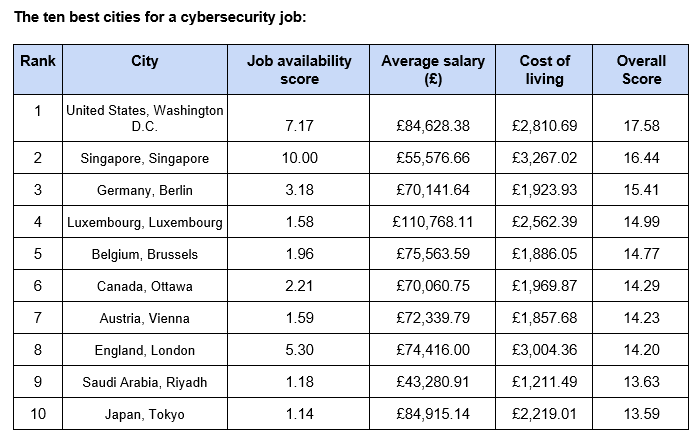
Table courtesy of Techshielder
It may not come as a surprise that Washington D.C sits at the top of the ranking — the capital is the headquarters of government agencies that employ many cybersecurity professionals.
Scoring a total score of 17.58, the city ranks second for job availability for those looking to work in the cybersecurity sector, balanced with the high average salary of £84,628 this city is a great contender for those looking to work in the industry.
Singapore comes in second place. The southeastern Asia city has the highest job availability out of all the cities examined. However, the average salary of £55,577 and the high cost of living of £3,267 brings it down.
London only ranks 8th, losing points because of its lower salary compared to other cities and the high cost of living, the city fails to make the top 5.
Singapore has the most cybersecurity jobs available
Recent graduates and any job seekers looking for a new role can increase their chances of getting hired by looking for cities with the largest number of job openings.
Techshielder analyzed the amount of cybersecurity-related jobs available on Indeed and Glassdoor to reveal the cities with the most cybersecurity jobs.
Singapore comes in first place with a job availability of 10, this is followed by Washington D.C and London rounds of the top three (7.17 and 5.30 job availability scores respectively).
At the other end of the scale, there is Islamabad in Pakistan, where the research found there is very limited opportunity for those in the field. Scoring a job availability score of just 1.01 this city has the fewest number of jobs available for cybersecurity professionals.
Cybersecurity experts in Luxembourg earn the highest salaries
Cybersecurity is a booming field with the potential to grow immensely. To get the most bang for your buck in this marketplace, it is also important to consider the cost of living. Any salary increase can be swiftly consumed by the differences in the cost of living.
Knowing the true value of a salary in different locations is just as crucial as knowing the pay.
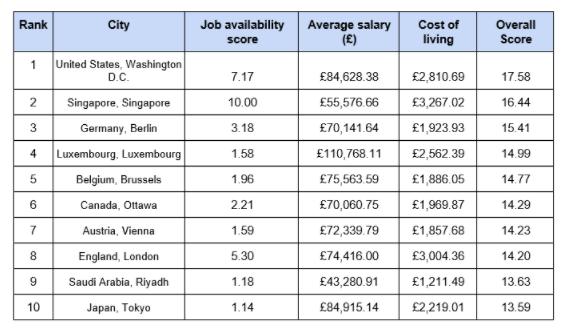
Table courtesy of Techshielder
The most in-demand skills to learn in 2021
While there is a high demand for jobs, you can’t start a career within the cybersecurity sector without the right expertise. The Techshielder report analyzed the most in-demand skills that employers looking to hire cybersecurity professionals are asking for:
- Network: One of the most in-demand skills and maybe one of the most important one for anyone in cybersecurity is networking. Understanding how networks work allows you to get a better comprehension of how many things work behind the scene.
- Threats: Threat intelligence ranks as the second most in-demand skill in 2021. Being able to evaluate threats and prevent or mitigate cyberattacks is a highly sorted after skill.
- Compliance: From the European Union’s GDPR to the California Consumer Privacy Act, companies need employees who can assess the risk and understand the paperwork and the security protocols are needed to keep personal data safe.
- Cloud: More companies are moving to cloud infrastructure and therefore the need for cloud-savvy professional are on the rise. These experts need to be able to arrange, organize and monitor a virtualized environment such as SaaS, PaaS or IaaS so that they can protect data from being deleted, leaked or even stolen.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





