Almost 20% increase in corporate security breaches since WFH
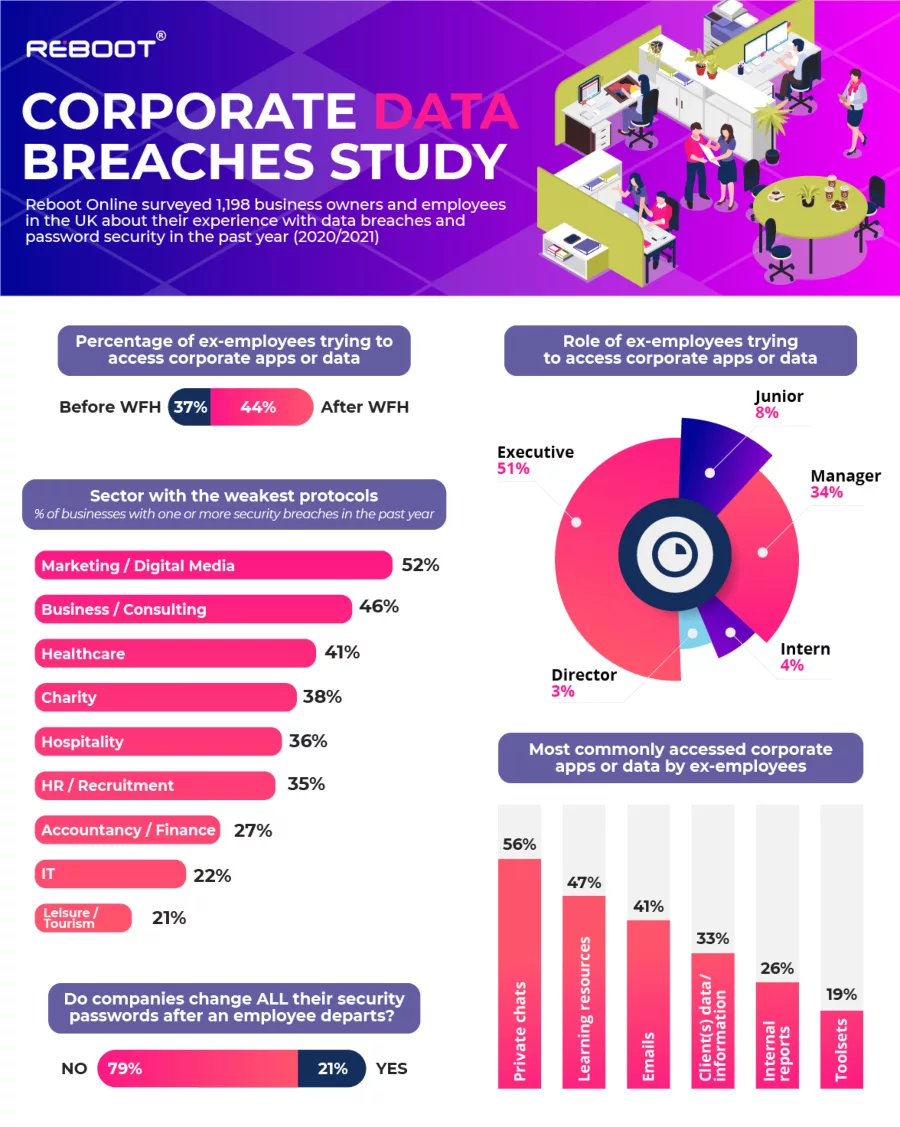
Image courtesy of Reboot
This past year has been a challenging one for many business owners and employees who’ve been forced to leave the office environment and switch to working from home (WFH) full time. Whilst this undoubtedly has its benefits, the risk of data breaches has exponentially grown.
With that in mind, the Digital Marketing experts at Reboot Online surveyed 1,198 business owners and employees across the UK on their experiences with data breaches and password security in the past year (2020/2021). Key findings include:
Almost a 20% increase in corporate security breaches since WFH!
44% of business owners have said they have experienced a former employee trying to log into corporate apps or data. This is a 19% increase from the previous year, pre-pandemic, when people were working in the office (37%).
Who are the guiltiest former employees?
After internal investigations, most businesses have managed to pinpoint the persons in charge of the security offences. Interestingly 51% of them were hired as Executives. Managers come in second place with 34% of internal security breaches made by them. Directors were the least likely to break security protocols (3%).
What data is most accessed by ex-employees?
The majority of data breaches (56%) involve private chats. Business owners have noticed former employees trying to access private conversations from when they were a part of the company.
Interestingly, in second place are learning resources with 47% of ex-employees still trying to benefit from these work perks. This is unsurprising given the fact many people have been focusing on personal development whilst WFH.
Other applications most accessed by former employees include emails (41%), client(s) data/information (33%), internal reports (26%) and toolsets (19%).
Which sectors have the weakest protocols?
The experts at Reboot Online also looked at the percentage of businesses with one or more security breaches in the past year. This led them to find that Marketing and Digital Media companies are most likely to suffer from security breaches (52%). This is followed by Business and Consulting (46%), Healthcare (41%) and Charity organizations (38%).
Why are security breaches so common?
This study demonstrates that security breaches are more common now that more people work from home, but how preventable are they?
Interestingly, Reboot Online found out that a shocking 79% of businesses do not change all their security passwords after an employee departs. Furthermore, 71% of businesses do not offer proper personnel password training to employees.
Shai Aharony, CEO and Founder at Reboot Online says, “Protecting your business from ill-intended former employees is vital, yet a shocking number of businesses forget to [prioritize] that. Trusting the wrong people and being careless can cost you greatly. The first step to ensure the adequate protection of your business is to train your staff to be aware of the importance of data security. This will ensure everyone avoids mistakes that can lead to unwanted breaches. It should, in fact, be part of your company culture. Secondly, make sure to carry out risk assessments often, especially after the departure of an employee - whether they left on good terms or not, you can never be too sure of the intention of others. Better to be safe than sorry. If in doubt, third party data security evaluations are a great way to ensure there is no threat to your company and advice from experts are always welcomed.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





