NSA releases cybersecurity guide on detecting and fixing outdated encryption protocol implementations

The National Security Agency released a cybersecurity product detailing how to detect and fix out-of-date encryption protocol implementations. Networks and systems that use deprecated forms of Transport Layer Security (TLS) or Secure Sockets Layer (SSL) for traffic sessions are at risk of sensitive data exposure and decryption.
The Cybersecurity Information Sheet, “Eliminating Obsolete Transport Layer Security (TLS) Protocol Configurations” instructs National Security System (NSS), Department of Defense (DoD), and Defense Industrial Base (DIB) system administrators on how to detect, prioritize, and replace unauthorized or deprecated TLS protocols with ones that meet current standards. Committee on National Security Systems (CNSS) Policy 15 requires that TLS protocols used by National Security Systems meet specified algorithm standards. Remediation is crucial to decreasing computer system and network attack surfaces and preventing unauthorized access to private data.
To help system administrators fix their network components, NSA developed several server configurations and network signatures to accompany the report that are available on the NSA Cybersecurity Github. While this information is provided to assist NSA's mission customers, any network administrator interested in finding and fixing their network components to allow only authorized and strong encryption protocol configurations may find it useful.
NSA seeks to regularly release unique, actionable, and timely cybersecurity guidance to secure the Department of Defense, National Security Systems, and the Defense Industrial Base. For more information or other cybersecurity products, visit NSA.gov/cybersecurity-guidance.
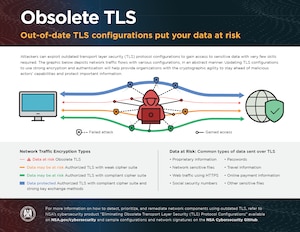
For a quick view on obsolete TLS, review the infographic.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!