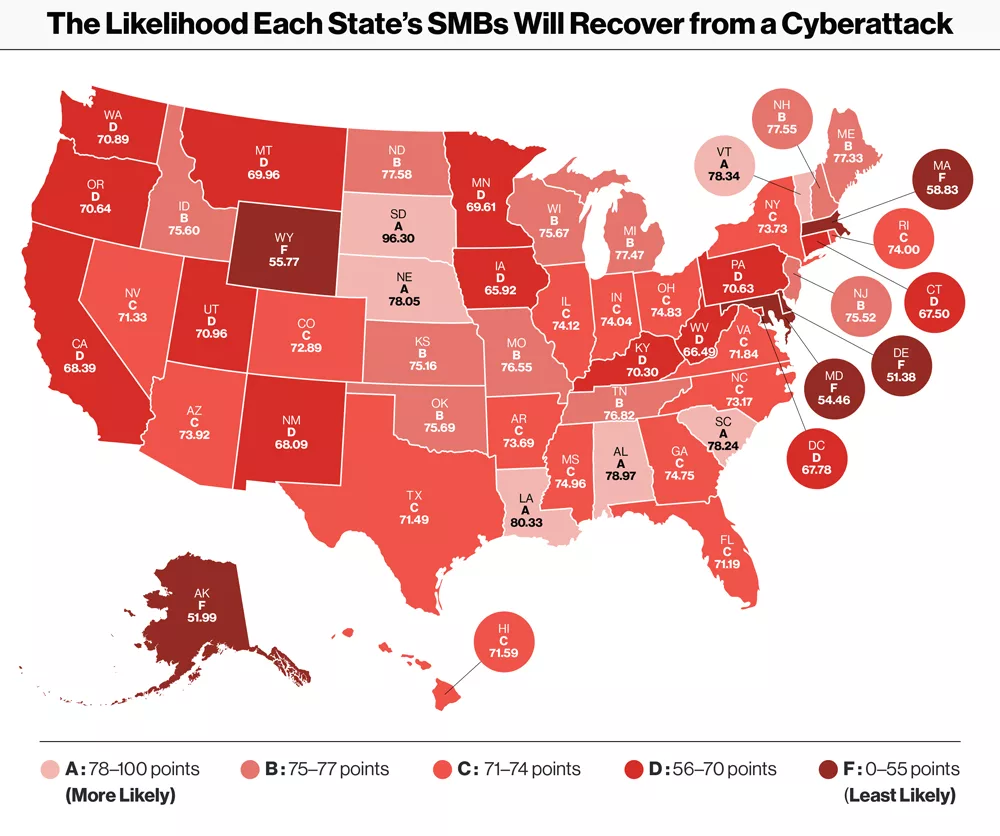
Top US states least likely to go bankrupt after a cyberattack
Cyberattacks have increased by 400% since before the COVID-19 pandemic. As cyberattacks become more prevalent, it’s especially important that small businesses protect themselves, since they face a high risk of bankruptcy following a cyberattack.
Small- to medium-sized businesses (SMBs) typically don’t prioritize cybersecurity as much as large companies too, which makes them prime targets for malware, phishing, viruses, and other cybersecurity threats. Unfortunately, few SMBs survive cyberattacks—nearly 60% of all SMBs fold within six months of a successful cyberattack.
Verizon security leaders evaluated which states’ businesses fare best after cyberattacks. To determine the odds of a business recovering from a cyberattack in any given state, they analyzed a host of factors, including internet privacy laws and the number of cyberattacks businesses within each state suffer each year.
Here’s what they found.
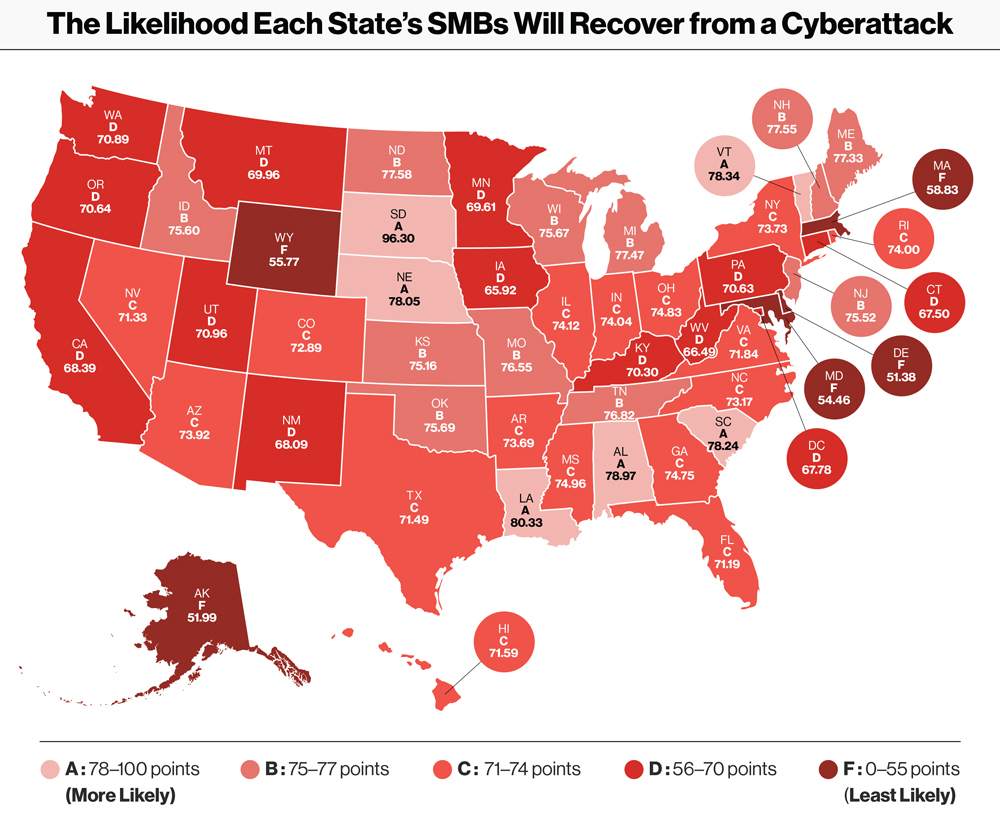
The Top 5: State-by-State Breakdown

South Dakota, which has cleverly dubbed itself the “Silicon Prairie,” has the highest number of small businesses per capita: 4,725 small businesses per 10,000 residents.
The state also recently signed into law a data privacy bill that requires companies and residents to report data breaches that affect more than 250 residents to the state’s Attorney General and consumer reporting agencies within sixty days of discovery.

Louisiana requires that businesses report a data breach to consumers within sixty days. It also requires that businesses notify the government of the breach, regardless of how many individuals were affected.
In addition, Louisiana SMB Development recently launched a no-cost cybersecurity initiative that offers various training programs to help businesses in Louisiana fortify themselves against cyberattacks.

Alabama requires that businesses report a data breach within forty-five days. Plus, Alabama is vigilant when it comes to cybersecurity research. Seven federal agencies within the state are involved in cybersecurity research, fifteen colleges in Alabama offer IT courses that cover cybersecurity, and the state is home to ten cybersecurity startups.

Businesses in Vermont must notify consumers and the government as soon as the breach occurs, without reasonable delay and no later than forty-five days from occurrence—fifteen days sooner than South Dakota and Louisiana.

As in Vermont, businesses in South Carolina are required to notify consumers of a breach as soon as it occurs. Thanks to the South Carolina Insurance Data Security Act, South Carolina was the first state in the country to pass legislation that protects SMBs from cybersecurity threats.
For the full story, please visit https://go.verizon.com/resources/smb-cyberattack-bankruptcies/
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







