TSA continues piloting “self-service” checkpoint technology

The Transportation Security Administration (TSA) is piloting a new touchless “self-service” technology that matches a traveler’s live photo with the photo on their ID. The initiative automatically authenticates a traveler’s ID, matches the live photo with the image on their ID, and confirms their flight information in near real time.
“In light of COVID-19, advanced health and safety precautions have become a top priority and part of the new normal for TSA,” said TSA Administrator David Pekoske. “As a result, we are exploring rapid testing and deployment of this touchless, self-service technology. At the conclusion of the pilot, we expect to be able to determine how positioning the new technology will allow passengers to use it themselves thereby providing a safer checkpoint experience, while adding significant security benefits.”
The current pilot at Ronald Reagan Washington National Airport (DCA) follows a previous 30-day test of the credential authentication technology with a camera in September 2019 at McCarran International Airport with volunteer TSA PreCheck™ passengers. Following that pilot, TSA refined the technology in partnership with the vendor and industry experts. The pilot at DCA also includes volunteer TSA PreCheck travelers, who generally have the shortest wait times and the least amount of physical contact while at a TSA checkpoint.
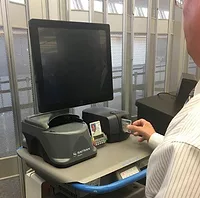
Travelers at DCA are now able to voluntarily participate in the pilot. Passengers will be able to approach the device and insert their own ID into the scanner for authentication, rather than physically handing it to a TSA officer, thus promoting social distancing and reducing physical contact. The device will also verify the identity of passengers by taking a photo of the traveler and comparing it with the image on their ID. The device will display results for face matching, ID authentication, and flight information to the TSA officer, who will be behind an acrylic shield to further minimize contact between the officer and passengers.
The credential authentication technology units authenticate several thousand types of IDs including:
- U.S. driver’s licenses and photo IDs issued by state motor vehicle departments
- U.S. passports/Permanent resident cards or visas
- U.S. military common access cards/Retired and Uniformed service military ID cards
- Department of Homeland Security Trusted Traveler ID cards
Photographs of travelers taken as part of the program are not saved, as there is no capacity to do so. The photographs are only used for identity verification to confirm that the photo matches the image on the traveler’s ID and ensure the passenger is the true bearer of an authentic ID. Signs near the checkpoint will provide notice to passengers on how to participate in the pilot, in addition to providing instructions on how to decline having their photo taken, although passenger IDs will still have to be scanned through the device for identity verification. Participating travelers may complete a brief survey via a QR code regarding their experience and satisfaction with the self-service system and its usability.
For broadcast content, please see TSA courtesy B-roll of the new machines in use at DCA.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!