Reducing the Chaos: How to Create a Security Operations Center that Helps
In March 2017, drivers on a Montreal highway were stuck for more than 12 hours in 15 inches of snow. Generally, the city is very efficient at keeping highways clear even in extreme weather. But, because of a lack of coordination and an inability to share information between first responders, various highway authority groups, and the city, more than 300 motorists were stranded in their cars overnight.
All of this could have been avoided if Montreal had a centralized location that connected operations and stakeholders to allow them to efficiently and securely share information. What the city needed was its own version of a security operations center (SOC).
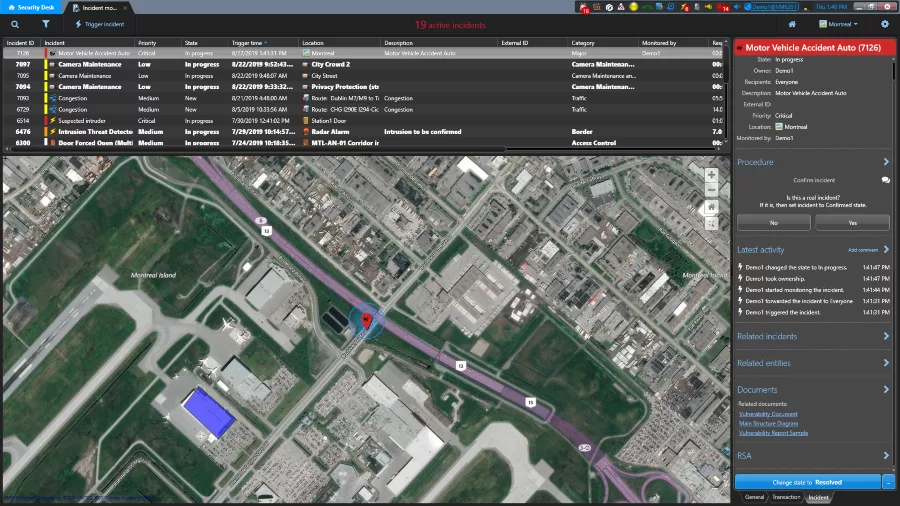
A SOC is a centralized unit where personnel manage operations. It’s a single location that houses multiple systems, including video management, access control, IoT, RADAR and ALPR, and gives a variety of stakeholders’ access to those systems. The goal is to provide a common framework and understanding for any situation. For security operators, a SOC can also provide both support for day-to-day functions and greater situational awareness when they respond to events and incidents.
Globally Distributed Security Operations Centers
Large organizations, like McDonalds or Starbucks, can create a Global SOC, or GSOC, to help manage operations centrally. A GSOC is a series of distributed SOCs across multiple locations. Global banks and railway systems are good examples of organizations that deploy GSOCs. In both cases, individual banks or train stations can have a local SOC, which can be federated across an entire country or around the world in a GSOC.
By federating individual SOCs, organizations make it easier and safer to share resources between locations. As you would expect, the benefits and challenges of working in a SOC or GSOC are very much the same. They just scale depending on the size of the network and the amount of data being collected and shared.
Not all SOCs are Created Equal
The make-up of an individual SOC depends largely on the organization and the technology deployed in it. A SOC that’s not well considered can actually create more problems than it solves. For example, by bringing together a wide range of sophisticated systems, a SOC can create a chaotic environment for security operators. According to Cisco’s Security Capabilities Benchmark study in 2018, 90 percent of alarms that come through a SOC are, in fact, false or nuisance alarms. This causes alarm fatigue in operators.
A false alarm can be anything from a motion detector that sets off an alarm in the SOC every time it senses a piece of debris to an alarm being triggered every time a sensor loses power. In the short-term, this can lead security operators to ignore or turn off nuisance alarms, leaving the system and the organization vulnerable. In the long-term, burn out can play a significant role in frequent operator turnover.
Information Overload—Can There Be Too Much of a Good Thing?
Adding to the chaos can be the sheer volume of information coming into a SOC. While false alarms involve notifications for non-events, information overload occurs because a system rightly signals that an event has happened, including a forced door, a scofflaw vehicle entering the parking lot, or a camera going down.
By themselves, these events are not an issue. But the average SOC has more than 20 systems, all designed to inform security personnel when an event occurs. This results in a constant stream of information coming into a SOC.
It’s easy to see why operators working in even a small SOC might feel overwhelmed. But, for larger organizations, the impact is much greater. The SOC at large international airports can see 5,000 events per second, or half a billion per day.
As with the volume of false or nuisance alarms, managing this constant stream of information can also lead to frequent operator turnover. When turnover rates are high, organizations are forced to spend extra time and resources constantly training new personnel. With so much information coming in, what operators really need is a way to determine which events are truly important, what needs to be investigated and how urgently that investigation must occur.
The role of a Collaborative Decision Management System
In order to address their challenges, organizations need to develop a SOC that truly supports operators. A key component of an effective SOC is a collaborative decision management system.
A collaborative decision management system first groups together detected events — a blacklisted plate in the parking lot, a perimeter breach at the fence, and a forced door into the facility — to create a qualified incident. It does this by recognizing that a series of events has happened in close proximity, which suggests to the system that something is occurring. It then links those separate events together to create a larger picture.
Based on this, the system then alerts the SOC and identifies this incident as having a higher priority. Because the collaborative decision management system can also send the associated video feeds with the alarm, operators don’t have to search through hundreds or even thousands of other camera feeds to view the activity. This improves safety and security by allowing operators to prioritize their responses with confidence and deal with incidents that require immediate investigation in the appropriate time frame.
Helping security operators perform their daily tasks effectively and efficiently benefits us all. When a SOC’s collaborative decision management system can create qualified incidents, it helps personnel focus on what’s really important — keeping us safe and secure.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!









