How Cybersecurity Can Best Support the Digital Enterprise
As companies digitize businesses and automate operations, cyber risks proliferate; here is how the cybersecurity organization can support a secure digital agenda.

Two consistent and related themes in enterprise technology have emerged in recent years, both involving rapid and dramatic change. One is the rise of the digital enterprise across sectors and internationally. The second is the need for IT to react quickly and aggressively develop innovations to meet the enterprise’s digital aspirations. Exhibit 1 presents a “digitization index”—the results of research on the progress of enterprise digitization within companies, encompassing sectors, assets, and operations.
As IT organizations seek to do this, however, many face significant cybersecurity challenges. At company after company, fundamental tensions arise between the business’s need to digitize and cybersecurity’s responsibility to protect the organization, its employees and its customers, within existing cyber operating models and practices.
Exhibit 1

If cybersecurity teams are to avoid becoming a barrier to digitization and instead become its enablers, they must transform their capabilities along three dimensions. They must improve risk management, applying quantitative risk analytics. They must build cybersecurity directly into the business’s value chain. And they must support the next generation of enterprise technology platforms, which include innovations like agile development, robotics, and cloud-based operating models.
Cybersecurity’s Role in Digitization
Every aspect of the digital enterprise has important cybersecurity implications. Here are just a few examples. As companies seek to create more digital customer experiences, they need to determine how to align their teams that manage fraud prevention, security, and product development so they can design controls, such as authentication, and create experiences that are both convenient and secure. As companies adopt massive data analytics, they must determine how to identify risks created by data sets that integrate many types of incredibly sensitive customer information. They must also incorporate security controls into analytics solutions that may not use a formal software development methodology. As companies apply robotic process automation (RPA), they must manage bot credentials effectively, and make sure that “boundary cases”—cases with unexpected or unusual factors, or inputs that are outside normal limits—do not introduce security risks.
Likewise, as companies build application programming interfaces (APIs) for external customers, they must determine how to identify vulnerabilities created by interactions between many APIs and services, and they must build and enforce standards for appropriate developer access. They must continue to maintain rigor in application security as they transition from waterfall to agile application development.
challenges with existing cybersecurity models
At most companies, chief information officers (CIOs), chief information security officers (CISOs), and their teams have sought to establish cybersecurity as an enterprise-grade service. What does that mean? They have consolidated cybersecurity-related activities into one or a few organizations. They have tried to identify risks and compare them to enterprise-wide risk appetites to understand gaps and make better decisions about closing them. They have created enterprise-wide policies and supported them with standards. They have established governance as a counterweight to the tendency of development teams to prioritize time-to-market and cost over risk and security. They have built security service offerings that require development teams to create a ticket requesting service from a central group before they can get a vulnerability scan or a penetration test.
All these actions have proven absolutely necessary to the security of the organization. Without them, cybersecurity breaches occur more frequently and often with more severe consequences. The needed actions, however, exist in tension with the emerging digital enterprise model, the outcome of an end-to-end digital transformation, from the customer interface through the back-office processes. As companies seek to use public cloud services, they often find that security is the “long pole in the tent”—the most intractable part of the problem of standing applications on public cloud infrastructure.
At one financial institution, development teams were frustrated with the long period needed by security to validate and approve incremental items in their cloud service provider’s catalog for production usage. Developers at other companies have puzzled over the fact that they can spin up a server in minutes but must wait weeks for the vulnerability scan required to promote their application to production. Everywhere IT organizations are finding that existing security models do not run at “cloud speed” and do not provide enough specialized support to developers on issues like analytics, RPA and APIs (Exhibit 2).
Exhibit 2
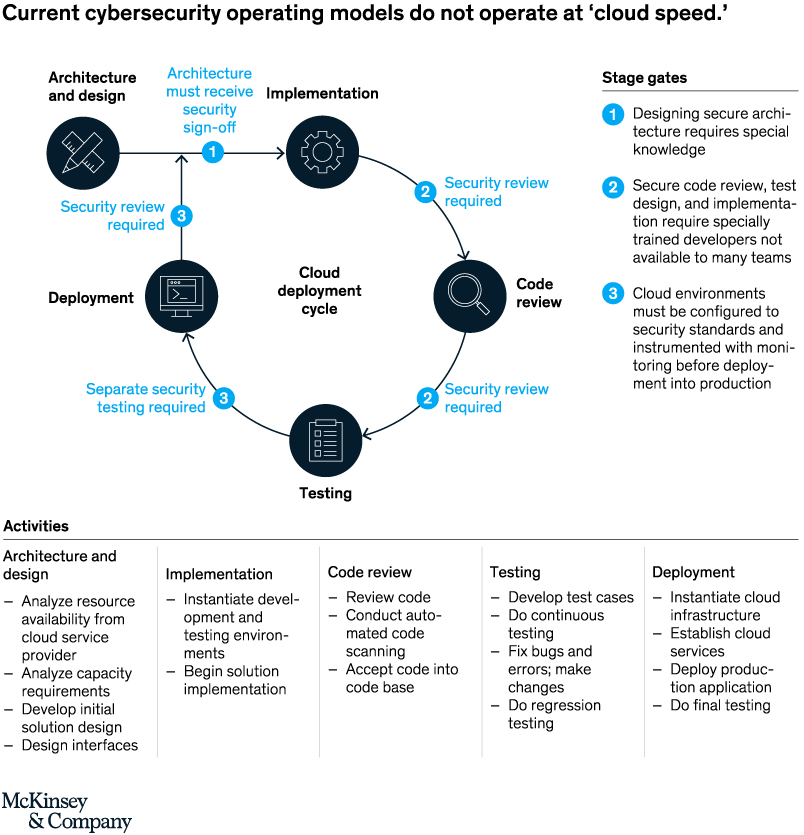
The misalignment between development and cybersecurity teams leads to missed business opportunities, as new capabilities are delayed in reaching the market. In some cases, the pressure to close the gap has caused increased vulnerability, as development teams bend rules to work around security policies and standards.
Cybersecurity for the Digital Enterprise
In response to aggressive digitization, some of the world’s most sophisticated cybersecurity functions are starting to transform their capabilities along the three dimensions we described: using quantitative risk analytics for decision-making; building cybersecurity into the business value chain, and enabling the new technology operating platforms that combine many innovations, such as agile approaches, robotics, cloud, and “DevOps”: software development and IT operations that in combination shorten development times and deliver new features, fixes, and updates aligned with the business.
Using quantitative risk analytics for decision-making
At the core of cybersecurity are decisions about which information risks to accept and how to mitigate them. Traditionally, CISOs and their business partners have made cyber risk management decisions using a combination of experience, intuition, judgment and qualitative analysis. In today’s digital enterprises however, the number of assets and processes to protect, and the decreasing practicality and efficacy of one-size-fits-all protections, have dramatically reduced the applicability of traditional decision-making processes and heuristics.
In response, companies are starting to strengthen their business and technology environments with quantitative risk analytics so they can make better, fact-based decisions. This has many aspects. It includes sophisticated employee and contractor segmentation as well as behavioral analysis to identify signs of possible insider threats, such as suspicious patterns of email activity. It also includes risk-based authentication that considers metadata—such as user location and recent access activity—to determine whether to grant access to critical systems. Ultimately, companies will start to use management dashboards that tie together business assets, threat intelligence, vulnerabilities, and potential mitigation to help senior executives make the best cybersecurity investments. They will be able to focus those investments on areas of the business that will yield the most protection with the least disruption and cost.
Building cybersecurity into the business value chain
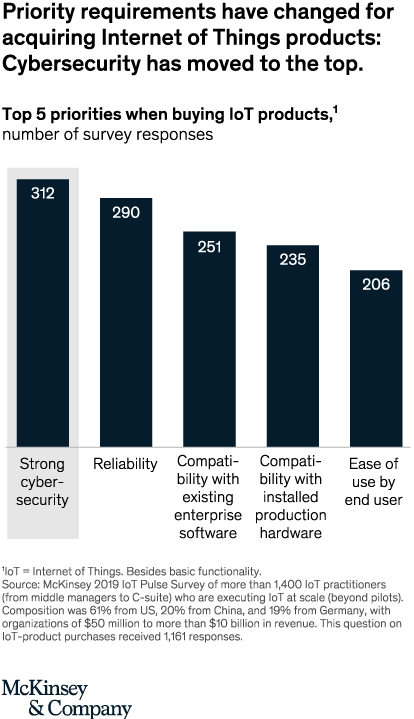
No institution is an island when it comes to cybersecurity. Every company of any complexity exchanges sensitive data and interconnects networks with customers, suppliers, and other business partners. As a result, cybersecurity related questions of trust (and the burden of mitigating protections) have become central to value chains in many sectors. For example, CISOs for pharmacy benefit managers and health insurers are having to spend significant time figuring out how to protect their customers’ data, and then explaining it to those customers. Likewise, cybersecurity is absolutely critical to how companies make decisions about procuring group health or business insurance, prime brokerage, and many other services. It is the single most important factor companies consider when purchasing IoT products (Exhibit 3).
Exhibit 3
Leading companies are starting to build cybersecurity into their customer relationships, production processes, and supplier interactions. Some of their tactics include:
- Using design thinking to build secure and convenient on-line customer experiences. For example, one bank allowed customers to customize their security controls, choosing simpler passwords if they agreed to two-factor authorization.
- Educating customers about how to interact in a safe and secure way. One bank has a senior executive whose job it is to travel the world teaching high-net-worth customers and family offices how to prevent their accounts from being compromised.
- Analyzing security surveys to understand what enterprise customers expect and creating knowledge bases so that sales teams can respond to customer security inquiries during negotiations with minimum friction. For instance, one (SaaS) software provider found that its customers insisted on having particularly strong data-loss prevention (DLP) provisions.
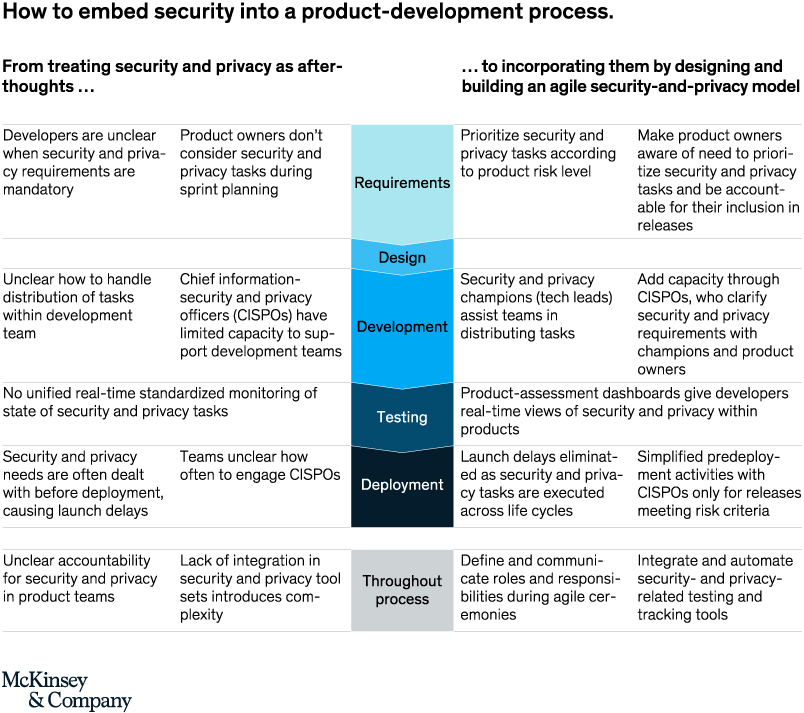
- Treating cybersecurity as a core feature of product design, for instance, what a hospital network would have to do integrate a new operating room device into its broader security environment. Exhibit 4 presents an example of how security is embedded in a product development process.
Exhibit 4
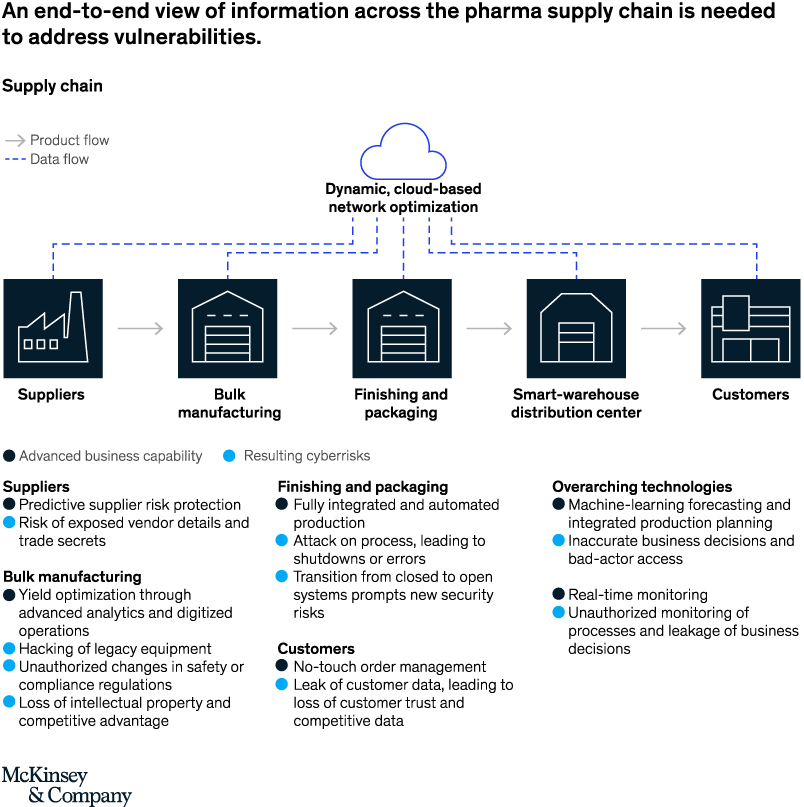
- Taking a seamless view across traditional information security and operational technology security in order eliminate vulnerabilities. One auto parts supplier found that the system holding the master version of some of its firmware could serve as an attack vector to the fuel injection systems it manufactured. With that knowledge it was able to put additional protections in place. Pharma companies have found that an end-to-end view of information protection across their supply chain was needed to address certain key vulnerabilities (Exhibit 5.)
- Using threat intelligence to interrogate supplier technology networks externally and assess risk of compromise.
Exhibit 5
Done in concert, these actions yield benefits. They enhance customer trust, accelerating their adoption of digital channels. They reduce the risk of customers or employees trying to circumvent security controls. They reduce friction and delays as suppliers and customers negotiate liability and responsibility for information risks. They build security intrinsically into customer-facing and operational processes, reducing the “deadweight loss” associated with security protections.
Enabling an agile, cloud-based operating platform enhanced by DevOps
Many companies seem to be trying to change everything about IT operations. They are replacing traditional software development processes with agile methodologies. They are repatriating engineering talent from vendors, and giving developers self-service access to infrastructure. Some are getting rid of their data centers altogether as they leverage cloud services. All of this is being done to make technology fast and scalable enough to support the enterprise’s digital aspirations. In turn, putting a modern technology model in place requires a far more flexible, responsive, and agile cybersecurity operating model. Key tenets of this model include:
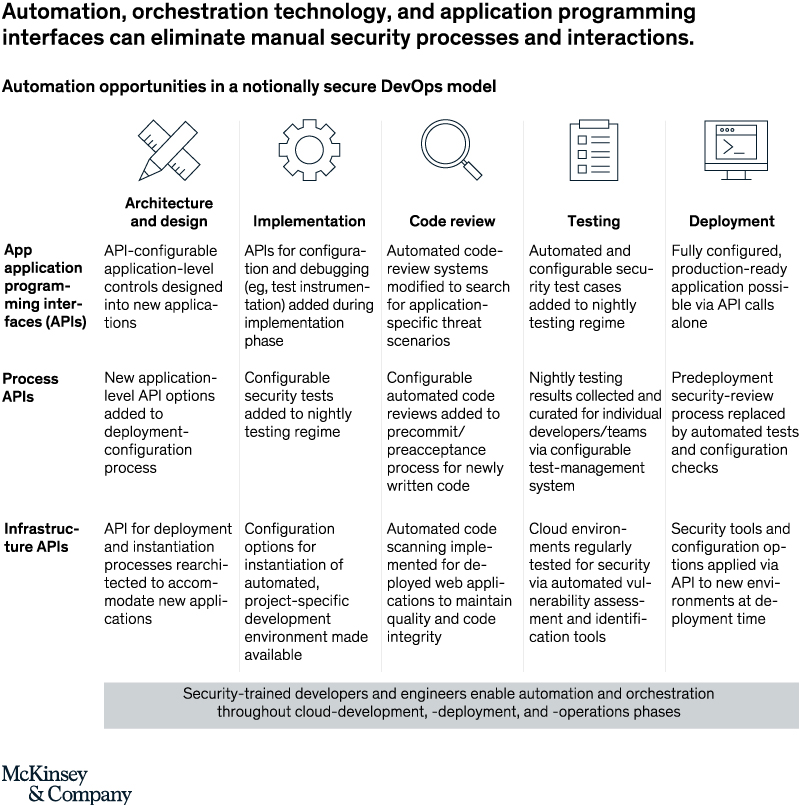
- Moving from ticket-based interfaces to API for security services. This requires automating every possible interaction and integrating cybersecurity into the software-development toolchain. That will allow development teams to perform vulnerability scans, adjust DLP rules, set up application security, and connect to identify and gain access to management services via APIs (Exhibit 6).
Exhibit 6
- Organizing security teams into agile (scrum or scrumban) teams managing developer-recognizable services, such as identity and access management (IAM) or DLP. Also, recruiting development team leaders to serve as product owners for security services can help, just as business managers are product owners for customer journeys and customer-oriented services.
- Tightly integrating security into enterprise end-user services, so that employees and contractors can easily obtain productivity and collaboration tools via an intuitive Amazon-like portal.
- Building a cloud-native security model that ensures developers can access cloud services instantly and seamlessly within certain guardrails.
- Collaborating with infrastructure and architecture teams to build required security services into standardized solutions for massive analytics and RPA.
- Shifting the talent model to incorporate those with “E-shaped” skills: cybersecurity professionals with several areas of deep knowledge, such as in integrative problem solving, automation, and development as well as security technologies.
Taken together these actions will eliminate roadblocks to building digital technology operating models and platforms. Perhaps more importantly, they can ensure that new digital platforms are inherently secure, allowing their adoption to actually reduce risk for the enterprise as a whole.
Case example: How a large biopharma company built cybersecurity capabilities to enable a digital enterprise.
The company had recently concluded a major investment program to enhance its foundational cybersecurity capabilities, dramatically reducing its risk profile. However, the business strategy began to evolve in new ways, with expanding on-line consumer relationships, digitally enabled products, enhanced supply-chain automation, and massive use of analytics. The company now needed new cybersecurity capabilities that would both address new business risks and facilitate business and technology innovation.
To get started, the cybersecurity team engaged a broad set of business partners, capturing current and planned strategic initiatives. It then mapped out the new risks that these initiatives would create and the ways in which cybersecurity protections might slow or block the capture of business opportunities. At the same time, the cybersecurity team looked a broad set of emerging practices and techniques from the pharma industry and other sectors, including on-line services, banking, and advanced manufacturing. Based on all this, it developed an overarching vision for how cybersecurity could protect and enable the company’s digital agenda, and it prioritized 25 initiatives. Some of the most important were:
- Collaborating with the commercial team to build patient trust by designing security into on-line patient journeys
- Collaborating with the manufacturing team to enhance transparency into configuration of plant assets
- Collaborating with the broader technology team to create the APIs and the template to ensure secure configuration of systems running in the public cloud
- Dramatically expanding automation of the security environment to reduce time lags and frustrations developers and users experienced when interacting with the cybersecurity team.
The cybersecurity team then used its vision and initiatives to articulate to senior management how it could enable the company’s digital business strategy, and the support and assistance it would require from other organizations to do so.
□ □ □
With digitization, analytics, RPA, agile, DevOps and cloud, it is clear that enterprise IT is evolving rapidly, and in exciting and value-creating ways. This evolution naturally creates tension with existing cybersecurity operating models. For organizations to overcome the tension, they will need to apply quantitative risk analytics for decision-making, create a secure business value chain, and enable an operating platform that encompasses the latest innovations. These actions will require significant adaptation from cybersecurity organizations. Many of these organizations are still in the early stages of this journey. As they continue, they will become more and more capable of protecting the company while supporting the innovative goals of the business and IT.
This article originally ran in Today’s Cybersecurity Leader, a monthly cybersecurity-focused eNewsletter for security end users, brought to you by Security Magazine. Subscribe here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!









