Most Organizations Frustrated with SOC's Cybersecurity Effectiveness
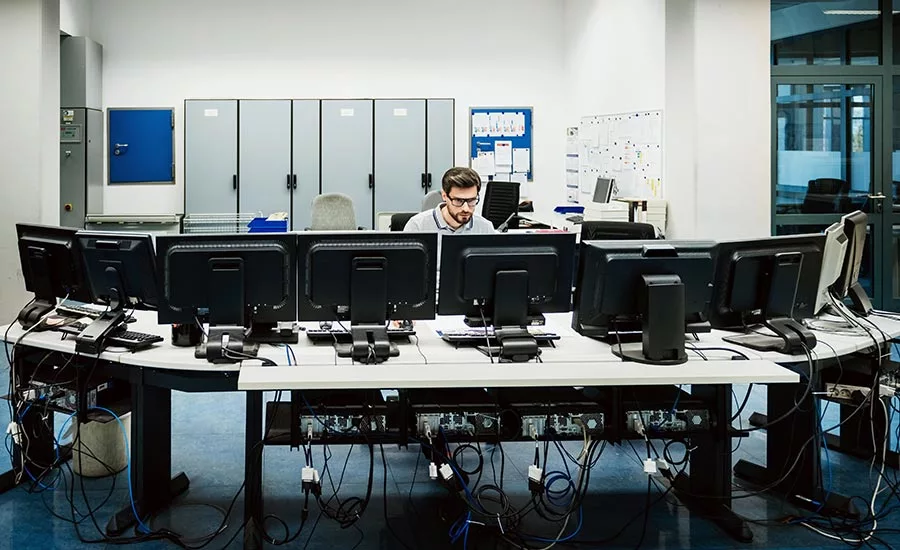
More than half of organizations (53 percent) rate their Security Operation Center’s (SOC) ability to gather evidence, investigate and find the source of threats as ineffective, according to the Improving the Effectiveness of the Security Operations Center study.
The top barrier to SOC success, according to 65 percent of respondents, is the lack of visibility into the IT security infrastructure and the top reason for SOC ineffectiveness, according to 69 percent, is lack of visibility into network traffic. On average, less than one-third of the IT security budget is used to fund the SOC and only four percent of respondents say more than 50 percent of the cybersecurity budget will be allocated to the SOC.
Additional key findings from the report include:
- Organizations are shifting to the cloud. Fifty-three percent of respondents say what best defines the IT infrastructure that houses their SOC is mostly cloud (29 percent) or a combination of cloud and on-premises. Forty-seven percent of respondents say it is onpremise.
- The majority of respondents (51 percent) say their companies invest in threat intelligence feeds. Of these organizations, 54 percent of respondents say the threat intelligence feeds combine open source and paid feeds. Sixty percent of respondents in organizations that invest in threat intelligence feeds develop custom feeds based on a technology profile. Twenty-eight percent of respondents say their organizations do not develop custom feeds.
- The exploits most commonly identified by the SOC are malware attacks, exploits of existing or known vulnerabilities, spear phishing and malicious insiders.
- Monitored or managed firewalls and intrusion prevention systems and intrusion detection systems are most often deployed within the SOC environment. Other services include managed vulnerability scanning of networks, servers, databases or applications and monitored or managed multifunction firewalls or unified threat management (UTM) technology.
- Organizations outsource based on their size and maturity level. Smaller organizations tend to outsource because of the inability to have an expert in-house SOC team and the necessary technologies. Further, these organizations outsource to improve the efficiencies and costeffectiveness of their cybersecurity strategy. As size and maturity increases, outsourcing the SOC decreases.
- The focus of most respondents is to implement technologies (63 percent), patch vulnerabilities (61 percent) and investigate threats (56 percent). They are less involved in setting priorities and determining strategy.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






