Financial Services in the Ransomware Crosshairs: Why and What to Do
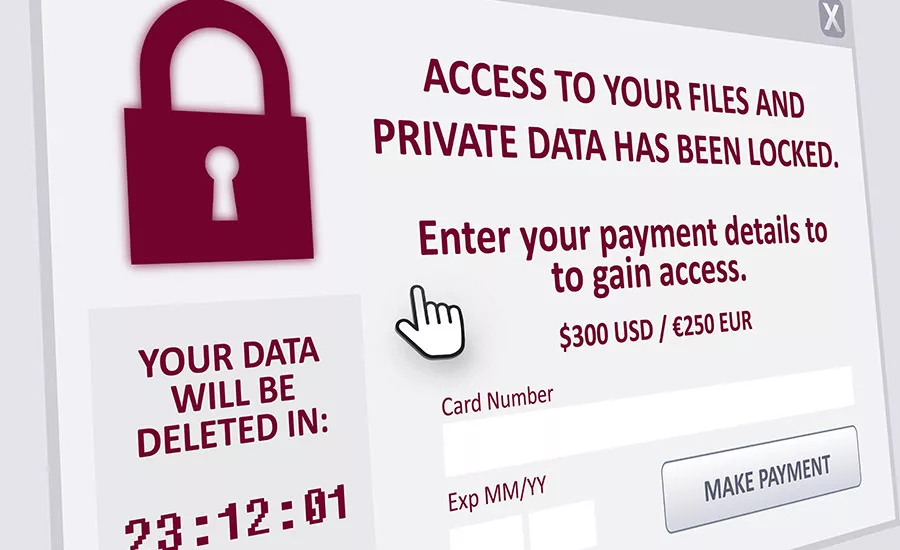
Cybercriminals are leveraging ransomware threats to extort big money from organizations of all sizes in every industry, but financial services organizations are one of today’s primary targets.
It is non-negotiable for financial services companies to maintain the privacy of theirs customers and the security of their confidential data. If a bank or credit union is hit with a ransomware attack, significant backlash is undoubtedly going to ensue – especially if customer data is held ransom for a significant amount of time.
Why financial services organizations?
Here are a few key reasons why financial services is being heavily targeted:
1. They store a lot of valuable and confidential customer and corporate data.
2. They tend to have significant cash on hand, and the high cost of downtime – makes them more likely to pay a ransom to get back encrypted data.
3. Their IT security is perceived to be deficient especially within smaller banks and credit unions.
Financial Services companies continue to exhibit effective security, which isn’t surprising considering their continued adoption of security frameworks, such as the NIST Cybersecurity Framework (CSF). Nonetheless, there is still room for improvement with ransomware attacks continuing to be a growing challenge. Effectively combating ransomware requires a well-thought-out combination of technical and cultural measures. This includes:
Training and Awareness
Most ransomware attacks begin with an email containing a malicious link or attachment. Consequently, the single most important measure you can take to reduce the likelihood of a successful attack is to train yourself, staff and partners to practice safe computing and recognize red flags that indicate a potentially malicious email.
Ensure all users understand the following key practices, and maintain awareness with a program of regular reminders:
- Don’t open suspicious emails. Pretty much anything unexpected or out of the ordinary is a potential attack, even if it comes from a trusted source. If possible, contact known senders separately to confirm the email is authentic before opening.
- Learn to spot red flags. Some telltale signs of an attack include:
- Grammar or spelling errors in a supposedly professional email;
- Odd, middle-of-the-night time of sending;
- “Typosquatting,” in which the “From” domain looks legitimate at first glance, but is actually slightly misspelled or has things added – “hacker@bankofarnerica.com,” for example; or
- Buttons and links in the email that connect to unexpected, suspicious URLs. Always check this, by hovering the cursor over the link or button, and checking the URL that appears at the bottom left of your window.
- When in doubt – delete or don’t open.
Train your entire staff to approach email with security in mind. A number of services exist to provide such training, including periodically sending fake phishing emails to staff members and alerting them if they respond unsafely.
Secure Your Network
Effective user training can help stop a lot of attacks, but keeping your network free of ransomware and other advanced malware also requires a combination of effective perimeter filtering, strategically designed network architecture, and the capability to detect and eliminate resident malware that may already be inside your network.
- Prevent threats from entering the network by deploying a firewall along with a comprehensive email security strategy to stop threats.
- Control and segment network access to minimize the spread of threats, in the event that they still get in.
- Clean house. Your infrastructure likely contains a number of latent threats, so all applications and inboxes – whether locally hosted or cloud-based – must be regularly scanned for malicious content and vulnerabilities.
Backup – Your Last, Best Defense Against Ransomware
When a ransomware attack succeeds, your critical files – HR, payroll, customer financial information, strategic planning documents, email records, etc. could all be encrypted, and the only way to obtain the decryption key is to pay a ransom.
But if you have the right backup strategy in place, instead of paying the ransom, you can simply restore your files from the most recent backup – your attackers will have to find someone else to rob.
Automated, cloud-based backup services can provide the greatest security. Reputable vendors offer a variety of very simple and secure backup service options, priced for organizations of any size, and requiring minimal staff time. Advanced solutions can even allow you to spin up a virtual copy of your servers in the cloud, restoring access to your critical files and applications within minutes of an attack or other disaster.
Financial Services IT Security: A Non-Negotiable Requirement
Financial Services organizations like yours are entrusted with the most personal, financial information that people have – not just their social security numbers, but their banking accounts and credit histories.
If that trust is betrayed – if you fail to take the steps necessary to keep that data safe against ransomware and other advanced malware – the cost to your business could extend far beyond paying a ransom. If your reputation for safeguarding customer data is damaged, rebuilding trust can take many years.
No matter how much progress your organization has made in improving IT security, this is no time to rest on your laurels. Those who continue to commit significant resources to implementing effective security will emerge as winners in a competitive environment that is ever more profoundly affected by ransomware and other advanced malware attacks.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





