4 Trends Driving Security Operations Centers
How the SOC Creates Customer Confidence
Today, the need for organizational trust has been amplified by cyber threats that continue to grow in variety, volume and scope. According to the Cisco 2018 Annual Cybersecurity Report, 32 percent of breaches affected more than half of organizations’ systems, up from 15 percent in 2016. Network breaches shake customer confidence, and it’s essential that organizations protect intellectual property, customer records and other critical digital assets. A strong cybersecurity strategy is today’s foundation for creating confidence among partners and customers.
The Security Operations Center Gains Prominence
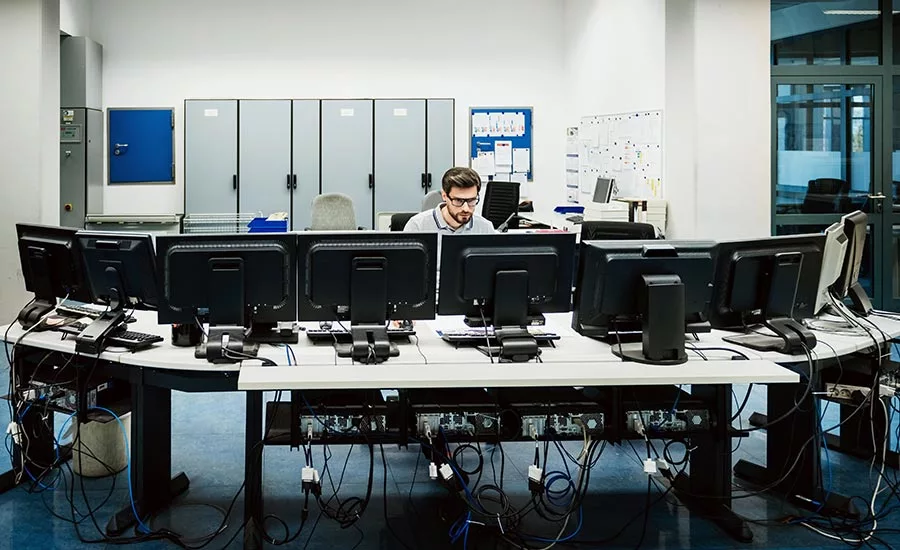
A key factor in establishing trust is the presence of a Security Operations Center (SOC). This is true whether the SOC functions internally or is provided by a third party, such as a managed security service provider (MSSP).
This team monitors, detects, investigates and responds to cyber threats around the clock. The SOC is charged with monitoring and protecting many assets, such as intellectual property, personnel data, business systems and brand integrity. This includes the connected controls found in networked industrial equipment. The SOC assumes overall responsibility for monitoring, assessing and defending against cyberattacks.
SOCs have grown in importance due to four primary trending needs:
- Departmental collaboration: It’s more important than ever that organizations maintain an environment where skilled people with the right tools can react quickly and collaborate to remediate system-wide as well as local problems.
- Cross-functional collaboration: People and cybersecurity tools must work together with other critical IT functions and business operations. These departments align with business objectives and compliance needs for a high-performing operation that is efficient and effective.
- Company-wide coordination and communication: As a security event takes place, it’s essential that there’s a centralized team to communicate with the rest of the organization and ensure efficient resolution. In turn, it’s also important that the organization knows who to turn to in the event of an incident.
- A holistic view: A view of all digital assets and processes that is centralized and real-time makes it possible to detect and fix problems whenever and wherever they occur. Centralization is critical for IoT systems. The sheer number of devices and the likelihood that they are widely dispersed make local monitoring impractical and inconsistent.
As security operations have changed, the associated job roles and responsibilities have evolved as well. Having the right team with the right skills in place is essential to optimizing an organization’s front-line defense.
SOC Member Roles
Within the SOC, there are many roles. While SOC teams are not all the same, these roles typically include:
- Cybersecurity SOC Manager: Manages the SOC personnel, budget, technology and programs, and interfaces with executive-level management, IT management, legal management, compliance management and the rest of the organization.
- Incident Responder: Investigates, evaluates and responds to cyber incidents.
- Forensic Specialist: Finds, gathers, examines and preserves evidence using analytical and investigative techniques.
- Cybersecurity Auditor: Monitors compliance of people, procedures and systems against cybersecurity policies and requirements.
- Cybersecurity Analyst: Identifies, categorizes and escalates cybersecurity events by analyzing information from systems using cyber defense tools.
These individuals work together to identify and respond to cybersecurity incidents in real time.
Building a SOC: A Challenge and an Opportunity
As networks expand and grow in complexity, SOCs are emerging as the enterprise’s front and best line of defense. The SOC is a strategic, risk-reducing asset that strengthens the security of an organization’s systems and data. Building a SOC isn’t as easy as simply hiring new team members, however.
That’s because the cybersecurity industry is facing a significant skills gap; there aren’t enough people right now equipped with the skills to fill open cybersecurity positions. This shortage of talent is one of the biggest cybersecurity challenges the industry is facing. Market intelligence firm Cybersecurity Ventures predicts there will be 3.5 million cybersecurity job openings by 2021.
Having too few people is not the only issue. A series of research reports from leading industry analyst Enterprise Strategy Group indicates that many currently employed cybersecurity professionals are overworked, not managing their careers proactively, and not receiving the proper amount of training to stay ahead of increasingly dangerous and prevalent threats.
Although individuals with skills in security are highly sought after, their skills can be learned and taught to others. That’s why it’s important to hire or train individuals who are willing to engage in continuous learning. Certifications and other expert credentials also help to validate existing security skillsets when hiring externally. Ongoing learning, training and certifications enable organizations to keep the SOC up-to-speed, ultimately building and maintaining customer and partner confidence.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







