Getting the Most from Your Legacy Access Control System
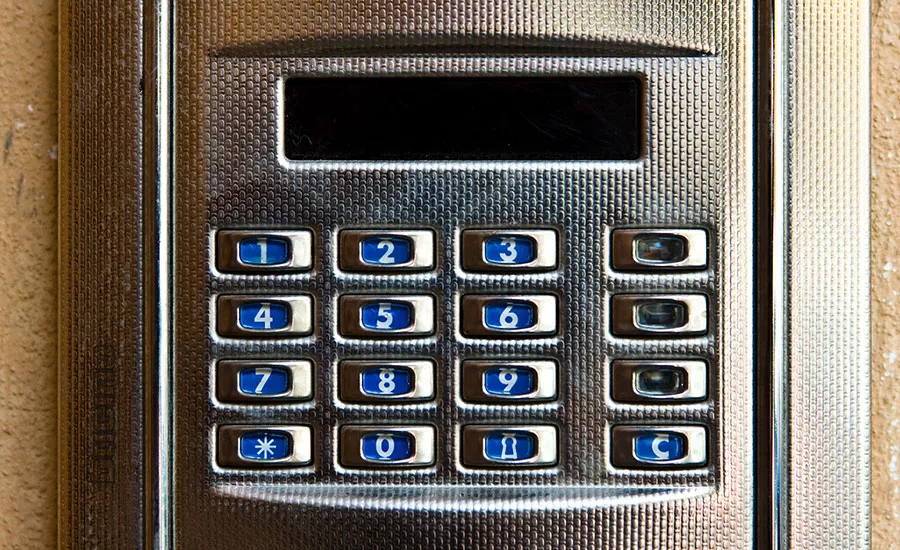
Jupiterimages / PHOTOS.com>> / Getty Images Plus / Via Getty Images
In a constantly evolving business environment, an increasingly popular strategy for organizations to achieve growth and market share is through acquisitions and mergers. Among the many challenges facing these new business situations is standardizing and/or upgrading the physical security systems to ensure enterprise-wide compatibility and efficiency. In many of these organizations, that process begins with the access control systems.
Updating Legacy Systems
Even just a few years ago, a “rip and replace” plan would have been the most feasible to bring uniformity to the enterprise. However, the availability today of best-in-breed access control solutions that enable legacy systems to be upgraded and/or integrated is resolving many of the issues and eliminating the need for an entire system replacement. What makes this solution even more viable is that new software solutions negate the need for concern regarding the brand of legacy hardware or system topography.
New software is the critical system enhancement component, and is by far the easiest component to deal with from an installation perspective. It also provides significant savings relative to equipment and installation costs, resulting in a higher return on investment and lower total cost of ownership.
Legacy systems are typically comprised of a series of controllers that have embedded software to control specific entrances. Essentially, the intelligence in the system is distributed to the access location entry points, with data sent back to a centralized location for system control. To upgrade this system, controllers are replaced and new remote interface cards are installed so that all operations are controlled centrally by an enterprise access control solution. In legacy access control systems that feature centralized architecture, all the system intelligence resides in the software. In most cases, these legacy systems are also most likely running on twisted pair cabling that can be utilized by the new system. This yields extremely high cost-efficiency as only the centralized software is being replaced at the head-end.
Addressing Growth Issues Today and Tomorrow
With new software solutions, even systems that span separate buildings in different locations can be efficiently upgraded – even if they have different hardware providers – by using one or both of the previously described methods. More importantly, disparate systems can be integrated without ripping and replacing costly hardware. The larger the deployments to be upgraded, the larger the incremental savings.
New software also holds the key for future growth of access control. This is especially true as users continue to employ access control systems for business operations beyond security, for example time and attendance or billable hours. Applications might include auto repair centers for accessing tool vending cabinets; verifying time for grounds maintenance crews; behavioral or usage tracking; and so on.
In a specific application, a school in Connecticut was looking for a better way to manage student traffic between a large number of portable classrooms being used while a new facility was constructed. One of the main concerns centered on children using restrooms and other facilities located in the main school building throughout the course of the day. School administrators wanted a way to efficiently track student movements beyond issuing conventional written hall passes. A feature called “Hall Pass” was developed that provides teachers with proximity devices they issue in lieu of conventional hall passes. Through the placement of access readers in the classrooms and at all entrances to the main school building, students are monitored with a predetermined amount of time to walk from their classroom to the building. If a student fails to report in the allocated time period, the system issues a general alert.
New access control and management technologies on the market today promise dramatic improvements in performance and efficiency. It’s to the benefit of both users and system integrators that these new technologies are also capable of maintaining legacy support and providing enhancements to pre-existing systems.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








