Access Control -- Hackers
Hacker Will Expose Potential Flaw in Four Million Hotel Room Locks
Jupiterimages / PHOTOS.com>> / Getty Images Plus / Via Getty Images
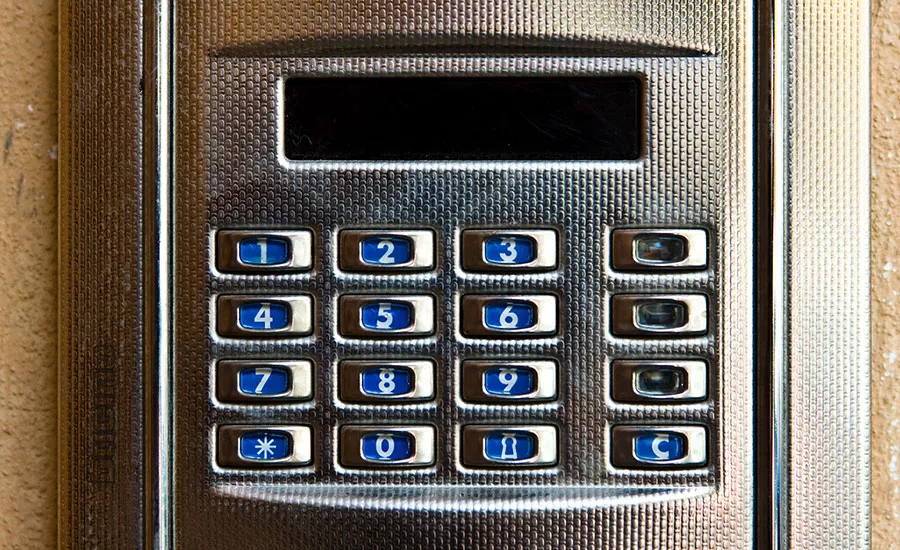
The next time you stay in a hotel room, run your fingers under the keycard lock outside your door. If you find a DC power port there, take note: With a few hacker tricks and a handful of cheap hardware, that tiny round hole might offer access to your room just as completely as your keycard, an article from Forbes says.
At the Black Hat security conference Tuesday evening, a Mozilla software developer and 24-year-old security researcher named Cody Brocious plans to present a pair of vulnerabilities he’s discovered in hotel room locks from the manufacturer Onity, whose devices are installed on the doors of between four and five million hotel rooms around the world according to the company’s figures.
Using an open-source hardware gadget Brocious built for less than $50, he can insert a plug into that DC port and sometimes, albeit unreliably, open the lock in a matter of seconds, Forbes reports.
Testing a standard Onity lock he ordered online, Brocious is able to bypass the card reader and trigger the opening mechanism every time, the article reports. But on three Onity locks installed on real hotel doors he and the Forbes reporter, Andy Greenberg, tested at well-known independent and franchise hotels in New York, results were much more mixed: Only one of the three opened, and even that one only worked on the second try, with Brocious taking a break to tweak his software between tests, the article says.
And even though the method might be unreliable, Brocious says he plans to release all his research in a paper as well as source code through his website following his talk, potentially enabling others to perfect his methods, the article reports.
Brocious’s exploit spoofs a portable programming device that hotel staff use to control a facility’s locks and set which master keys open which doors, Forbes reports.
According to the article: “The system’s vulnerability arises, Brocious says, from the fact that every lock’s memory is entirely exposed to whatever device attempts to read it through that port. Though each lock has a cryptographic key that’s required to trigger its “open” mechanism, that string of data is also stored in the lock’s memory, like a spare key hidden under the welcome mat. So it can be immediately accessed by Brocious’s own spoofed portable device and used to open the door a fraction of a second later.”
Brocious doesn’t plan to complete the development and debugging of the technique himself, due to what he says are time constraints and concerns about what a universally effective exploit would mean for the security of millions of hotel guests, according to Forbes. But he believes that with more experimentation, someone could easily access a significant fraction of hotel rooms in the U.S. without leaving a trace.
The ability to access the devices’ memory is just one of the two vulnerabilities Brocious says he found in the locks. According to the Forbes article, he says the company also uses a weak encryption scheme that allows him to derive the “site code” – a unique numerical key for every facility – from two cards encoded one after another for the same room. By reading the encrypted data off of two cards and testing thousands of potential site codes against both cards until the decoded data displays a predictable interval between the two, he can find the site code and use it to create more card keys with a magnetizing device.
But given that he can only create more cards for the same room as the two keys he’s been issued, that security flaw represents a fairly low risk compared with the ability to open any door arbitrarily, the article says.
In a move that may dismay security practitioners, Brocious never contacted Onity or its parent company United Technologies Corporation to tell the firm about its security flaws, and doesn’t plan to ahead of his talk, Forbes reports.
But he says that’s because there’s little the company could do: the locks can’t be simply upgraded with new firmware to fix the problem. New circuit boards will have to be installed in every affected lock – a logistical nightmare if millions of locks prove to be vulnerable.
“I didn’t want to delay putting this out there any further than I had to. I see no path to mitigate this from Onity’s side,” he says in the article. “The best way to help hotels at this point is educate them about this, not to go through Onity and delay getting the information out longer than I had to.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




