The Urge to Merge: Integrating Access Control
Like chocolate and peanut butter, access control and biometrics go together.
"Biometrics is very powerful because it brings access control down to a person," says Tom Colatosti, president and CEO of Viisage Technology, Littleton, Mass.
Identification is important when it comes to access control. Some traditional technologies do not necessarily provide the best security.
"When using a swipe card or password, all you are really saying is that the card or the password belongs in the building. With biometrics, you can say this person belongs in the building," says Colatosti.
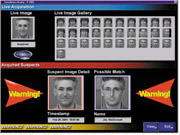
One of the emerging biometric technologies is facial recognition. And, facial recognition is easily integratable with other security systems, such as CCTV.
"Facial recognition easily lends itself to existing infrastructures. Many buildings have surveillance cameras, and facial recognition provides a powerful compatibility," says Colatosti.
"It is a very intuitive biometric form because it lends itself to something recognizable. And biometrics adds a dimension of convenience. People can forget their badges and keys or passwords, but they don't forget their face," says Colatosti.
With access control, there is always the question: "is the right person getting in?" Colatosti notes, however, that you should also ask, "is only the right person getting in?"
"There is often times the problem of 'tailgating'. Someone can easily get through a door as long as an authorize use r swipes their card or enters their code. The tailgater simply waits and follows them in."
Tracking Assets
Asset tracking is another technology on its way to being integrated with access control. With this type of technology, you can monitor not only who is coming and going, but also what they have with them."When we talk about asset tracking, it is important to note that people are assets, too," says Doug Karp, sr. director of operations and strategic marketing, Checkpoint Systems, Thorofare, NJ. "With the marriage of access control and RFID technology, there is total asset visibility."
One of the advantages of this type of technology is that it is east to upgrade. For example, if you already have RFID technology, you can add the access control, and vice versa. Potential markets that can benefit are pharmaceutical companies, government agencies, and any other company with strict compliance issues.
Will this be a difficult technology to implement? According to Karp, the answer is no.
"It's really about creating a solution-oriented product. The technology is relatively plug and play. There is always a learning curve with new technology, but I do not think it will be substantial in this instance. The difficult thing is getting people to think outside the box, and move away from what they are used to. It just takes time and experience," he says.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





