Product Spotlight on Analytics

Analytics is what holds most security systems together, allowing all of the gathered data to be organized and properly stored. Security magazine highlights a few analytics security products.

Crisis24
Combine Digital and Human Analysis
Crisis24 Horizon is a risk management platform to provide a picture of risk exposure. The platform processes a diverse range of feeds, complemented by a team of human analysts. The platform allows users to view events or risks at a global level, or to focus on specific local alerts such as street corners or specific addresses. The system is supported by global operations centers which offer intelligence from over 180 analysts around the world. Image courtesy of Crisis24
Find out more at CRISIS24.GARDA.COM
CrowdStrike
Increases Visibility and Improves Response Times
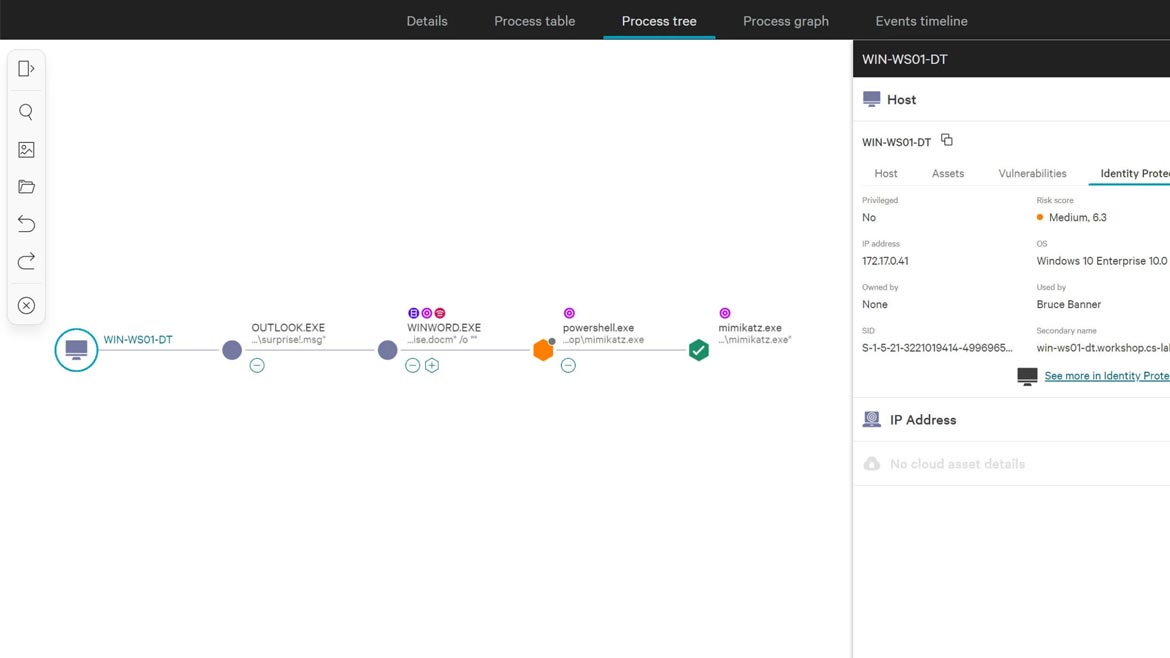
CrowdStrike’s platform allows users to deploy a single agent for immediate value. Users can gain full visibility and protection across attack paths, boosting response times and stopping modern adversaries. With unified visibility across cloud, endpoints and identities, users can correlate and detect cross-domain attacks to stop adversaries from moving laterally across your environments. Get complete visibility and real-time protection across traditional Active Directory (AD) and cloud identity providers such as Entra ID and Okta, empowered with industry-leading threat intelligence. Image courtesy of CrowdStrike
Find out more at CROWDSTRIKE.COM

Verkada
Tracks Individuals Through a Building
Verkada History Player Search allows users to seamlessly pull past footage and track an individual’s movement across all cameras in their organization. With a single click, History Player Search automatically analyzes video footage to generate a chronological playback of that person’s movements, making it easy to find specific moments, jump to key events, and archive or share clips as part of a comprehensive Incident Report. Image courtesy of Verkada
Find out more at VERDAKA.COM

Forcepoint
Quickly Identifies Sensitive Data
Forcepoint Data Security Cloud is an AI-powered data security platform uniting visibility and control of data everywhere it’s created, stored or moved. Driven by AI Mesh, the single cloud-delivered platform unifies Data Security Posture Management (DSPM), Data Detection and Response (DDR), Enterprise DLP, SaaS Security, Web Security, and Email Security, to deliver full-spectrum data security. This enables enterprise and government customers to immediately gain an understanding of their proprietary and sensitive data, dynamically adapt to risk in real time, and simplify management with automated, behavior-aware protection. Image courtesy of Forcepoint
Find out more at FORCEPOINT.COM
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






