Product spotlight on analytics

Whether it’s video surveillance or cybersecurity incidents, security leaders rely on analytics to keep their organizations secure.
Security magazine highlights a variety of analytics platforms focusing on video surveillance, natural disasters and cyberattacks.
 Bosch
Bosch
Automate building security and review events
Bosch’s VideoView+ is a cloud-enabled video management application, which enables users to view live and recorded video and manage events when an incident occurs. The application is built for various types of situations and markets, including users needing the flexibility to surveil multiple sites remotely. Instant event notifications enable users to investigate issues via a desktop computer, laptop, mobile phone or tablet. Event clips, including a video analytics overlay, can be revisited with a timeline of events. Image courtesy of Bosch
FIND OUT MORE AT BOSCH.COM
Broadcom
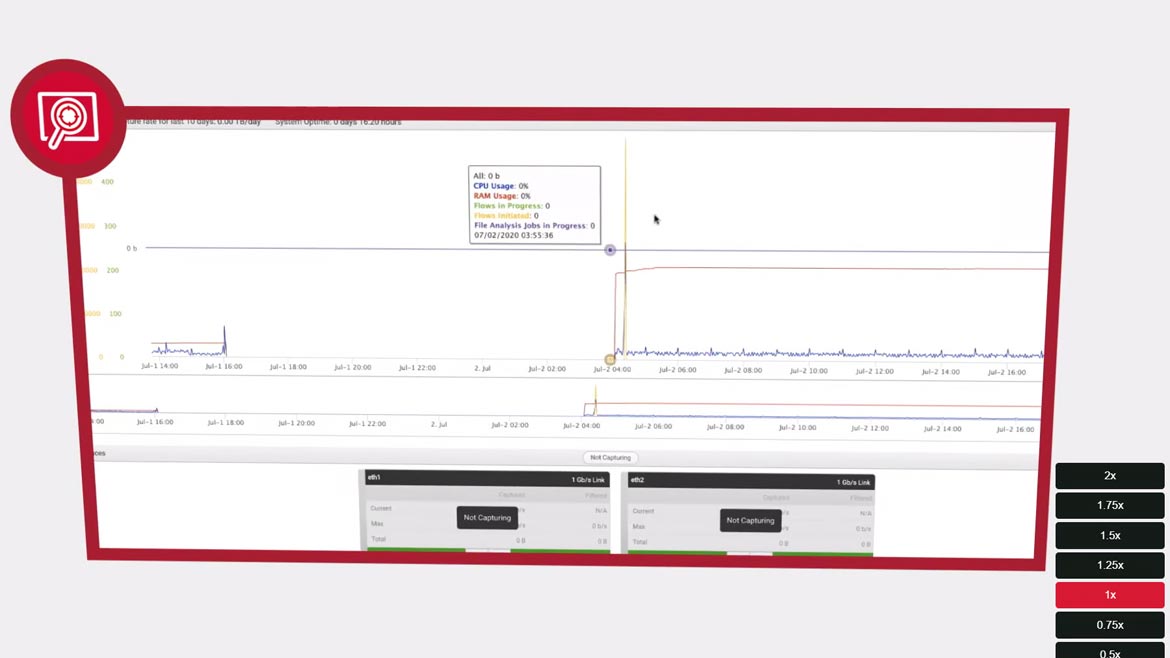
Analyze current and past events
Symantec Security Analytics delivers the network visibility and forensics required to conduct comprehensive real-time and retrospective analysis, enabling security leaders to react to security issues to protect an organization’s workforce, fortify the network, and improve security processes. The solution can capture, inspect, index, classify and enrich all network traffic, which is stored in a file system for analysis, retrieval and complete reconstruction to support all incident response and remediation activities. Appliance-based, the solution can be deployed anywhere in the network. Image courtesy of Broadcom
FIND OUT MORE AT BROADCOM.COM
Crisis24
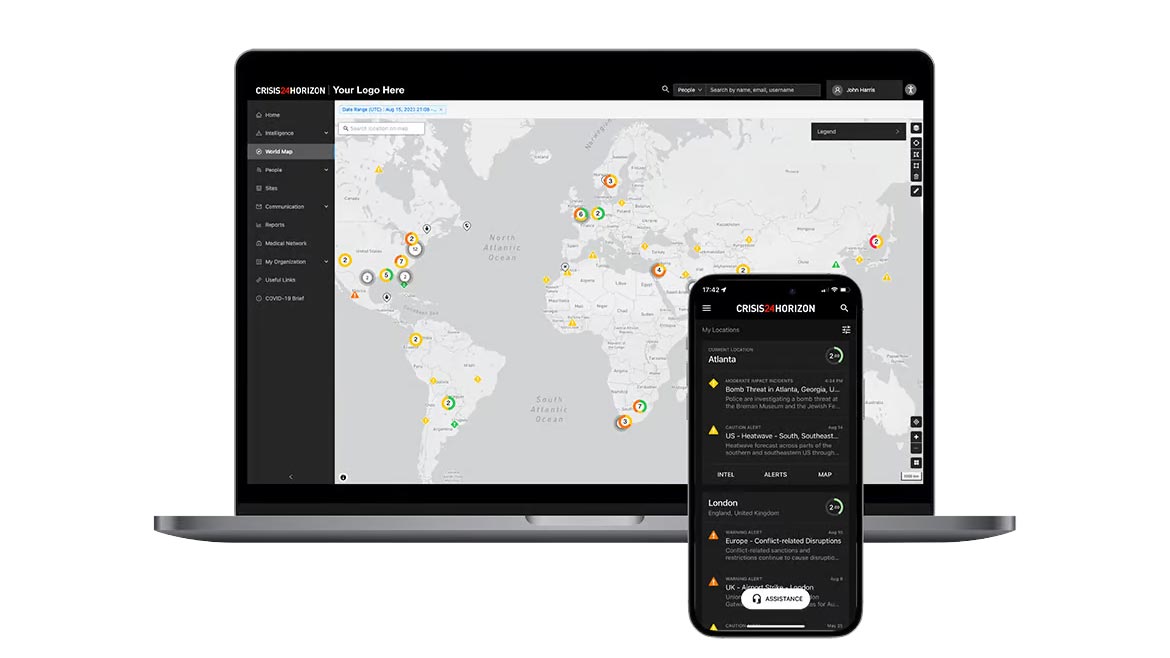
Manage global data and assess risk
Crisis24 Horizon is a risk management platform to provide a picture of risk exposure. The platform processes a diverse range of feeds, complemented by a team of human analysts. The platform allows users to view events or risks at a global level, or to focus on specific local alerts such as street corners or specific addresses. The system is supported by global operations centers which offer intelligence from over 180 analysts around the world. Image courtesy of Crisis24
FIND OUT MORE AT CRISIS24.GARDA.COM
Dynatrace
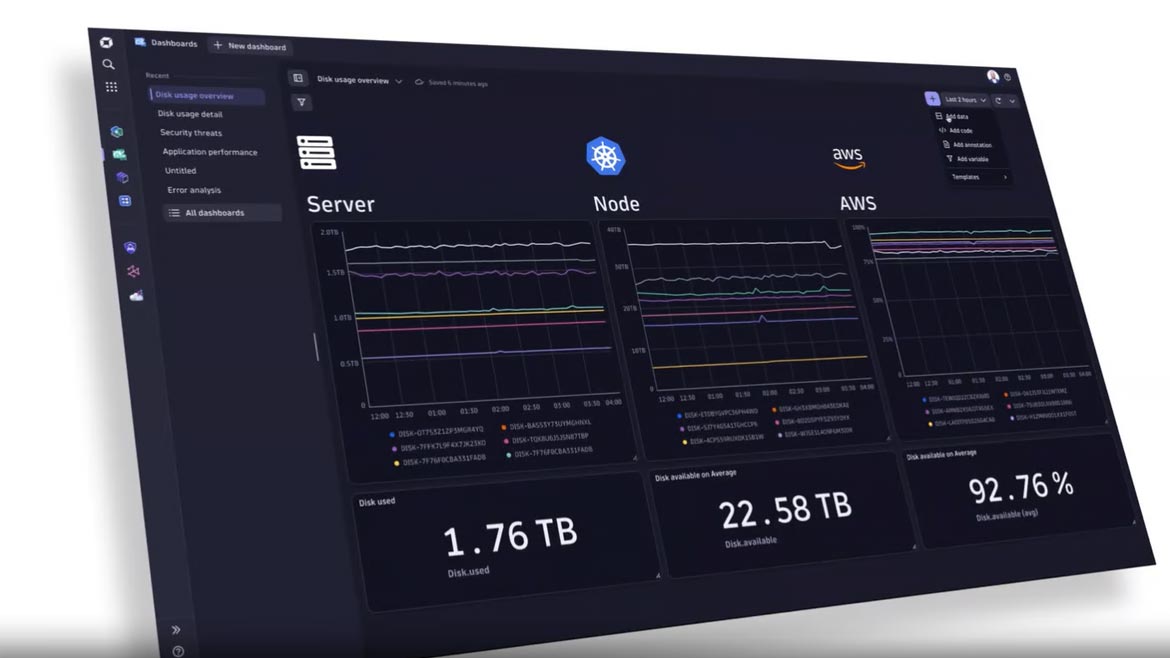
Use AI to monitor cyber threats
Dynatrace Security Analytics leverages Davis AI, which combines predictive and causal artificial intelligence (AI) techniques to provide security analysts with the answers and data context they need to prioritize and investigate threats and vulnerabilities. In addition, Security Analytics can create automations and workflows that analysts can use to assess the impact of an attack, find the indicators of compromise (IOCs), or automatically trigger a response. Security analysts can use the platform to defend against emerging cyber threats proactively. Image courtesy of Dynatrace
FIND OUT MORE AT DYNATRACE.COM
Eagle Eye Networks
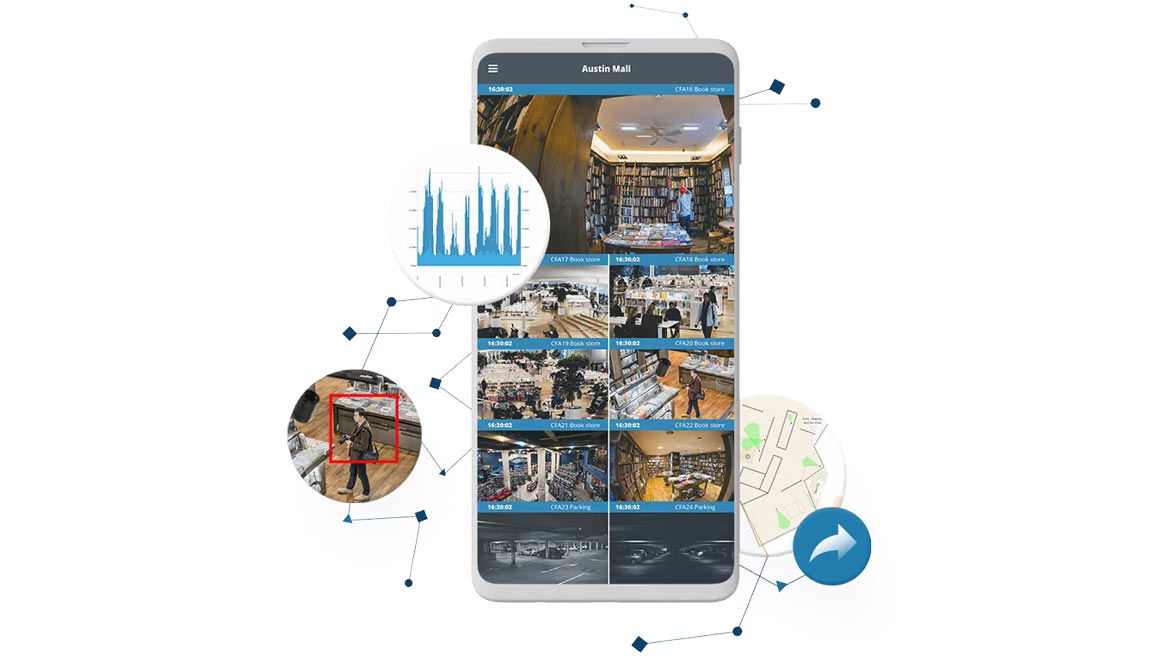
Collect and manage video surveillance data
Version three of the Eagle Eye Video API Platform is used by Eagle Eye developers, resellers, and technology partners worldwide. The platform provides cloud-based AI and video analytics. The platform included analysis from external experts alongside existing data. The platform has been used in the hospitality industry for surveillance and management, along with enterprise security. Image courtesy of Eagle Eye Networks
FIND OUT MORE AT EEN.COM
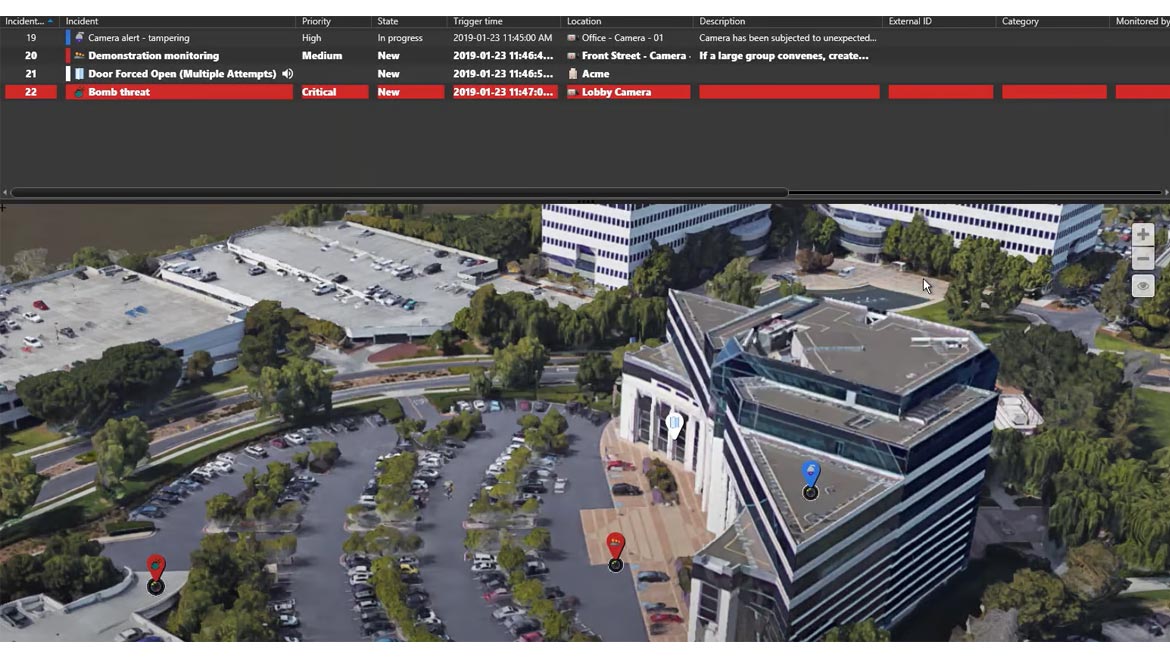
Genetec
Balance incident response and investigations
Genetec has announced a new integration between the Genetec Mission Control decision management system and the Genetec Clearance digital evidence management solution. This integration enables users to move from incident response to investigation from within a single interface. Security teams in organizations such as hospitals, banks and utilities often handle a high volume of events, and frequently need to share video evidence and incident details with internal departments as well as with law enforcement agencies, attorneys and insurance providers. This information includes video evidence as well as details of events as they unfolded and what courses of action were taken during the incident. Image courtesy of Genetec
FIND OUT MORE AT GENETEC.COM

Granica
Review how data is stored in the cloud
Chronicle is a generative AI-powered Software as a Service (SaaS) offering that provides visibility and analytics into how data is accessed in cloud object stores. Chronicle provides analytics and observability for data with a deep focus on access. Chronicle is designed to provide data at-rest and access visibility into cloud object storage platforms, via an AI-powered interface. The solution allows users to determine potential rogue/shadow access, determine if access is compliant (e.g., with GDPR), assess and minimize risk of breach or data loss, and maintain audit trails. Image courtesy of Granica
FIND OUT MORE AT GRANICA.AI

Lanner Electronics/Hailo
Process and streamline video data
The Lanner Falcon Lite PCIe AI Acceleration Card is a scalable intelligent video analytics application. The platform is utilized in smart retail, Industry 4.0 and intelligent transportation. With high-density AI processors, the solution can accommodate two, three and four Hailo-8 AI processors. Designed to support x4, x8, and x16 PCIe interfaces in both commercial and industrial settings, the Falcon Lite AI Accelerator Card provides enables legacy devices to run video-intensive, mission-critical applications such as video analytics, traffic management and access control. Image courtesy of Lanner and Hailo
FIND OUT MORE AT LANNERINC.COM
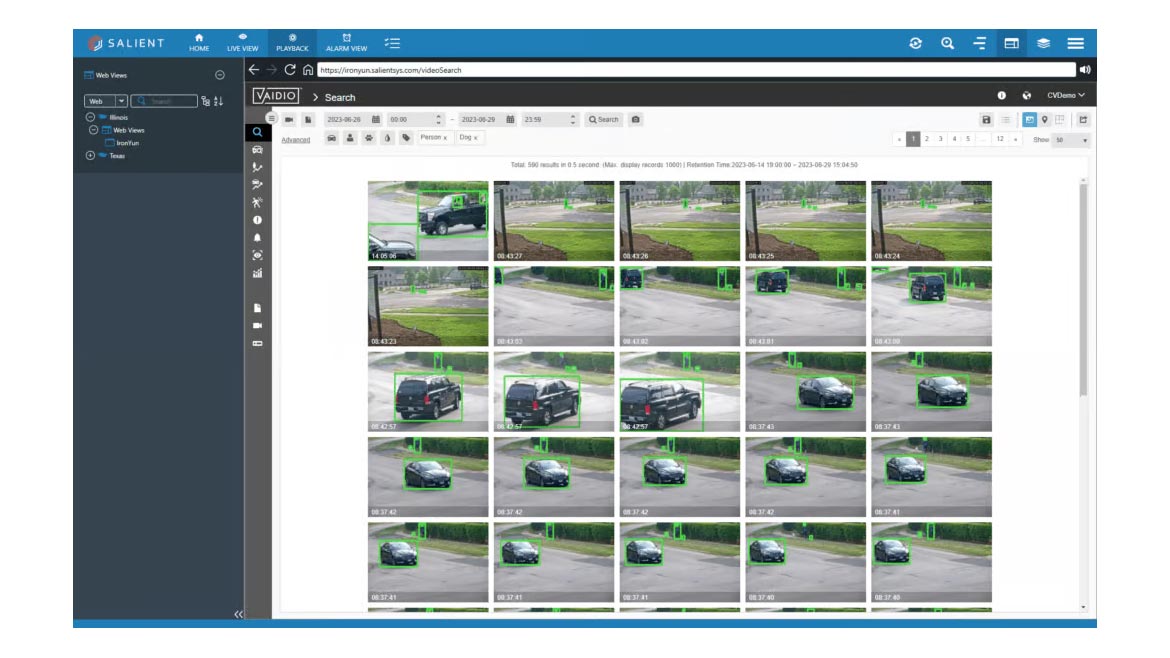
Salient Systems
Recognize faces and alert security leaders
Vaidio AI delivers a suite of people, vehicle, facial and object analytics that work with any camera or video source and integrates into the CompleteView video management system (VMS). Security operators can benefit from real-time alerts and notifications, which are delivered directly into the platform. Investigators can benefit from improved search and can either step through analytic alarm events. The solution is scalable from a handful to thousands of cameras. Image courtesy of Salient Systems
FIND OUT MORE AT SALIENTSYS.COM

Viisights
Detect and record individual behaviors
The Wise 3.0 behavioral recognition video analytics from viisights provide detection, analysis and notification of violent activity, suspicious activity, individual and crowd behavior, perimeter and protection control, traffic monitoring, and personal and environmental safety. New detection capabilities included in Wise 3.0 include person-tailgating, person-abandon-bag/abandoned-bag, personal protective equipment (PPE) and more. The new release also provides improvements in processing throughput and speed impacting overall performance, specifically in high recall and low false positive rates. Image courtesy of Viisights
FIND OUT MORE AT VIISIGHTS.COM
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






