Cyberattack shuts down Seattle Public Library systems
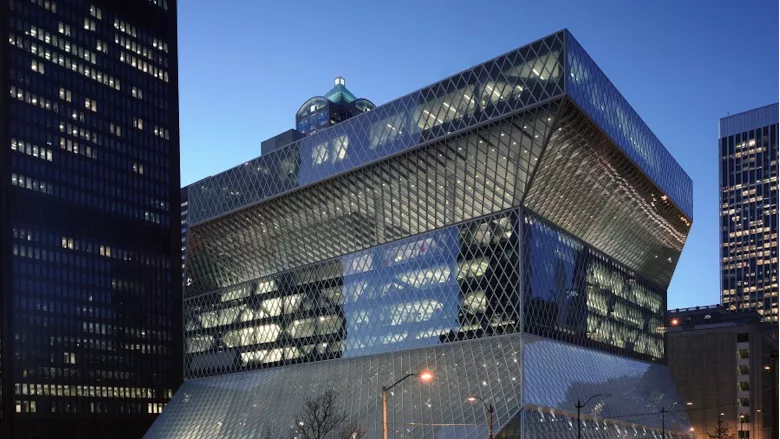
Image courtesy of The Seattle Public Library
The Seattle Public Library faced a cyberattack, forcing the library to take its systems offline. The attack obstructed access to the following:
- Staff and public computers
- E-books and e-audiobooks
- In-house Wi-Fi
- Online catalog and loaning systems
- The Seattle Public Library website
Although physical book loans and in-person events are still available, online resources currently remain unavailable. The library does not yet have an estimated timeline for restoring the function of its services.
On the subject of the attack, Nick Brigmon, Security Operations and Support Manager at Blumira, says, “In the wake of the cyberattacks on the Seattle Public Library and Toronto Public Library, now is the time for local libraries to bolster their cybersecurity measures. Libraries might not traditionally consider themselves prime targets for cyberattacks, with cybersecurity becoming an afterthought. However, this mindset leaves them vulnerable.
“Proactive cybersecurity is not just a defense mechanism but a commitment to preserving the trust and safety of our community. By recognizing the evolving threats and taking decisive action, libraries can protect their valuable resources and information.
“Unfortunately, we know implementing cybersecurity measures can be difficult for libraries due to limited resources. Thankfully, there are a few easy steps libraries can take to safeguard patrons’ information and ensure the uninterrupted provision of services for community members.
“Libraries looking for guidance on where to start on their cybersecurity journey can consider taking the following three steps:
- Conduct a comprehensive cybersecurity assessment: Engage a reputable cybersecurity consultant to conduct a thorough assessment of current systems to identify vulnerabilities in the network infrastructure, software and hardware. Consultants can also help library decision-makers stay informed about the latest threats and trends.
- Hold employee training: Conduct cybersecurity training sessions for all staff members and develop a clear policy for identifying and reporting suspicious activities. In addition, provide resources and support for recognizing phishing attempts and other common cyber threats.
- Develop an incident response plan: Develop and regularly update a comprehensive incident response plan (IRP) and take part in training exercises to test the effectiveness of the IRP in addressing common threats. Also, make sure to establish clear communication protocols for notifying stakeholders and patrons in the event of a breach. A cybersecurity consultant can be supremely helpful in these activities.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!









