Cybersecurity
Special Report
Claudia Natanson, Vice President, Information Security, AccuWeather
Read More
Special Report
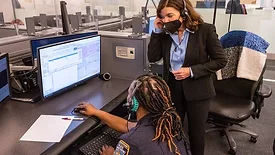
Making a difference in cybersecurity and intelligence
Teresa Shea, Vice President, Cyber Offense and Defense Experts, Raytheon Intelligence & Space
March 1, 2022
Special Report
Collaboration makes cybersecurity stronger
David McLeod, Vice President, Chief Information Security Officer, Cox Enterprises
March 1, 2022
Special Report
Making the future safer
Chris Novak, Director, Threat Research Advisory Center, Verizon
March 1, 2022
Special Report
Knowledge sharing in cybersecurity
Mark Dunkerley, Director, IT Architecture & Cybersecurity, Coca-Cola Bottlers’ Sales & Services, LLC
March 1, 2022
Special Report
Embedding cybersecurity into all organization levels
Diego Souza, Global Chief Information Security Officer, Cummins Inc.
March 1, 2022
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing