Security Top Stories
How Florida Agencies are Training for a Cyber Talent Pipeline
A new partnership in Florida strives to foster cybersecurity talent in state agencies through ongoing education and hands-on training
June 8, 2018
What to Look for in Travel Security and Executive Protection Services
What are the components and challenges of a successful travel security program?
June 5, 2018
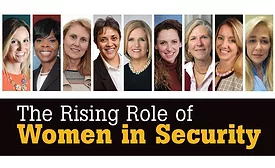
2018 Security Leadership Issue: The Rising Role of Women in Security
In the historically male-oriented security field, many women are successfully advancing to leadership roles.
June 1, 2018
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing