Security Top Stories
When it comes to using video in rugged terrain and remote locations, enterprise security professionals face a range of challenges.
Read More
A Public Private Partnership: the DSS and Enterprise Security
How does the the U.S. Diplomatic Security Service interface with public safety responders, and what can enterprise security learn from their successes?
March 18, 2020
Enterprise Security Must Prepare to Respond
An Effective Emergency Response Program is the Heart of Exceptional Service.
March 18, 2020
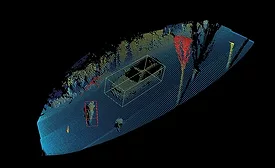
The Future of LiDAR and Security
Radar love? Yesterday’s news. Sonar? So out. LiDAR is the new heartthrob of the remote sensing world, in smart cities, surveillance, autonomous vehicles, intrusion detection and other applications.
March 16, 2020
Securing Soft Targets and Crowded Places
How can enterprise security secure soft targets and crowded places without intruding on the entertainment aspect of events?
March 13, 2020
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing