Surveillance Technology Gets More Proactive with Intelligence and Information
According to the FBI, in 2018, there were an estimated 1,206,836 violent crimes in the United States. More than 7 million of those crimes were property crimes, and the FBI estimates that reported violent crimes cost victims $16.4 billion.
Even beyond challenges with violent crimes is the challenge with repeat offenders. For example, a May 2018 U.S. Department of Justice report on state prisoner recidivism followed a sample of the 412,731 prisoners released by 30 states in 2005, representing approximately 77% of all state prisoners released that year. Almost 45% of the former prisoners were arrested within one year of release; 16% were arrested in the second year, 8% in the third, 11% in years four to six and 4% in years seven to nine. Thus, about 68% were arrested within three years, 79% within six years and 83% in nine years.
Just more than 50% of the former prisoners convicted of property crimes were arrested in the first year following their release, compared with 39% of releasees convicted of violent crimes, 43% with drug convictions and 41% with public order convictions.
This data clearly illustrates that today’s criminal ecosystem continues to evolve and progress to a level that imposes complex demands on security professionals in all types of industries. The answer lies in security professional’s ability to go on the offensive, to create deterrents, and to mitigate security events before they occur. Video surveillance is a powerful tool in that fight.
Yet, today’s security investigators and loss prevention professionals routinely face the mammoth challenge of finding a small snippet of valuable footage among hours of recorded video. The availability of low-cost cameras and increased storage has boosted surveillance coverage, but also has created a mountain of video footage. How can security search parse through all that video and quickly find what’s relevant?
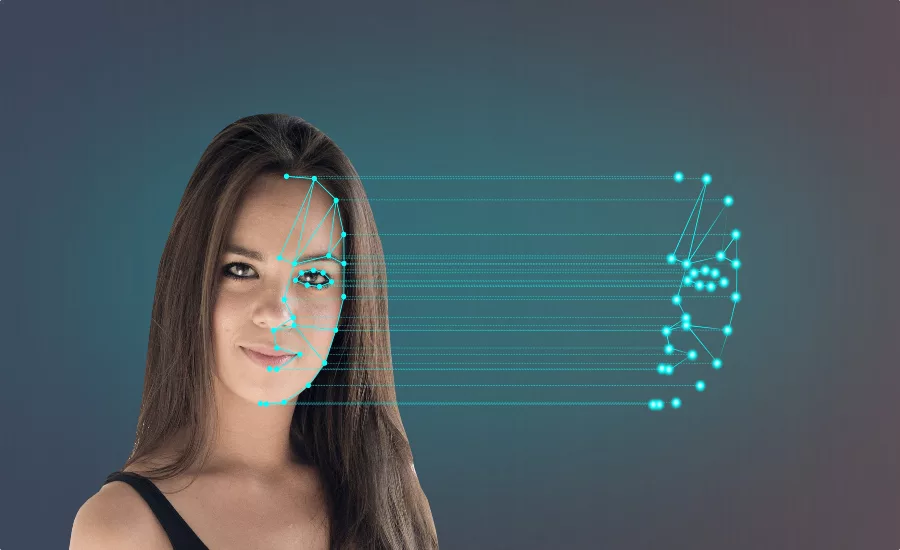
One solution is from Captis Intelligence, which gives security end users a powerful intelligence, information, investigation and identification tool. The solution integrates facial recognition and big data for instantaneous identification.
Here’s how it works: a user captures a criminal activity on their VMS from a live feed or recorded video, and grabs a still frame of the perpetrator’s face. They select a button on the solution that sits on their VMS. Within 4-5 seconds, the captured image is scanned across a database of more than 30 million criminals from law enforcement agencies – and matched. The matched files then pop-up with all available info on the identified perpetrator, including name, address, phone, previous arrests and criminal charges. This information can then immediately be shared with law enforcement.
Even more, the solution provides the ability to integrate additional facial databases and watchlists for various other security and business intelligence applications. For example:
- Companies can match employees with “banned” or “ex-employees” to automatically notify if they are on camera
- Schools can use for banned individuals, suspended students, sex offenders…
- Prisons/jails can use to scan visitors
- Retail for shoplifters, and both banned and prized customers
- Casinos for cheats and high-rollers
The cloud-based solution provides:
Intelligence – Extensive geographical police crime feeds, social media scanning/tracking, database access of more than 28 million criminals, deep and dark web intelligence that was previously only available to law enforcement.
Information – Internal and external communications related to investigations and collaborations with external businesses and law enforcement.
Investigation – Solveacrime.com access, social media criminal deterrent, database search, social media investigation tool, social media incident chatter visibility.
Identification – Access to the world’s largest private database of criminals. Identify a subject in seconds after uploading a facial image. 2nd layer of identification – Solveacrime.com, the world’s largest viral crime solving community.
The solution is cost-effective, as well, as there is no investment needed to purchase, install and learn how to use a separate facial recognition product.
Overall, enterprise security management can now proactively go on the offensive to quickly identify individuals and help apprehend suspects by implementing a powerful new deterrent that has already reduced incident rates by up to 70 percent in initial deployments.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








