Security Education & Training
Plus: School security & doors, the future of senior security leadership and much more.
Read More
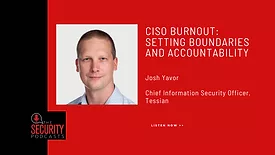
The Security Podcasts
Listen to Josh Yavor, Tessian CISO, talk burnout among security teams and executives
March 11, 2022
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing