Security Leadership and Management
Protecting Students, Staff and Community at Marymount California University
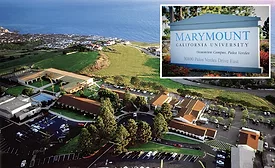
Learn about Hector Rodriguez, Director of Public Safety and Security at Marymount California University.
December 4, 2019
Contracted vs. In-House Guarding: No Universal Right Answer
Your security officers: should you in-house or outsource?
December 2, 2019
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing