Product Spotlight
Product spotlight on mobile and touchless security

The desire for mobile and touchless technology has grown over the past few years, especially in the wake of the COVID-19 pandemic. Additionally, the ability to manage a building’s entry points without a physical security guard present can help bypass current staffing shortages.
Security magazine highlights mobile and touchless security solutions, ranging from access control technology to identity management solutions.
Codelocks
Creates temporary access codes
The KL1000 G3 NetCode is a digital lock. NetCode allows owners to create date- and time-sensitive temporary access codes, which can be sent to the end-user by SMS or email. Codes can be created for single- or multi-use, giving people one-time access or repeated ongoing access for periods between one hour and one year. NetCode also includes a key override function. Image via Codelocks
Find out more at www.codelocks.us
DEN Smart Home
Unlock doors from mobile devices
The DEN SmartStrike is an invisible, wireless smart door strike that installs into the doorframe. Once installed, users can unlock their door using their traditional key or via the companion app to access their homes and businesses easily. Through the app, users can also create digital keys for guests to access the facility during specific periods. Image via DEN
Find out more at www.densmarthome.com
iDenfy
Prevents identification fraud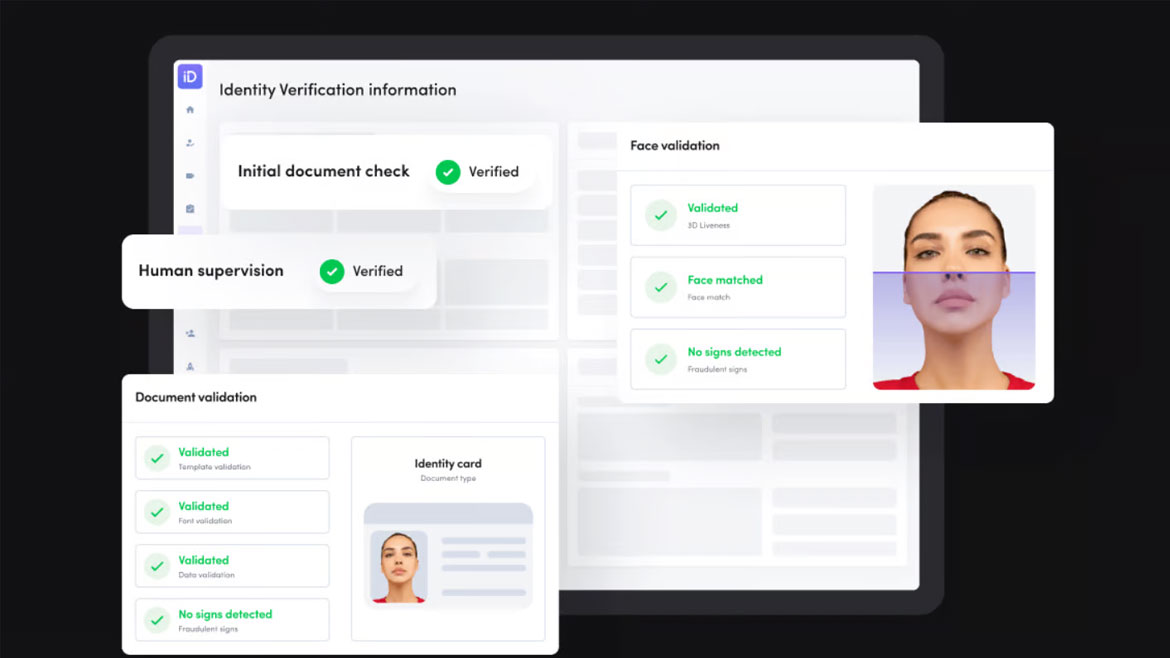
iDenfy ID verification is an AI-based verification platform. The platform offers biometric identification services designed to mitigate fraud. A user allows a reader to scan their face and the platform detects if the face is real or if someone is attempting to use a photo or video to access a building. The identity verification solution is certified by ISO/IEC 27001 standards. Image via iDenfy
Find out more at www.idenfy.com
Kaadas
Utilizes fingerprints for access control
Using a 3D biometric fingerprint sensor, the Kaadas KA202 Z-Wave Fingerprint Keypad Deadbolt unlocks doors and supports up to 50 fingerprints for access. Users can unlock the lock via the integrated biometric fingerprint scanner, via the integrated mechanical backlit keypad, or with the key. The KA202 also supports up to 250 unique user PIN codes allowing users to provide secure access to roommates, friends, family, guests or authorized service providers. Image via Kaadas
Find out more at www.kaadasgroup.com
Suprema AI
Recognizes faces using AI
Q-Face Pro is equipped with an AI-based face recognition algorithm and a neural processing unit (NPU) to provide face recognition for up to 50,000 users. The algorithm also registers when users’ faces change, such as when wearing different types and colors of masks, hairstyles, hats and glasses. In addition, it uses optimized radiant heat design and supports other contactless authentication methods including face recognition, QR codes and barcodes. Image via Suprema AI
Find out more at suprema.ai
System Surveyor
Maps out facilities in the cloud
System Surveyor is a live digital map and database for security, technical and IoT devices. System Surveyor enables users to document and manage devices across facilities and share that information with relevant partners, such as vendors, contractors and public safety. The system is cloud-based and can be loaded onto mobile devices. Image via System Surveyor
Find out more at systemsurveyor.com
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






