To keep or replace: IoMT security hinges on assessing device risk
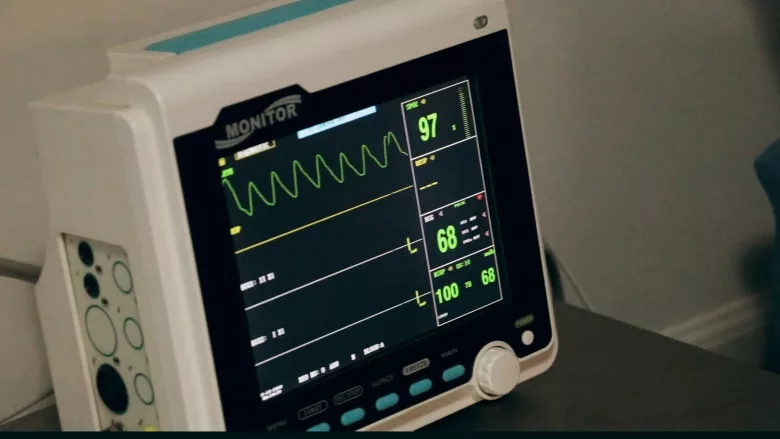
Image via Unsplash
Healthcare delivery organizations must approach the security of their internet-connected medical devices more urgently than ever — attackers are honing in on this often-vulnerable equipment (and the lucrative data it holds) with increasing sophistication. Indicators from the U.S. Department of Health and Human Services’ Office for Civil Rights (OCR) show that healthcare data breaches have more than tripled over the past decade. Just last year alone, 50 million individuals in the U.S. (or about 1 in 6 Americans) were tied to a healthcare data breach. Given this ever-more-ominous threat landscape, attacks exploiting medical device vulnerabilities to infiltrate networks and expose patient data — or even interrupt patient care — are now a top concern among healthcare organizations’ IT leaders.
But sooner or later, those leaders face a strategic quandary: when should medical devices with known security flaws be replaced, and when is a change unnecessary? Thorough risk assessments are the key to informing this decision-making process. The work of procuring new medical devices is time and resource intensive. Purchasing new devices (which might not be necessary to do) also puts direct pressure on budgets. For these reasons, healthcare IT decision-makers should seek to keep existing devices in place whenever possible. Only when a device represents a high risk — and there is no patch or fix available — should a (likely expensive) replacement be considered.
Let’s look at the motivations compelling healthcare organizations to take action (or, ideally, not) on medical device replacement, and run through some current risk assessment best practices that will yield more confident Internet of Medical Things (IoMT) technology and security decisions.
The disadvantages of IoMT device replacement
In addition to the high upfront device replacement costs, healthcare IT and security leaders must carefully consider several other factors. This industry is unique in that technology teams must confer with clinicians and other stakeholders to understand the impact that replacing a device will have on patient care. IT and security leaders may need to retain — and do their best with —IoMT devices that have known vulnerabilities because those devices have become essential to patient experiences and/or patient outcomes. (In short, a rip-and-replace of IoT devices can be a much more straightforward decision in manufacturing or other industries.)
For the same reasons, any IoMT device changes or new features that increase security but might also affect clinical functionality need to be carefully assessed and discussed. Healthcare organizations balancing those decisions will often find it necessary to favor the needs of their patients. Then there’s the additional (and very real) risk that a costly replacement device could prove just as vulnerable to attack as the previous equipment. This is why accurate risk assessment is important to guide device security decisions. Healthcare organizations with the right risk assessment strategy in place can prioritize vulnerabilities and keep existing devices healthy without the budget crunch of new equipment.
When replacement is the only option
While replacing established IoMT devices should be a last resort, healthcare organizations with no other option should maximize the potential benefits of these transitions. Devices with modernized security features should be able to quickly meet current regulatory compliance standards. The performance improvements with modern devices support healthcare operational management, via capabilities such as real-time patient data access that enables more accurate and decisive medical care decisions. Newer devices can also provide superior ease of use for caregivers (and patients, where relevant).
Device replacement can be necessary for outdated IoMT equipment that no longer receives manufacturer support — a variable that directly increases the risks of unaddressed vulnerabilities and the potential for malfunction. Also, while legacy devices require careful ongoing risk assessment and remediation of any recognized issues, new devices don’t carry the same level of burden.
Risk assessment and IoMT replacement best practices
With IoMT security, it’s crucial to recognize the actual level of risk presented by a given device. While an IoMT environment can include devices with thousands of known vulnerabilities, a complete risk assessment and exploit analysis will often show that 95% of those vulnerabilities present no real risk of enabling cyberattacks or data breaches. Identifying and preparing to address those remaining risks is the key purpose of an effective risk assessment. IoMT device risk assessments should also factor in a medical device’s configuration, security capabilities, impacts on the network and many other parameters — with the end goal of grading the device’s security posture. As a critical best practice to both budgets and operations, such risk assessments must be completed and weighed alongside organizational and patient needs before deciding whether new devices have to be procured and which of the existing ones have to be retired. Newly procured IoMT devices should also have their security tested and verified prior to deployment.
Minimizing or eliminating downtime during the transition to new devices is important to leave patient care uninterrupted. Strategies include having redundant systems to achieve continuous and disruption-free operations as new IoMT devices come online.
Accurate risk assessments build a successful IoMT device keep/replace strategy
Considering the large efforts, investments, and inherent risks of the IoMT device replacement process, it pays to get those decisions correct. A careful and complete risk assessment process will allow healthcare IT security leaders to confidently and accurately recognize and prioritize which IoMT devices require security attention—and, ideally, avoid spending for new off-the-shelf equipment.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






