Product Spotlight
RSA Conference 2023 product preview

Keeping an organization secure against cyber threats necessitates a combination of employee training, security processes and tools to bolster enterprise cybersecurity.
From hybrid-cloud solutions to risk management tools, Security magazine highlights recent products from security leaders at the 2023 RSA Conference.
SecureAuth
Authenticates User Identities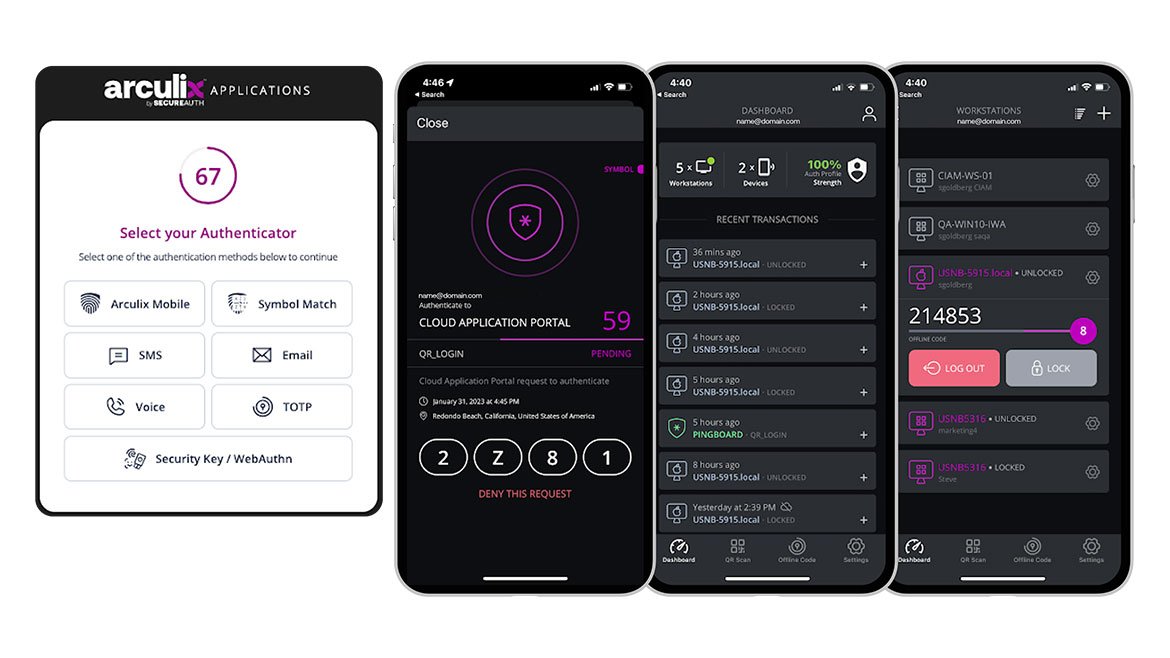
The Acrulix platform from SecureAuth takes an identity’s level of assurance based on user, device and browser trust that employs artificial intelligence (AI) and machine learning (ML) to determine anomalous behavior. Arculix builds zero trust initiatives by ensuring digital identities have the right amount of access to the right resources without having to repeatedly ask for re-authentication. Arculix generates a risk score when logging into a device that is used to grant access to tools the user needs. Risk is reassessed to provide multi-factor authentication (MFA) that utilizes analytics to deliver a user experience with adaptive workflows that step-up or step-down authentication based on overall risk. Image courtesy of SecureAuth
Find out more at www.secureauth.com
MITIGA
Aids in Cloud and SaaS Breach Response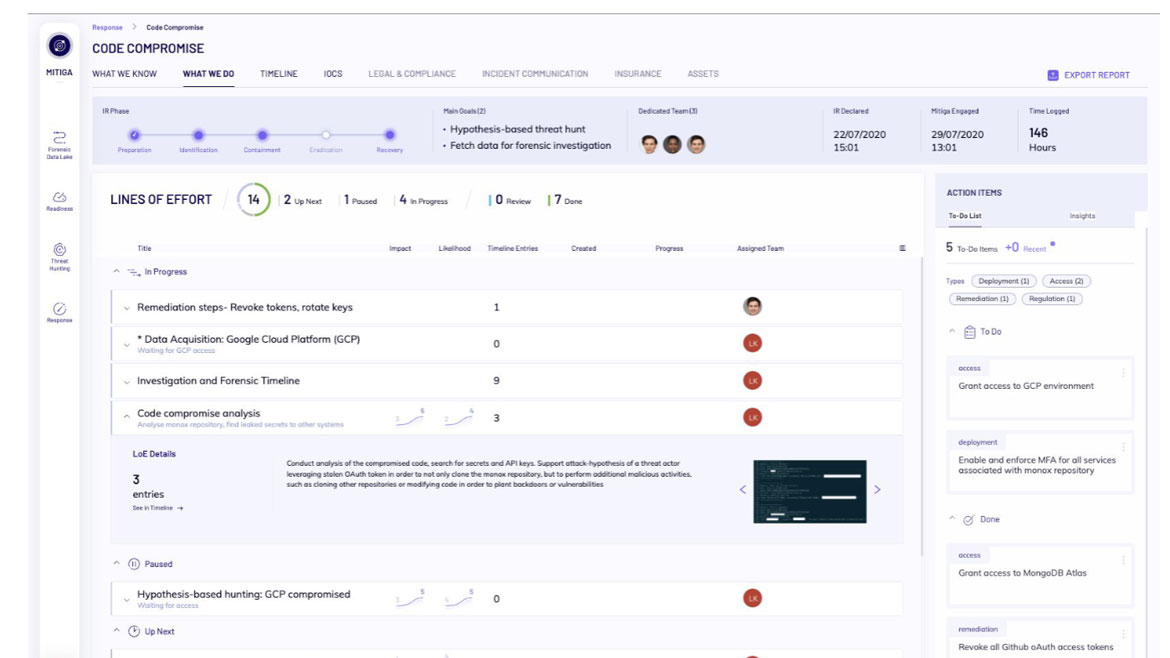
Mitiga’s IR2 Cloud Incident Response Platform allows organizations to prepare for, respond to and recover from cloud and Software as a Service (SaaS) breaches. IR2 gathers and analyzes forensics data to speed cloud investigations. The technology and data-driven approach combine to deliver a service-level agreement (SLA). IR2 integrates with cloud service providers (CSP) and SaaS. It runs hunts against user forensic data to either provide a “clean check” or commence investigation based on the Cloud Attack Scenario Library (CASL). Image courtesy of Mitiga
Find out more at www.mitiga.io
Wallarm
Discovers Leaked API Keys
The API Leak Management solution from Wallarm scans and discovers leaked application programming interface (API) keys and secrets. When leaks are found, the solution implements controls to block their use and protects against any follow-on attacks. This helps prevent unauthorized access to sensitive data within enterprise companies while protecting their internal operations and end-users from unauthorized use of that data. Users can maintain full-spectrum visibility, detection and protection for their web applications and API portfolio. Image courtesy of Wallarm
Find out more at www.wallarm.com
Regscale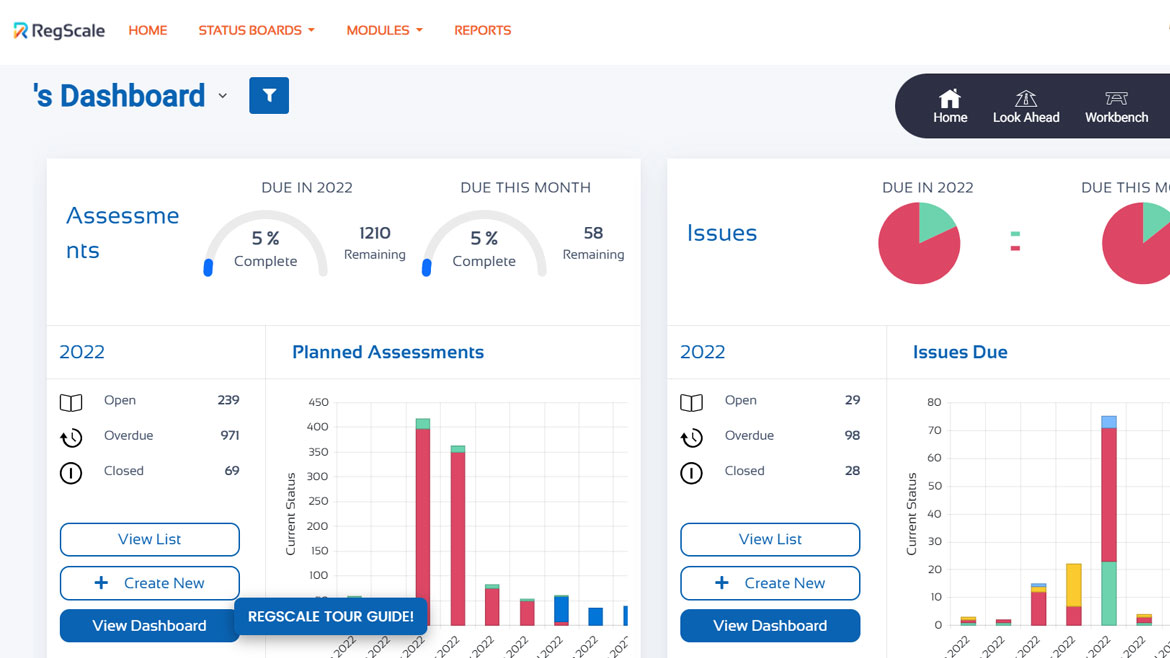
Shifts Compliance Left
RegScale’s continuous compliance automation software platform integrates with existing security and compliance platforms to manage the security control state, shifting compliance left to help deliver audit-ready documentation when needed for regulatory compliance. RegScale is used within the U.S. military, government agencies and corporate businesses. Image courtesy of RegScale
Find out more at www.regscale.com
Forgerock
Manages Platform Identities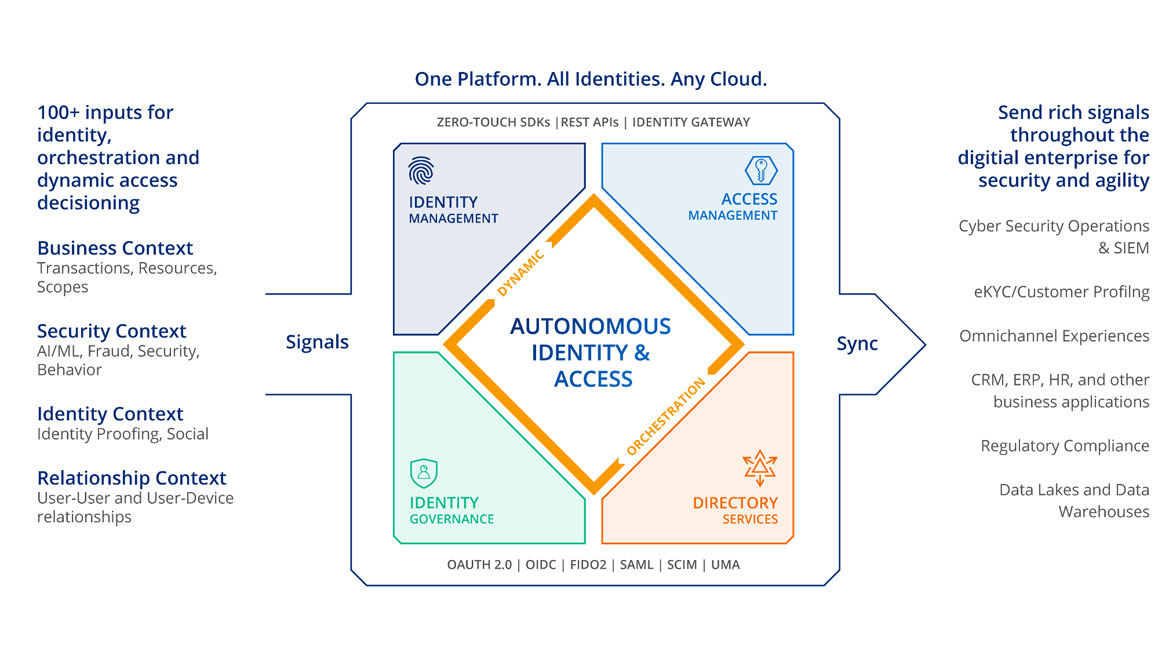
The ForgeRock Identity Cloud is an end-to-end identity solution that includes AI-driven identity and access management (IAM) and identity governance and administration (IGA) capabilities. It offers enterprise-grade capabilities for users, workforce and Internet of Things (IoT) identities, and is a customizable Identity Platform as a Service. ForgeRock Identity Cloud aims to deliver enterprise IAM requirements for SaaS applications and legacy on-premises applications. Image courtesy of ForgeRock
Find out more at www.forgerock.com
Silverfort
Scans for Identity Hygiene Issues
Silverfort launched free identity risk assessment available to discover the gaps and hygiene issues in their identity attack surface which may cause cyber insurance compliance failures. Silverfort’’s identity risk assessment operates at a directory level to report with in-depth visibility on the identity attack surface. The report summarizes risky user accounts and authentications as well as risk indicators such as shadow admins, passwords that never expire, admins liable to Kerberoasting, pass-the-ticket and lateral movement attempts, authentications using weak encryption protocols and unprotected service accounts. The free identity risk assessment provides organizations a clear view of their exposure. With the results they can better understand the steps necessary to improve security posture and insurability, such as applying MFA to critical resources and protecting service accounts. Image courtesy of Silverfort
Find out more at www.silverfort.com
Whitespider
Automate Service Migration
The WhiteSpider Hybrid Cloud solution aims to provide one-touch automated service instantiation and service migration, bringing applications closer to where they’re needed. The Hybrid Cloud solution is orchestrated through WhiteSpider’s tool, Merlin, which controls the instantiation, management and monitoring of the infrastructure. Image courtesy of WhiteSpider
Find out more at www.whitespider.com
Dig security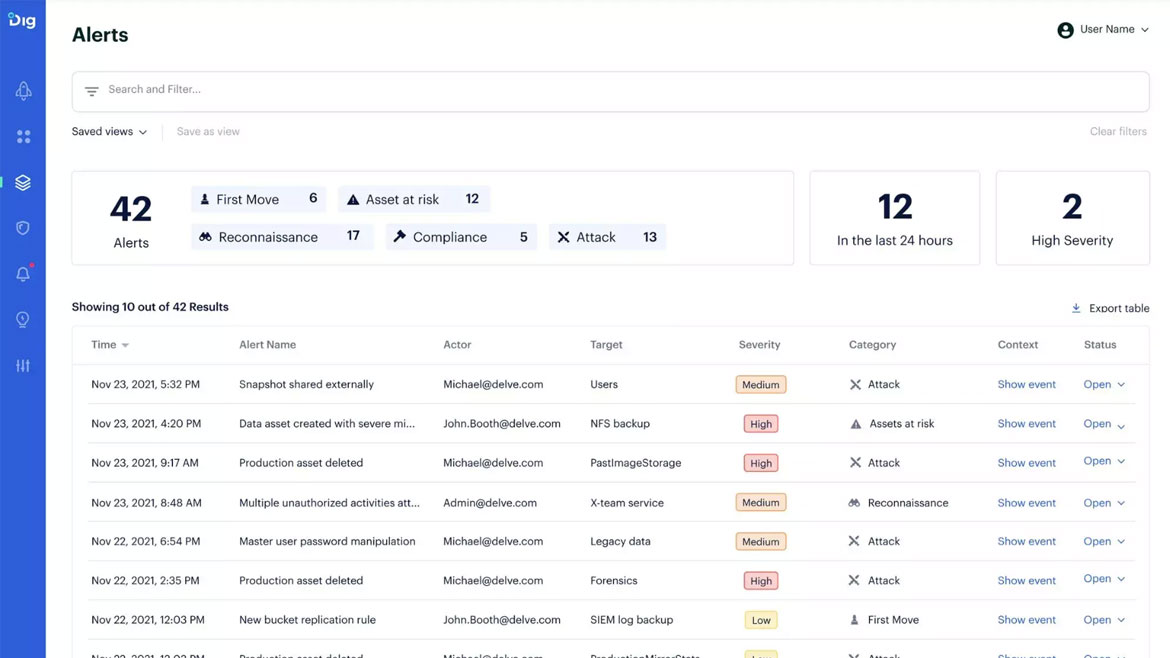
Protect Cloud Data
The Dig Data Security Platform enables organizations to discover, classify, protect and govern their cloud data. Dig's cloud-native and agentless approach uses cloud data loss prevention (DLP) with data detection and response (DDR) capabilities to help organizations better cope with cloud data sprawl. Dig finds data, brings context to how it’s used and what it contains, and provides real-time protection in response. It can support a number of cloud infrastructures. Image courtesy of Dig Security
Find out more at www.dig.security
Threatmodeler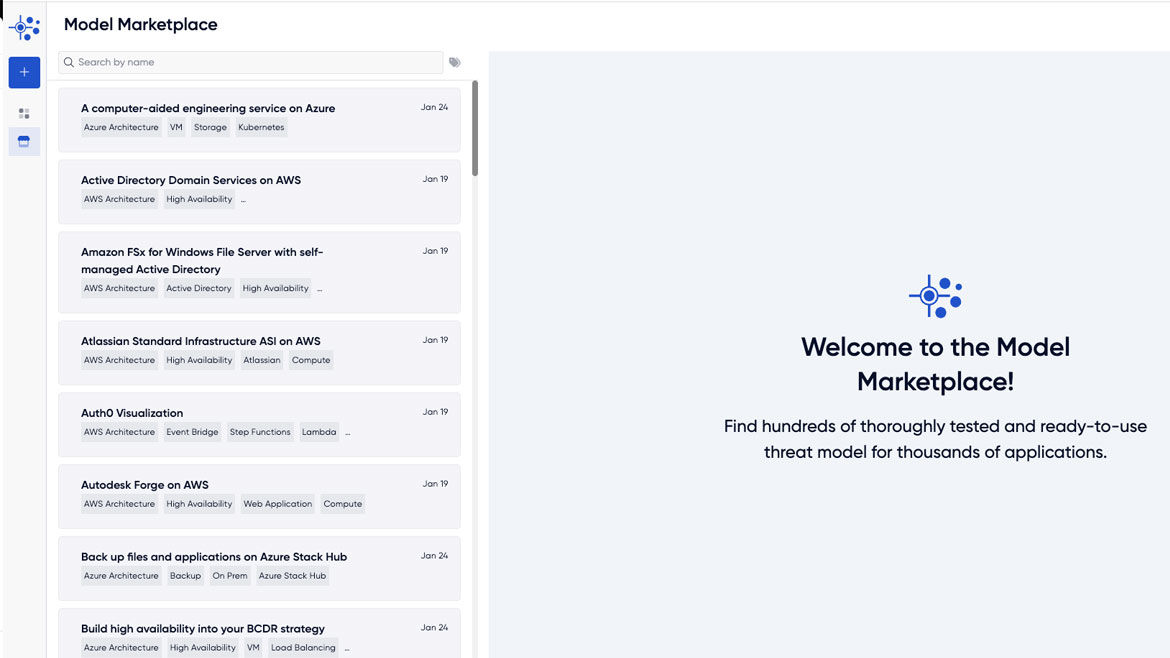
Pre-Builds Threat Models
Threat Model Marketplace is a cybersecurity asset marketplace offering pre-built threat models to be downloaded and incorporated into new and ongoing threat modeling initiatives. With Threat Model Marketplace, enterprises can visualize attack surfaces, understand security requirements and prioritize steps to mitigate threats across environments, including AWS, Azure and the Google Cloud Platform. ThreatModeler will introduce up to 50 new threat models per month to address a widening range of use cases, regulatory requirements and industry needs. Image courtesy of ThreatModeler
Find out more at www.threatmodeler.com
Keeper security
Manages Enterprise Passwords
Keeper Security’s Privileged Access Management (PAM) platform aims to deliver an Enterprise Password Manager (EPM), Keeper Connection Manager (KCM) and Keeper Secrets Manager (KSM). Keeper’s PAM platform is built with security that is both zero trust and zero knowledge. KeeperPAM is human-centric and reduces IT staff while maintaining identity security and access management across an organization. Image courtesy of Keeper Security
Find out more at www.keepersecurity.com
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






