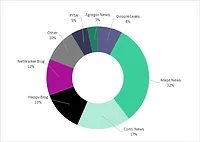
Leading ransomware variants in Q3

Image from Pixabay
During Q3 of 2022, Intel 471 observed 455 ransomware attacks, a decrease of 72 attacks recorded from the second quarter of 2022, according to the Leading Ransomware Variants report.
Intel 471 reported 27 ransomware variants were used to conduct 455 attacks from July 2022 to September 2022, a decrease of 38 attacks from the second quarter of 2022 and 134 from the first quarter of 2022.
In descending order, the most prevalent ransomware variants in the third quarter of 2022 were LockBit 3.0, which was responsible for 42.2% of all reported incidents, Black Basta at 11%, and Hive at 9.23%, and ALPHV aka ALPHV-ng at 6.6%.
The most-impacted sectors, in descending order, included:
- Consumer and industrial products
- Manufacturing
- Professional services and consulting
- Real estate; life sciences and healthcare
- Technology, media and telecommunications
- Energy, resources, agriculture
- Public sector; financial services; and nonprofit
The most-impacted regions, in descending order, were North America, Europe, Asia, South America, Oceania, Africa and the Middle East. The most impacted countries included the U.S., France, U.K. and Italy.
According to Intel 471, the dissolution of the Conti group likely impacted the overall quantity of breaches and placement of impactful ransomware variants for Q3.
Ransomware attacks observed in the third quarter of 2022 indicated that the variants collectively targeted 111 organizations in July 2022, 162 in August 2022 and 182 in September 2022. The LockBit variant has remained the most impactful ransomware service, with 192 attacks for the fourth consecutive quarter since the third quarter of 2021. Following LockBit 3.0, 50 attacks were associated with Black Basta, 42 with Hive and 30 with ALPHV. Other ransomware variants observed conducting multiple ransomware attacks this quarter in descending order were AvosLocker, Vice Society, STORMOUS RANSOMWARE, RansomHouse, Quantum and LV, each accounting for 32 or fewer breaches.
Matthew Warner, CTO and Co-Founder at Blumira, says, “Today’s ransomware attackers are also much more focused on blackmailing victims, getting data and doing more with that data. What we’ve learned in the last 20 years is that there’s value to that data that attackers will take advantage of. Securing environments against these attacks requires broad visibility and risk mitigation efforts that are difficult for organizations of all sizes to keep up with.”
Warner adds, “It’s extremely important that organizations focus on detecting the first three steps of a ransomware attack: discovery, gaining a foothold, and escalating privileges. Detection, in addition to being aware as to what data you hold that could help you restore from a backup, will allow you to quickly respond to attacks, or at worst case, understand how to handle post-exploitation of a ransomware event.”
Mike Parkin, Senior Technical Engineer at Vulcan Cyber, believes that “while an apparent reduction in ransomware attacks is welcome, it doesn’t mean we’re “winning the war,” so to speak, against these cybercriminal gangs. The frequency of these attacks ebb and flow based on everything from law enforcement activity to what exploits are effective to internal politics within, or between, the gangs. It’s entirely possible that the advantage currently lies with the defense, at least for now; however, it’s not something we can count on. It’s impossible to predict when the next wave of cybercrime will come rolling in, but we know that it will.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




.webp?height=200&t=1698173135&width=200)


