New ransomware variants emerged in late 2020

Digital Shadows released its Q4 ransomware report, analyzing key insights as ransomware continues to wreak havoc and new variants emerge with a level of regularity.
According to Digital Shadows’ Photon Research Team in Q4 2020:
1. Six groups made up 84% of alerts—Maze, Egregor, Conti, Sodinokibi, DoppelPaymer, and NetWalker— from the ransomware data leak sites Digital Shadows monitors.
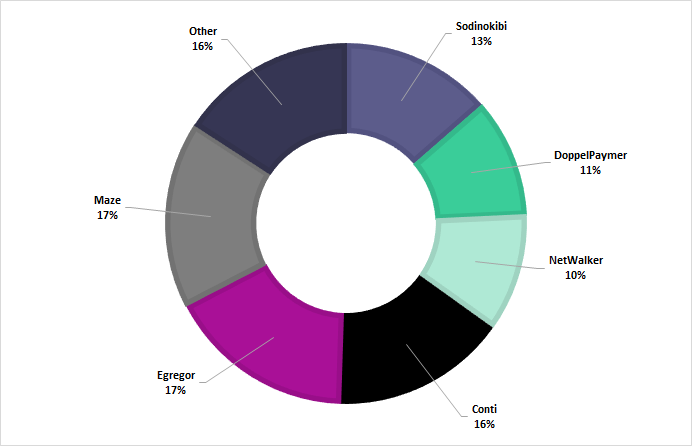
Most popular ransomware blog locations in 2020. Image courtesy of Digital Shadows
2. 29% of victims represented companies in the industrial goods and services sector, the leading sector by far, while the remaining was split among a range of industries.
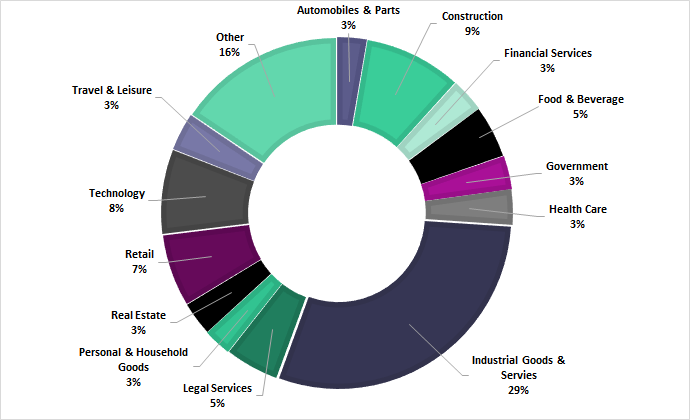
Breakdown of targeted sectors on ransomware data leak sites throughout 2020. Image courtesy of Digital Shadows
3. North America was the most targeted region, accounting for 2/3 of ransomware alerts.
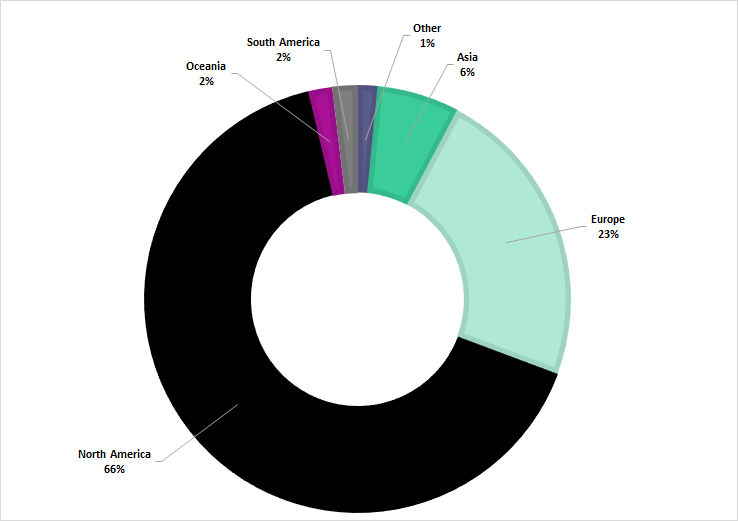
Breakdown of target locations throughout 2020. Image courtesy of Digital Shadows
Other key findings include:
- Ransomware groups attempted new tactics, which included cold calling victims to pressure them into paying the ransom demand; some attempts went as far as threatening employee’s safety.
- The pay-or-get-breached model continue to skyrocket in popularity.
- High profile victims from Q4 include Barnes and Noble, Ubisoft, and Epicor Software, to name only a few.
- Egregor entered the scene and made a name for itself— Egregor victims increased 240% from 25 September to October and another 43% from October to 17 November.
- Pay2Key, RansomEXX, and Everest ransomware groups joined the plethora of data leak sites with their own versions.
Digital Shadows encourages security teams to stay up to date with threat intelligence on the ransomware threat landscape to be able to identify data exposure on data dump sites early, research associated vulnerabilities, and identify early discussions and advertisements for sensitive information and employee credentials on cybercriminal marketplaces and forums.
For the full blog, please visit http://www.digitalshadows.com/blog-and-research/ransomware-analyzing-the-data-from-2020/
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





