Try creating employee personas to customize your security communications efforts
Taking a marketing campaign approach with internal security communication efforts

Data security is top-of-mind for businesses of all kinds as reports of data breaches hit the news with increasing frequency. Despite policies and ongoing appeals to employees to do everything within their power to protect critical company and customer data, breaches happen. Why? Often because these companies and their IT leaders are taking the wrong approach as they attempt to communicate key messages to employees.
Dry policies and once-a-year required in-house training is not enough to create a strong security culture. But a strong security culture is exactly what companies need. How to get there? By taking a marketing campaign approach to internal security communication efforts.
Security awareness should be an ongoing campaign, not just an event. That campaign, just like any marketing campaign, starts with a thorough understanding of the target audience — the people you wish to influence to adapt security best practices.
Define Audience Segments
Most security communication messages are sent en masse to the entire organization. Yet most organizations are comprised of people in different roles, with different levels of understanding and awareness of security-related issues, and different levels of “need to know.”
For instance, employees in the IT department will need slightly different information than employees in the sales department; after all, they have access to different systems and have differing levels of risk associated with the data/systems they access. Employees without access to critical information stored online will need different information than employees with access to extremely sensitive or proprietary information.
Create Employee Personas
Marketing professionals are very familiar with the concept of creating personas — detailed profiles of target audiences they wish to influence. Each persona will have different motivations, concerns, strengths, and weaknesses. Understanding these different personas helps unlock a range of new possibilities for engagement.
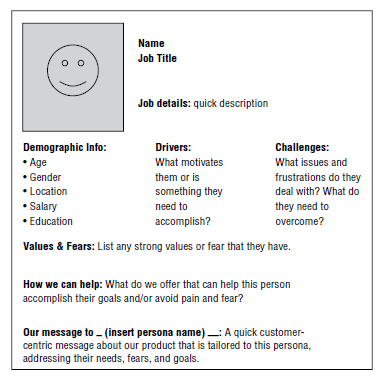
Once you thoroughly understand the different employee segments you wish to influence, you can build a more surgically precise campaign that targets those specific segments and personas. Your messages will be designed to target the right people, with the right message, at the right time.
Not just one message delivered through one channel. Successful campaigns require a multichannel communication approach and ideal choice of endpoint device.
Create Messaging Designed to Move Your Audience
The messages you send to your target audience based on the personas you’ve drawn out will contain three key elements -- the what, the how, the why. These elements are part of Sinek’s Golden Circle model. Developed by leadership expert Simon Sinek, the Golden Circle model provides a framework for communicators to help them focus their messaging.
- The ‘why’ is the purpose of the message. For instance: “To ensure employees understand the importance of creating strong passwords.
- The ‘how’ provides instructions on how to execute or complete the desired behavior.
- The ‘what’ is the actual security-related message or instruction.
Keep in mind that you will be creating messages personalized to each of the personas you have developed. Your next step, then, is disseminating your message.
Take a Multichannel Communication Approach
A one-and-done approach is not the way to influence employees and change behavior. Just as marketers know that to achieve their goals and objectives they must communicate multiple times in multiple ways, so should Security leaders identify and use a wide range of communication channels to make sure their messages resonate.
Your goal is to find people where they are and continually get your messages out in front of them—repeatedly. People don’t change their opinions or behaviors by hearing or reading information once. It takes multiple, ongoing exposures over time to change behaviors.
Track Results and Measure Effectiveness
Marketing is a numbers game and savvy marketers are monitoring those numbers all the time. There are a variety of things you can measure to give you insights into how well your marketing campaign is working — both process and outcome measures.
Process measures may be things like:
- Page views. How many people clicked on the link in your intranet or Slack channel to take them to more detailed information about a message they received?
- Document downloads. How many employees were curious enough to learn more about a critical security patch or incident because of the compelling email you wrote?
- Webinar views. How many people watched — in its entirety — the webinar you produced on important security protocols to follow?
Outcome measures are where the rubber meets the road. These could be things like:
- Decline in number of employees who fall victim to your simulated phishing attacks.
- Number of employees who change and/or create strong passwords within your allotted time.
Partnering With Your Marketing Colleagues
Get your company’s marketing department involved in your in-house efforts. Turn to these communication experts to help you develop and deliver the kind of results they’re used to achieving with customers. Not only will you be able to benefit from their expertise in creating content of all kinds — you’ll also benefit from developing some allies in your quest to create a strong security culture. They’ll become advocates and ambassadors for your messages.
Traditional messages created and disseminated by security departments are generally not sufficient to achieve real, lasting impact and behavior changes among employees. Taking a campaign approach to your security messaging, in partnership with your marketing colleagues, can result in the real changes you’re attempting to achieve.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








