OEMs should take control of security when it comes to vehicle hacking
How Easy Is it to Hack a Vehicle? We hear everyday about kids hacking into computers and forget how vehicles are actually comprised of multiple computers - so how easy is it to actually hack a vehicle’s computer system?
Vehicle systems are much like any other computer systems, connected to the internet and will eventually result in the same behavior and suffer the same security threats that any other computer faces. Meaning “script kiddies’ can eventually find their way to a connected vehicle but not every layer of the vehicle is easy to hack. It is important to distinguish though, between attacks on the connected components of the car and attacks on the deeper car systems such as critical safety systems which will require additional skills to attack.
Changing a Security Mindset
Simple attacks on the connected systems, or "low hanging fruit" exploits depend much on the accessibility of the attacker to the attack surface of the target. Connected cars today have content and services that are very much controlled by the OEMs and the accessibility is limited. However, there are already signs of uncontrolled content making their way to the market. Application stores, Internet browsing, and mobile connectivity are changing the accessibility factor allowing much easier access to the car attack surface, so we can expect a change in the near future. Additionally, sometimes this surface level content opens the door for an attacker to get deeper inside a vehicle.
Currently, automakers' most urgent concern is around the safety of the critical systems and most of the security efforts of cars are oriented around those important features. However, the connected car introduces new threats to non-safety critical car systems, such as theft, privacy and operational threats like ransomwares. This is a shift in thinking that automakers are going to need to change and adopt, very quickly.
Gaining Complete Visibility
To protect vehicles, OEMs, Tier 1s and other suppliers are facing multiple obstacles to meet the developing regulatory needs of the industry, the most important of which is the need to protect vehicles from cyberattacks throughout their lifecycle, meaning continuously from development all the way through its “life span”. To do this one essential element to automotive security is complete visibility.
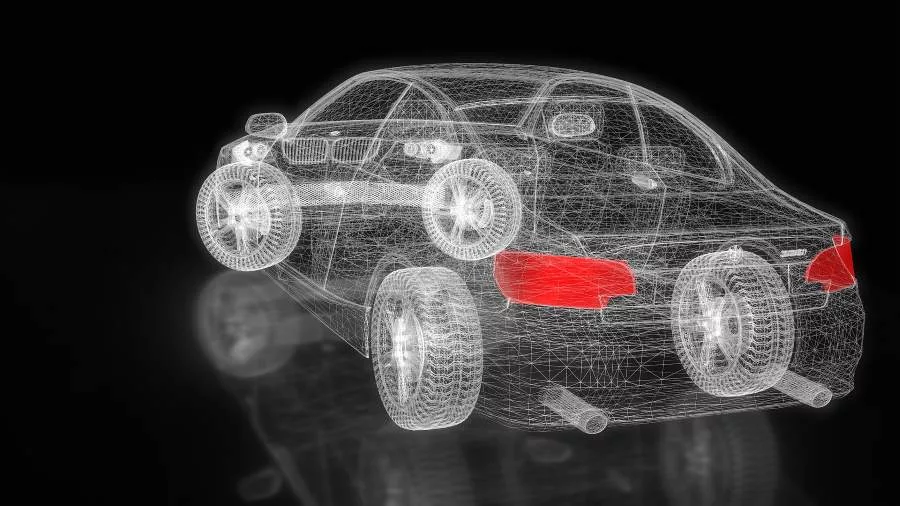
Visibility is crucial for cybersecurity management, which means a complete and continuous view of the security system, similar to a map. This view needs to understand the minute details down to the supply chain to understand how to monitor and protect it. This is important because vehicles have so many different components from so many different suppliers that all have varying types of protection. The visibility needs to understand it all so it can detect if there are any “holes” in the security system of the vehicle. It is essential that before professional cybersecurity teams can protect their products, they must have full oversight of the inner workings of a vehicle.
Providing a 360-degree oversight of the operation of security control to OEMs makes relevant security information easily accessible and therefore manageable. For OEMs, this is the main obstacle to overcome especially when considering the number of vehicle models and topologies, increasing connectivity and over-the-air updates - once the vehicle is on the road, visibility provides an important means of constant and systematic analysis, allowing for a strong security posture.
Once they gain visibility into their vehicles’ cybersecurity lifecycles, OEMs can perform risk assessments and analyze potential threats, plan their desired security policy and enforce the chosen policy across the board to gain full ownership.
The first step in the battle to full automotive security, is seeing the problem. Once the cybersecurity issues are uncovered, OEMs can take control creating a pathway to security throughout the vehicles’ lifecycle.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






