The most overused buzzwords in cybersecurity are...

A survey of Black Hat attendees, conducted by Invicti Security, unveiled fun and interesting information, including the most overused buzzwords in cybersecurity and the fact that 64% of respondents say their organizations' security resources have not increased in response to recent high-profile security breaches.
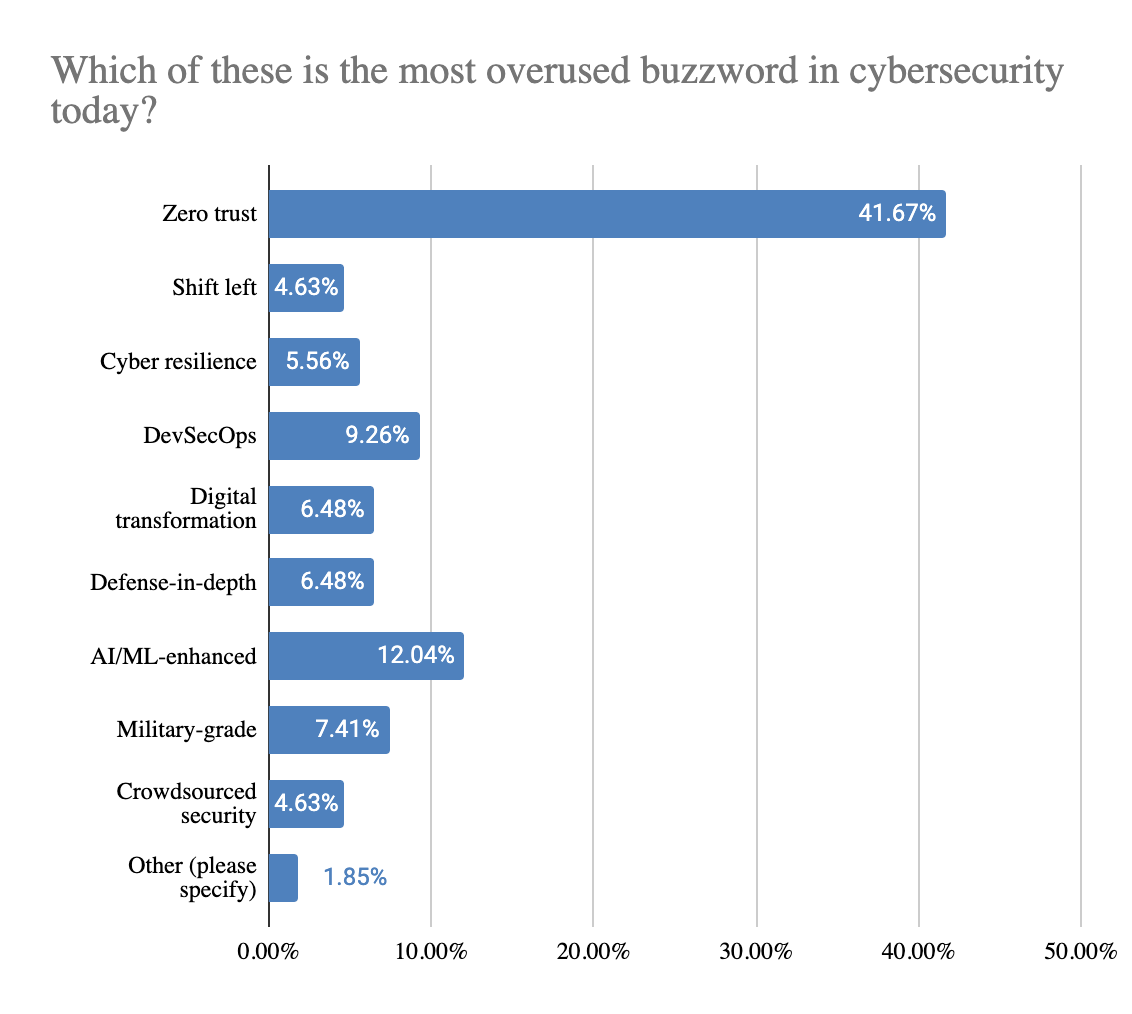
- “Zero-Trust” is the most overused buzzword in cybersecurity today - by a lot.
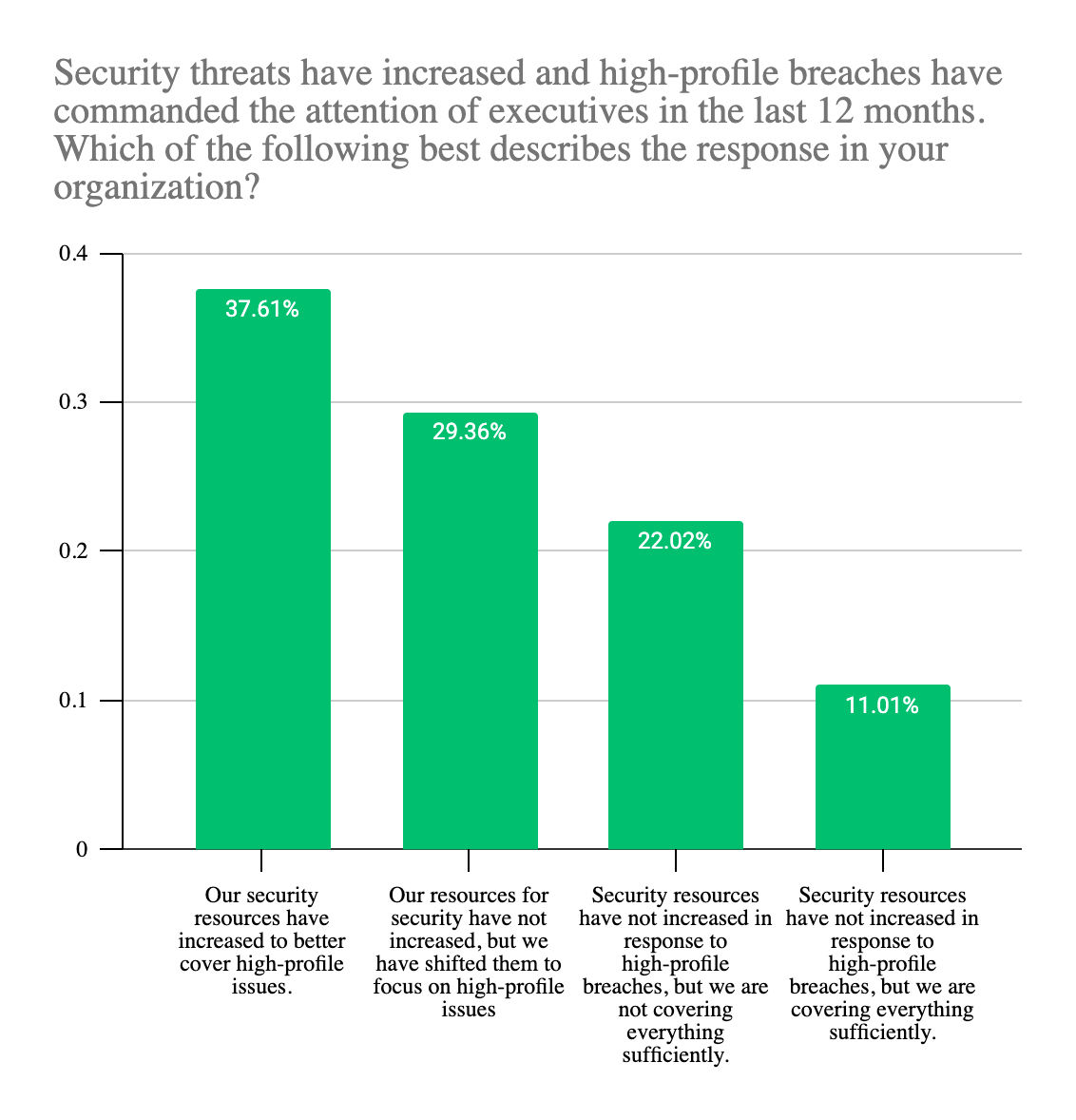
- 64% of respondents said that their organizations’ security resources have not increased in response to high-profile breaches.
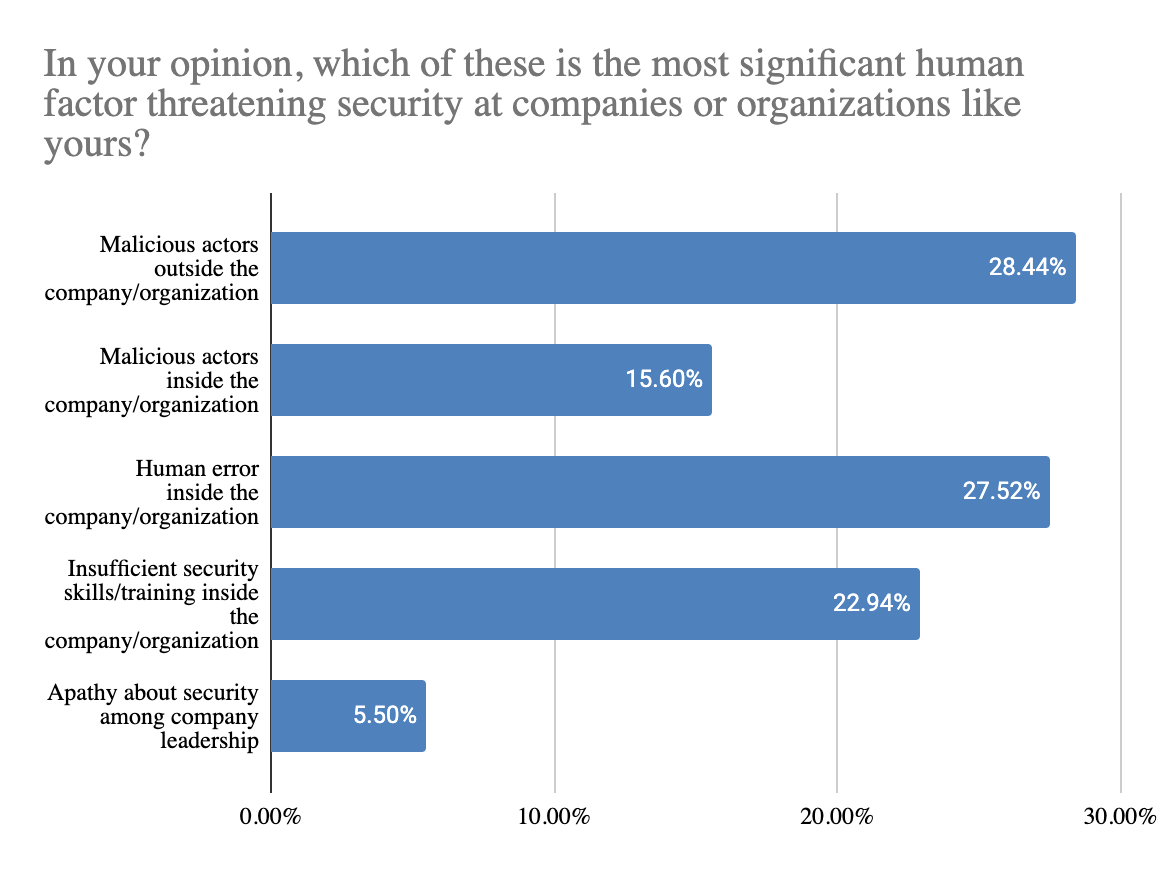
- The biggest perceived threats are malicious actors outside the company (28%), followed right behind by human error inside the company (27%). Insufficient security skills inside the company was also a popular response (23%).
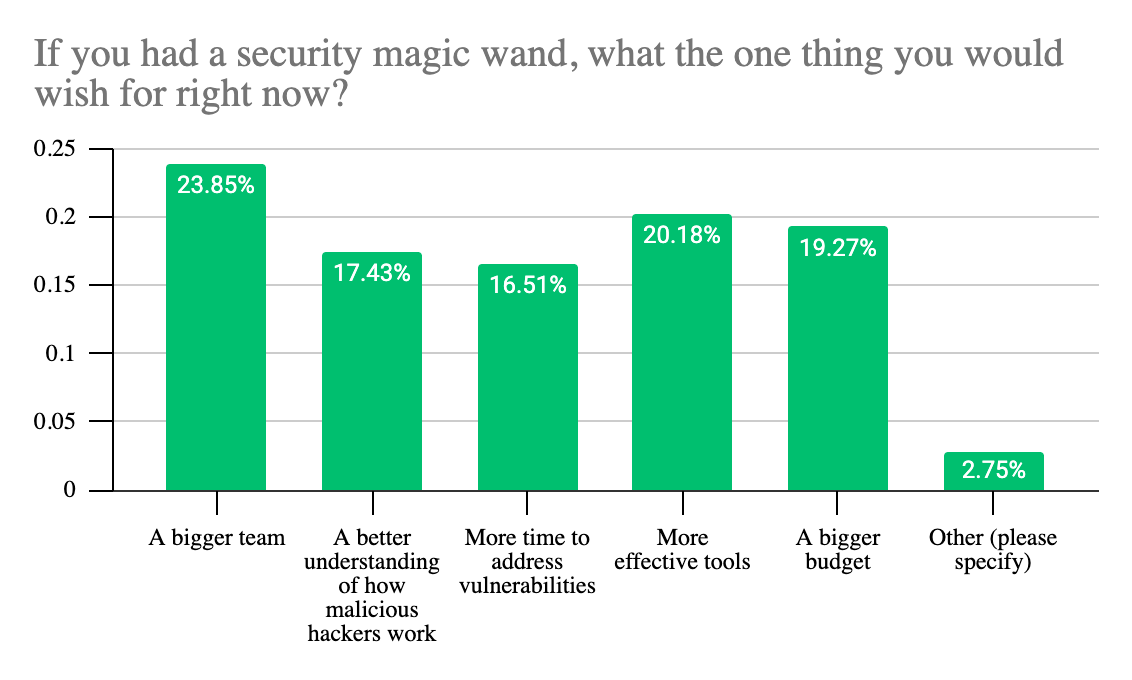
- Top of the wishlist for cybersecurity professionals - a bigger team (24%), more effective tools (20%), and a bigger budget (19%).
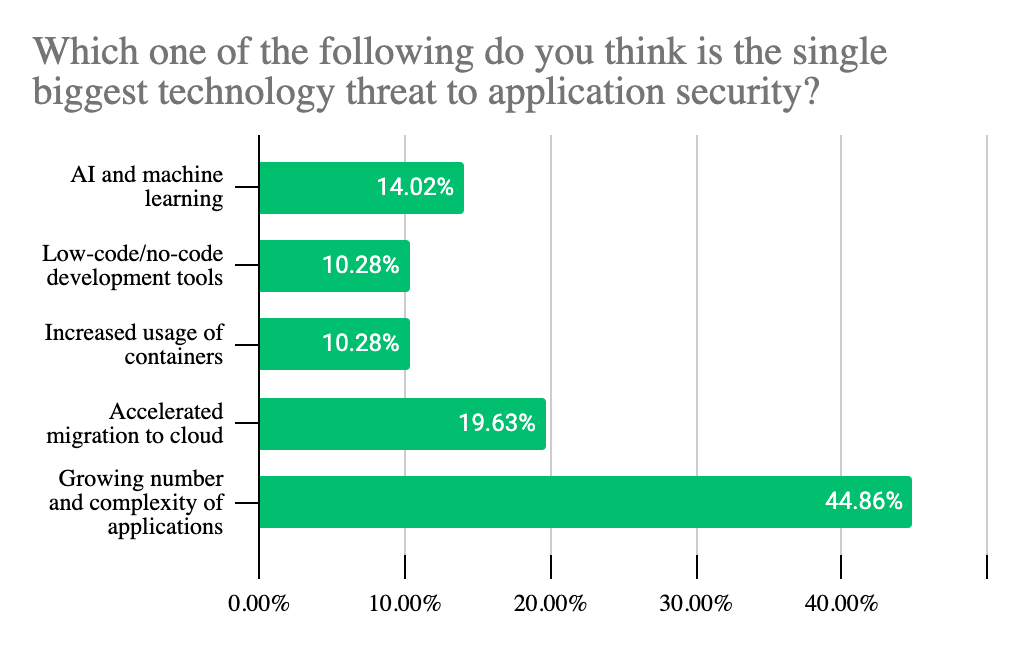
- By far the largest portion of respondents (48%) see the growing number and complexity of applications as the single biggest threat to app security.
- The average number of days to burn down existing technical debt, if focusing on nothing else?
375
- When asked about the impact of the Biden administration cybersecurity policies:
- More than a quarter (27%) expect the order to make their job at least a little bit easier.
- Another quarter (26%) think it will make their job at least a little bit harder, with 10% expecting it to make their job a lot harder
- About half (47%) are expecting things to stay about the same
- When asked to #badlydescribe their job, some highlights included:
- I fix people’s bad planning
- Hack my company to keep hackers from hacking my company
- I solve and squash problems or errors before anyone even knows a problem exists. Not all heroes wear capes.
- Custodial engineer. I clean up the mess
- Make people think my ideas were theirs #inception
- I let people cry on my shoulder and help them realize it was their fault
- If people hate me, I am doing a great job
- I tell everyone their work quality is bad. Eventually they agree.
- I teach people to break things
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





