The IoT Cybersecurity Improvement Act: A first step in bolstering smart technology security
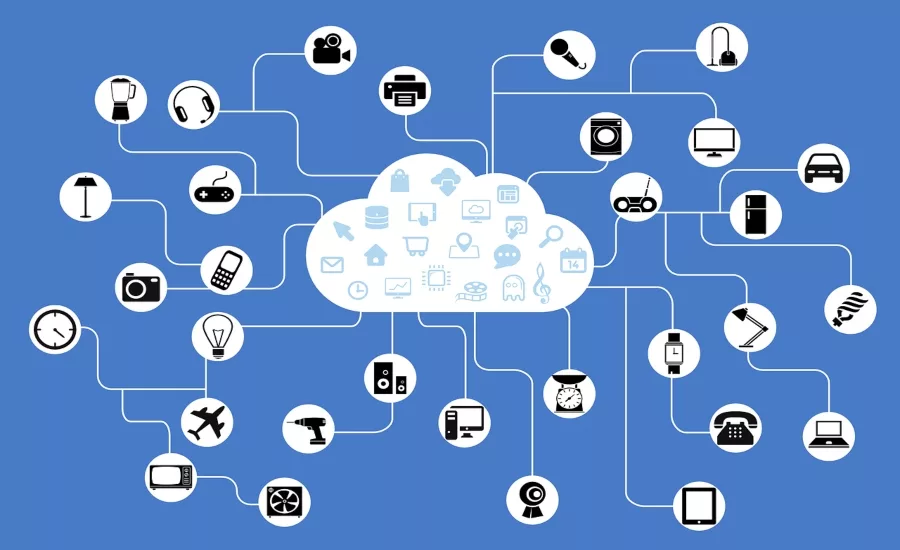
Connected devices are known first and foremost for their convenience factor -- from smart vacuum cleaners to digital assistants, it’s easy to understand why the use of Internet of Things (IoT) technology has seen such widespread adoption. Every second, 127 new IoT devices are connected to the web, and experts predict that by 2025, that figure will equate to more than 75 billion connected devices overall. But, such convenience also brings security risk, as these devices are often riddled with security vulnerabilities impacting security and privacy both at a consumer and corporate level.
In an effort to help bolster the security of IoT devices, on December 4, 2020, the Trump administration signed the Internet of Things Cybersecurity Improvement Act of 2020. The first-of-its-kind legislation requires the creation of security standards and guidelines for IoT devices used in and purchased by the federal government, and encompasses issues such as secure development, identity management, patching processes, and configuration management. The IoT security bill also calls for guidelines in vulnerability reporting for IoT devices in government networks, as well as of those of federal contractors.
The IoT security bill is a step in the right direction, as it addresses one of the biggest gaps in software security overall -- generating awareness. But, as the use of connected devices continues to exponentially grow over time, we must ask ourselves: is it enough? Let’s explore.
Progress Made, but Just a Stepping Stone
While there is still a lot of work to be done in securing the IoT ecosystem, this latest bill should be applauded, as it brings the topic of IoT security to the forefront of the agenda for federal organizations, technology manufacturers and consumers alike. One of the most prominent takeaways from the bill is that standardized guidelines on IoT security are now available from one of the most reputable security organizations, the National Institute of Standards and Technology (NIST). While intended for government parties, these guidelines can provide manufacturers and security vendors with a general roadmap of how to bolster IoT security measures overall -- something that has been lacking in years past.
However, the opportunity to expand and enhance IoT security is still present, and needed, as the bill in its current state addresses only a portion of the larger problem at-hand. The security regulations outlined in the bill only apply to IoT technologies that will be used in federal environments, rather than being applicable across all relevant IoT-enabled devices.
While providing secure IoT technologies is still the primary responsibility of manufacturers, end users must also demand more security measures from the companies selling such devices. This will then create a ripple effect, sparking proactive action from manufacturers and security vendors to holistically address IoT security concerns from the start, with an all-encompassing set of guidelines required to secure IoT device manufacturing, distribution and implementation. Only through this domino effect will IoT security move beyond the government and into our own homes and business environments.
Immediate Steps to Bolster IoT Security
According to the OWASP IoT Project, which is designed to help manufacturers, developers, and consumers make better security decisions when building, deploying, or assessing IoT technologies, the most common IoT security risks include:
- Weak Guessable, or Hardcoded Passwords
- Insecure Network Services
- Insecure Ecosystem Interfaces
- Lack of Secure Update Mechanism
- Use of Insecure or Outdated Components
- Insufficient Privacy Protection
- Insecure Data Transfer and Storage
- Lack of Device Management
- Insecure Default Settings
- Lack of Physical Hardening
From the manufacturers’ perspective, it’s critical to be aware of the dangers of IoT vulnerabilities, the options for mitigating those dangers, the proper methods and technologies for testing the underlying software, and the correct way to handle reports and fixes in the event that security issues are discovered. Oftentimes, software developers are racing to build the newest piece of software or deploy the latest and greatest update to an existing product in order to match, and exceed, the industry’s pace of innovation. However, this often comes at the expense of software security. It’s critical for manufacturers to not only arm their developers with the appropriate tools to detect code-borne vulnerabilities earlier in software development cycles, but also provide them with the proper training to create more secure code, which should be regular, interactive and empowering in nature.
For end users, this list is a clear indication that everyone must be more aware of their security posture when it comes to IoT devices. For example, when activating a connected device, change the default password to one that is long, complex and difficult to guess. It’s also important to remember that we get what we pay for -- sometimes, taking the more affordable option when purchasing a connected device means that security likely wasn’t as big of a priority during the project. Research the manufacturer in advance to learn more about its history and security reputation, and see if the device and/or vendor has recently made headlines for any of the wrong reasons.
Moving forward, we can expect technology manufacturers to assume more responsibility over the security of their smart devices, rather than assuming users will properly protect themselves from the risks. This is in large part due to consumers starting to demand action from manufacturers, as witnessed in a recent class action lawsuit after several customers complained their smart doorbells were hijacked by malicious actors.
Overall, when buying an IoT device, always ask yourself, “Do I really need this?” Yes, smart devices can make life easier and more convenient, but that often comes with security risk.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







