FBI warns of BEC scammers using email forwarding

The U.S. Federal Bureau of Investigation (FBI) issued a Private Industry Notification alert, noting that cybercriminals are increasingly implementing auto-forwarding rules on victims' web-based email clients to conceal their activities. According to the FBI, cybercriminals then capitalize on this reduced visibility to increase the likelihood of a successful business email compromise (BEC).
"While IT personnel traditionally implement auto-alerts through security monitoring appliances to alert when rule updates appear on their networks, such alerts can miss updates on remote workstations using web-based email," says the FBI.
If businesses do not configure their network to routinely sync their employees' web-based emails to the internal network, an intrusion may be left unidentified until the computer sends an update to the security appliance to monitor changes within the email application, leaving employees and all connected networks vulnerable to cyberattacks and hackers.
In 2019, the Internet Crime Complaint Center (IC3) reported more than $1.7 billion in worldwide losses due to BEC schemes. The alert, which was recently made public, says the technique has been observed and abused in recent BEC attacks:
- In August 2020, cybercriminals created auto-forwarding email rules on the recently upgraded web client of a US-based medical equipment company. After the BEC actors obtained access to the network, they impersonated a known international vendor, obtaining $175,000 from the victim.
- During another incident in August 2020, the same actor created three forwarding rules within the web-based email used by a company in the manufacturing industry.
Mark Chaplin, Principal at the Information Security Forum, a London-based authority on cyber, information security and risk management, explains that BEC attacks reflect the continued evolution of criminal activity in compromising senior, privileged and commercially vulnerable employees.
Chaplin explains, "With the COVID-19 pandemic continuing to remain in the forefront of public consciousness, organized criminal groups are taking advantage of new working arrangements and global brands to steal large sums of money. Uncertainty will continue to provide criminals with further opportunities. BEC sits firmly on every organization's threat radar and will remain there for the foreseeable future.”
According to Chris Morales, head of security analytics at Vectra, a San Jose, Calif.-based provider of technology which applies AI to detect and hunt for cyberattackers, while Office 365 provides the distributed workforce with a primary domain to conduct business, it also creates a central repository of data and information that’s a prime target for attackers to exploit.
"Rather than leveraging malware, attackers are using the existing tools and capabilities already present in Office 365, living off the land to stay hidden for months. Forwarding emails is just one of many techniques to worry about. After attackers gain a foothold in an Office 365 environment, there are several common techniques that can occur, including:
- Searching through emails, chat histories, and files looking for passwords or other interesting data
- Setting up forwarding rules to obtain access to a steady stream of email without needing to sign-in again
- Leveraging the trusted communication channel (i.e. sending an illegitimate email from the CEO’s official account, used to socially engineer employees, customers, or partners)
- Planting malware or malicious links in documents that many people trust and use, again manipulating trust to circumvent prevention controls that may trigger warnings
- Stealing or holding files and data for ransom
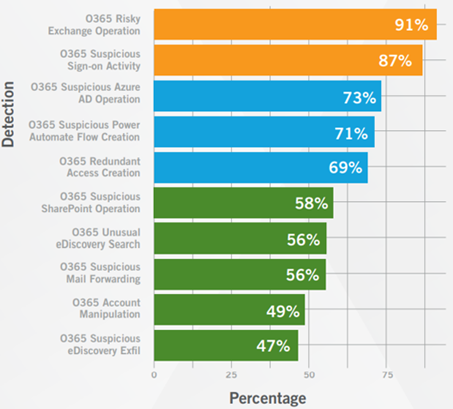
In recent Vectra research of the top ten most common techniques, Morales says, they found suspicious mail forwarding to be the eighth most common behavior.
Morales adds, "The importance of keeping a watchful eye on the misuse of user access cannot be overstated given its prevalence in real-world attacks. In the current cybersecurity landscape, security measures like multi-factor authentication are no longer enough to deter attackers. SaaS platforms like Office 365 are a safe haven for attacker lateral movement, making it paramount to focus on user access to accounts and services. When security teams have solid information and expectations about SaaS platforms such as Office 365, malicious behaviors and privilege abuse are much easier to quickly identify and mitigate.”
Matthew Gardiner, Principal Security Strategist, Mimecast, says, "The use of auto-forwarding rules is a standard operating procedure for BEC focused cybercriminals. With auto-forwarding setup to forward email to the attacker the attacker can literally quietly read the targets email for an extended period and decide when to launch the next step of the attack. Using auto-forwarding on web-based email clients versus traditional clients such as Microsoft Outlook adds another layer of obfuscation and gives the cybercriminal more time in the email without the likelihood of detection. A similar set of attacks was reported last month that resulted in approximately $15M being illegally diverted. There are multiple ways organizations can protect themselves from these sorts of attacks, including stronger security controls, improved security awareness training, and more resilient business processes. Perhaps a more interesting question is why so many organizations don’t appear to be making these well-known investments and changes."
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







