Measuring the Impact of Cyberattacks: Lost Revenue, Reputation & Customers
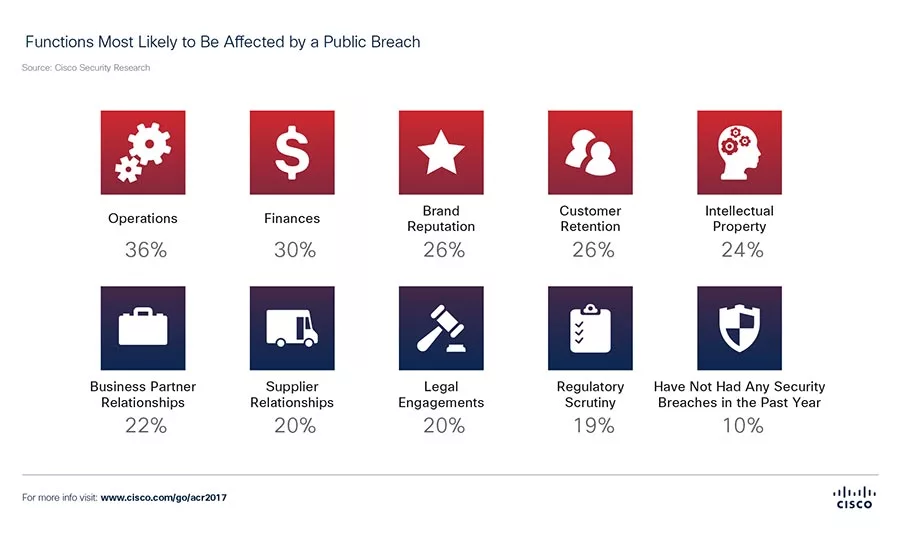
Which functions are most likely to be affected by a data breach? According to the latest report from Cisco, Operations and Finance are top of the list. Chart courtesy of Cisco.

Organizations are feeling the effects of data breaches much more keenly, as many that experience a cyberattack see their revenue take a significant hit. Chart courtesy of Cisco.

Budget constraints once again top the list of CISOs' hurdles to adequate cybersecurity. Chart courtesy of Cisco.
CISOs are feeling the pressure when it comes to cybersecurity management, but new data from Cisco’s annual report may help in getting them the buy-in they need.
The Cisco 2017 Annual Cybersecurity Report, released 1/31/17, outlines some of the major trends and risks facing enterprises, compiling data from surveys of approximately 3,000 CISOs.
According to Cisco CISO Steve Martino, enterprises are realizing that losses from data breaches and cybersecurity vulnerabilities have tangible repercussions for the business. As a result of public breaches, 29 percent of security professionals surveyed say their organizations experienced a loss of revenue, and 38 percent of that group said revenue loss was 20 percent or higher. Security professionals also cite rising losses of opportunity and customers after cyberattacks.
Operations and finance are feeling the effects keenest, as these are the top two functions likely to be affected by a public breach. According to Martino, if an IT department experiences 1 to 8 hours of system downtime (as 45 percent of outages reported do), it can result in monetary losses but also a disruption in services and deliverables. Forty-one percent of network outages affect between 11 percent and 30 percent of the organizations’ systems, significantly hindering the business for an extended period.
Security leaders are also facing increased scrutiny from a variety of sources, including executive leadership, clients, employees, investors, regulators, insurance companies and watchdog groups, the report notes.
However, the impact of a data breach is not always negative in the long run. The survey results show that CISOs and security leaders are using the aftermath of a breach as a learning opportunity – 90 percent of security professionals surveyed said that a security breach drove improvements in threat defense technologies and processes. Thirty-eight percent separated the security team from the IT department; 38 percent increased security awareness training among employees; 37 percent increased focus on risk analysis and risk mitigation; 37 percent increased investment in security defense technologies or solutions; and 37 percent increased investment in training of security staff.
Learn more about the report’s findings, including CISOs’ challenges to address incoming alerts, the race to a faster time to detect, and the return of rampant, malicious spam, read the full report here.
This article was originally published in our monthly newsletter, Today's Cybersecurity Leader. You can subscribe here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





