New Survey Reveals Critical Infrastructure Cybersecurity Challenges

IT executives within critical infrastructure organizations see a need for public-private threat intelligence sharing partnerships (86 percent of respondents) to keep pace with escalating cybersecurity threats, according to a survey by The Aspen Institute and Intel Security.
A majority (76 percent) of survey respondents also indicated they believe a national defense force should respond when a cyber attack damages a critical infrastructure company within national borders. Additionally, although most respondents agree that threats to their organizations are on the rise, they maintain a high degree of confidence in existing security.
The survey, Holding the Line Against Cyber Threats: Critical Infrastructure Readiness Survey, reveals that the critical infrastructure providers surveyed are pleased with the results of their efforts to improve cybersecurity over the last three years, but at the same time many (72 percent) said that the threat level of attacks was escalating. Almost half of all respondents (48 percent) believe it is likely that a cyberattack on critical infrastructure, with the potential to result in the loss of human life, could happen within the next three years.
“This data raises new and vital questions about how public and private interests can best join forces to mitigate and defend against cyberattacks,” said Clark Kent Ervin, The Aspen Institute's director of homeland security. “This issue must be addressed by policymakers and corporate leaders alike.”
Survey results suggest there may be a disconnect between critical infrastructure providers and the current threat landscape:
- Perceived Improvements: Respondents believe their own vulnerability to cyberattacks has decreased over the last three years. When asked to evaluate their security posture in retrospect, 50 percent reported that they would have considered their organizations “very or extremely” vulnerable three years ago; by comparison, only 27 percent believe that their organizations are currently “very or extremely” vulnerable.
- Government Involvement Encouraged: Private industry is often hesitant when it comes to government’s involvement in private sector business; however, 86 percent of respondents believe that cooperation between the public and private sectors on infrastructure protection is critical to successful cyber defense. Furthermore, 68 percent of respondents believe their own government can be a valuable and respectful partner in cybersecurity.
- Confidence in Current Solutions: Sixty-four percent believe an attack resulting in fatalities has not happened yet because good IT security is already in place. Correspondingly, more than four in five are satisfied or extremely satisfied with the performance of their own security tools such as endpoint protection (84 percent), network firewalls (84 percent), and secure web gateways (85 percent).
- Disruptions Increasing: More than 70 percent of respondents think the cybersecurity threat level in their organization is escalating. Around nine in 10 (89 percent) respondents experienced at least one attack on a system within their organization, which they deemed secure, over the past three years, with a median of close to 20 attacks per year. Fifty-nine percent of respondents stated that at least one of these attacks resulted in physical damage.
- Loss of Life?: Forty-eight percent of respondents believe it is likely that a cyberattack that will take down critical infrastructure with potential loss of life will occur within the next three years, although there were no additional survey questions to determine the circumstances under which respondents believed the loss of life could occur. More U.S. respondents thought this scenario was “extremely likely” to occur than did their European counterparts.
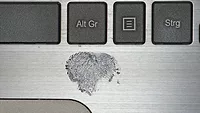
- User Error Still #1 Issue: Respondents believe user error is the greatest cause of successful attacks on critical infrastructure. Organizations may strengthen their security postures, but individual employees can still fall victim to phishing emails, social engineering and drive-by browser downloads that successfully infect their organizations’ networks.
- Government Response: Seventy-six percent of respondents believe a national defense force should respond when a cyber attack damages a critical infrastructure company within national borders.
- Different Country Perspectives: U.S. respondents believe the likelihood of a catastrophic cyberattack on critical infrastructure that could result in loss of life is more certain than do their European counterparts. While 18 percent of U.S. sources consider this scenario “extremely likely” to occur in the next three years, only 2 percent in Germany and 3 percent in the United Kingdom think it extremely likely.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!