Managing Risk Across the Enterprise
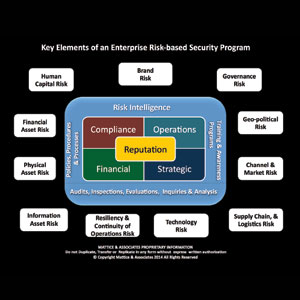
The key to the risk-based security program is that no matter what issue you examine, every one of them affects the reputation of the enterprise in one manner or another.
|
Over the course of the last 18 months we have conducted a fairly exhaustive review of all of the elements that comprise an effective program to identify and analyze the full scope of risks that an enterprise faces while operating domestically or globally. We also explored effective methodologies to examine risk mitigation solution options that can be deployed across the enterprise.
The chart that we provided depicts the various elements of a comprehensive risk-based security program. The key to the risk-based security program is that no matter what issue you examine, every one of them affects the reputation of the enterprise in one manner or another. Understanding the links, dependencies and potential impact of each element of a sound risk-based security program is fundamental to an organization’s ability to effectively deploy this type of program and, ultimately, holistically manage the enterprise’s entire risk portfolio.
The first step is developing an initial risk profile of the enterprise. We have yet to find a single company that has in one place collected the full scope of documentation necessary to create a true snapshot of the enterprise’s risk portfolio. Developing a matrix of current and emerging risks through the implementation of a comprehensive risk intelligence program is absolutely vital. As we previously discussed, there are several different approaches to establishing a comprehensive program to gather risk intelligence. At the end of the day, what is most important is having an effective risk intelligence program for the enterprise, not how it is organized or what function owns it.
Critical elements of the risk intelligence process include: the establishment of the key intelligence questions and the gathering, analysis, processing and distributing of the risk intelligence to those functions that have a legitimate need for the information. The data gathered through the risk intelligence program is also a vital element of the strategic planning process for the enterprise. A trusted risk intelligence program is also critical to ensuring that management has highly accurate and trusted data to utilize in their decision-making process.
Once the risk matrix has been populated, management must then prioritize the risks and determine which are the most critical to the viability, survivability and resilience of the enterprise. When that prioritization has been completed, various functions within the organization can be tasked to design the appropriate solution for the risk involved. Those solutions may involve complex and expensive methodologies to effectively mitigate a given risk. Other risks may involve inexpensive and easy to implement mitigation solutions, third party transfer of the risk through some form of insurance instrument, or the enterprise may simply decide that the probability of the risk occurring is so remote that while an incident could be devastating, the cost to mitigate the risk results in the enterprise simply accepting the risk without deploying any mitigation solutions.
Another key take-away involves the establishment of sound policies, procedures and processes across the enterprise. These provide the foundation for effectively managing the enterprise, establishing the guidelines under which all personnel and functions are expected to operate, and implementing appropriate controls to ensure the long-term viability of the enterprise. Of course, it is necessary to ensure that staff members are thoroughly trained on their roles, responsibilities and accountabilities.
Validation of the design and functionality of policies, procedures, processes and controls are measured through audits, inspections and evaluations. If failures occur or weaknesses are identified in controls, it is vital that an inquiry is conducted to determine the root cause for the failure of the particular management system involved. Once a determination of the cause of a particular failure is made, an appropriate solution can be crafted that prevents the failure from reoccurring. A similar process of evaluation takes place when a risk morphs over time or a new risk evolves which requires an evaluation of the current management systems involved to apply appropriate revisions to mitigate the change to the risks.
Hopefully, through this series our readers have gained a more comprehensive understanding of the full scope of risk that must be gathered, analyzed and mitigated as part of effectively managing an enterprise’s risk portfolio.
About the Authors: Jerry J. Brennan is the founder and Chief Operating Officer of Security Management Resources (SMR Group), the world’s leading executive search firm exclusively focused in corporate security. Lynn Mattice is Managing Director of Mattice and Associates, a management consultancy focused at the development and alignment of Enterprise Risk Management and Business Intelligence Programs, as well as Intellectual Property Protection and Cybersecurity.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!