Like Peas and Carrots: Keeping Like Technologies Together with VLANs
A major trend in the security integration channel has been the evolution of IP security surveillance cameras and Network Video Recorders (NVRs). Instead of using their own dedicated cabling, the devices are sharing the existing IP-based computer network infrastructure. The popularity and affordability of IP networking has driven security integrators to utilize existing Ethernet networks more and more. However, by sharing the IP network, a new set of problems can arise that in a worst-case scenario can make the entire network unusable. Gone are the days of analog security video which had its own dedicated cabling and nothing to interfere with its use.
Having spent countless hours supporting dealers and installers, we’ve encountered a common problemthat is caused by sharing the IP-based network. What we have found is that a newer generation of IP devices, such as video-streaming devices and home controls, send out multitudes of broadcasts that can clog up bandwidth and thus affect the performance of other devices on the network, especially security cameras and the associated NVRs.
In the past, when personal computers were the only devices on the network, the computing experience was not impacted if bandwidth was not sufficient. The user’s satisfaction was not diminished if he or she received a file in 35 seconds rather than 30 seconds. Unlike computer data networks that can tolerate a certain degree of unpredictable latency, IP cameras, video and audio streaming, control systems cannot. The packets that carry surveillance video must arrive on time and in order, and IP-based controls cannot lose critical command packets. In other words, today’s sophisticated IP networks require a new level of robustness in order to even perform their basic functions.
A New Way to Design Network Infrastructure
As technology evolves, it seems as though infrastructure is the last to catch up. As automobiles became faster and more prevalent, for example, paved roads and multi-lane highways took decades to develop. The same is true for computers and IP devices versus their infrastructure. Audio and video devices have advanced and are now IP-based so they share the same network as computers and printers.
Meanwhile, the routers, switches and wireless access points that make up the IP-based infrastructure remain the same in features and functionality, as if there are only computers on the network. The routers and switches sold today for the residential and commercial market have the same basic "intended use” features as devices sold 10 years ago. The prevailing standard, by and large, still assumes that a given network will only be used for basic computing, such as file sharing and Internet access. This archaic standard also assumes that there is very little broadcast packet traffic, which is characteristic of today’s new audio/video-based IP devices.
Eliminate Wide Broadcasts
One problematic feature we've discovered is that IP-based audio/video streaming and home control devices send out numerous broadcasts to stay in sync. Let's say that all security IP cameras are connected in a single Local Area Network (LAN) with a switch. Switches, Layer 2 devices, are designed to forward all broadcasts, but that's not always a good thing. A switch in a typical home might have anywhere from 12 to more than 100 ports with all the devices using the network. By default, all hosts connected to that switch are going to be in the same broadcast domain because everything is connected in a single LAN.
Now, let's say you have 100 ports on your network. If one host connected to that switch sends a broadcast, by default, all of the other 99 hosts are going to receive that broadcast. These unnecessary broadcasts will soak up your network's available bandwidth. Moreover, for some network services and protocols used today, a broadcast received by a host triggers that receiving host to transmit a broadcast of its own. When all of the hosts receive that second broadcast, they respond by transmitting additional broadcasts. In moments, these broadcasts have swelled into a broadcast storm that can take up a major part of a network's bandwidth and make normal network operations almost impossible. Imagine what this means if you are trying to stream IP surveillance video to an NVR over this network! Just wait until you start streaming even higher megapixel resolution videos.
Introducing Virtual LANs or VLANs
VLANs are essentially segmentations of the entire LAN into smaller LANs grouped together by services, which address issues surrounding broadcast filtering, security and traffic flow management. Today’s security installers need to segment the network into smaller networks where similar devices reside; otherwise, there is potential for trouble. VLAN technology has been around for many years now. At the most basic level, a VLAN is nothing more than a broadcast domain. Devices that perform critical communications must be grouped together. For example, different sets of groupings might be surveillance videos and the associated NVRs, Voice-over-IP (VoIP) phone systems, devices streaming audio and video from a central server, devices that provide home automation and, finally, the computer network.
Each of these categories needs to be in its own sub-LAN where devices can perform their critical functions without being affected by other devices that they do not need to communicate with. The installer’s job is to logically construct VLANs to separate out surveillance videos, VoIP, audio/video streaming, home controls and computing into broadcast domains. Broadcasts won't be forwarded or propagated between VLANs, and a broadcast sent by one host in a VLAN will be forwarded only to other hosts in that same VLAN.
By default, there will be no inter-VLAN traffic on the switch. But what if a computer needs to communicate with an IP surveillance camera? For traffic to go between VLANs, a Layer Three device, or a router with VLAN-aware capabilities, needs to be added to the network.
To finalize this new type of IP-based network, each newly created VLAN, when accessing shared resources such as the Internet, cannot have equal priority with the others. The VLANs containing devices with digital media assets, such as surveillance video and VoIP audio, must be given top priority in this new network. Remember, a computer downloading a file in 35 seconds versus 30 seconds does not affect the user’s experience, whereas a lost or delayed surveillance video packet can completely ruin a security system.
In summary, designing and implementing a VLAN-with-priority network allows security integrators to break up a large, loud network into smaller, separated groups that can communicate effectively while each is still connected to a greater extended network. 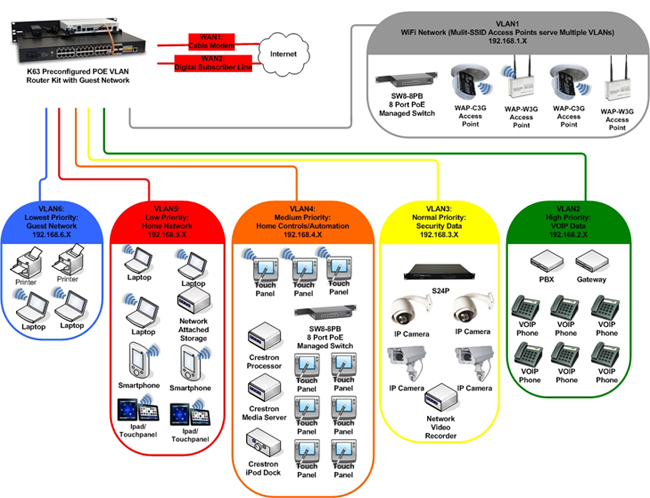
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






