Biometrics Bridges Physical, Logical Security

For some
biometrics readers, advanced antimicrobial technology has been added to reduce
the spread of micro-organisms.
The various biometrics-based approaches have been around for years, mostly providing physical access control and time and attendance. With the integration of biometrics readers into networks, desktops, laptops and mobile wireless devices, the shift started to a more all-encompassing solution that can also bring together chief security officers and their IT security colleagues. Another important trend centers on the integration of biometrics into access cards and badges.
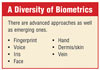
Biometrics are technologies that automatically confirm the identity of people by comparing patterns of physical or behavioral characteristics in real-time against enrolled computer records of those patterns, according to the International Biometrics Industry Association. Leading biometric technologies accomplish this task by scanning patterns of the face, fingerprint, hand, iris, palm, signature, skin or voice.
There has, however, been some concern relative to privacy when a biometrics-based system is used to identify or provide authorized access to a facility or computer system. Elsewhere in this issue, Don Erickson, in his column According to SIA, addresses the efforts of some states to legislate controls over the use of biometrics.
However, many in the security industry contend that biometrics helps protect privacy by erecting a barrier between personal data and unauthorized access. Technically, biometrics-based capture devices create electronic digital templates that are encrypted and stored and then compared to encrypted templates derived from “live” images in order to confirm the identity of a person. The templates are generated from complex and proprietary algorithms and are then encrypted using strong cryptographic algorithms to secure and protect them from disclosure.
Federal government requirements, post 9/11, also are driving biometrics into dual functionality – physical and logical.
With FIPS 201-1, for example, chief security officers are empowered with a tool to check the identity and status of individuals needing access to enterprise or government resources. This provides capabilities beyond those of most legacy physical access credentials. It is important to understand the different authentication mechanisms and the levels of threat they mitigate. With this knowledge a CSO is in the best position to decide how to employ the FIPS 201-1 credential within the context of an overall security plan, bearing in mind requirements for throughput, operational and interoperability considerations.
In transitioning to accepting PIV credentials, biometrics experts recommend that to first define the end-state identification verification goals, then decide the equipment, if any, needed to help accomplish this goal and finally, develop a transition and migration plan that meets the agency’s needs and budget.
The PIV credential enables agencies to implement a range of identity authentication methods, allowing the appropriate

Iris and retinal
scanning has advantages when it comes to some biometrics applications.
PHYSICAL AND LOGICAL IDENTITY CONVERGENCE
The high cost of data breaches and the need to meet compliance regulations are pushing organizations to adopt heightened identity and access management (IAM) processes. Companies are looking to physical and logical identity convergence in order to increase security, reduce redundancies and create complete audit trails.Converging physical and logical identity and access management enables organizations to more closely monitor what employees are accessing not only when but from where. In essence, identity convergence enables organizations to add a fourth factor of authentication. Traditionally, there are three possible ways in which employees can prove their identities — through what they know (a password or personal identification number (PIN)), what they have (a proximity or smart card) and who they are (a biometric). When physical and logical identity management are converged, companies can also use a fourth factor of authentication — where a person is — in order to verify his or her identity.
For example, you can prevent employees from accessing their desktop if they have not first authenticated themselves at the door. This can prevent unauthorized access to a coworker’s computer before they arrive in the morning — even if their usernames and passwords have been compromised. Converging physical and logical identity further strengthens security, enabling organizations to close off previously difficult to detect security gaps.
According to a study by Deloitte, most employees are given 17 user accounts within the course of their employment, but only 10 of these are deleted on average when they leave. The orphaned accounts leave an organization vulnerable to insider threats. When physical and logical IAM are converged, applying a single identity for each individual within an organization is more achievable.
Without a unified IAM policy, a person’s user accounts and credentials can become rogue identities that can be used to gain unauthorized access to information. With unified IAM, all of a person’s user accounts and credentials are managed centrally under their identity. When they leave, their identity and associated rights and privileges are removed, effectively disabling all of the user accounts and credentials they were assigned during the course of their employment.
This also simplifies assigning employees new privileges when they take on new roles. Administrators can simply delete them from one user group and assign them to another to give them physical and logical access to everything they need for their new role. This prevents the time lag and delay it generally takes to get a user account started — a period in which employees are either unproductive or tempted to borrow each other’s account — a clear violation of many compliance regulations.
Physical and logical convergence also enables companies to use the same credentials, such as a fingerprint biometric, for physical and logical access. This can lower the cost of access control accessories as one authentication factor can be used for both. Significant return on investment can be achieved by this as, for example, according to a study by Datamonitor, managing smart cards can take 9.5 hours a week while biometrics can take less than an hour to manage.
Using the same credential for both physical and logical identification requires technological interoperability. For example, the biometric reader on an employee’s laptop should be able to use the same template in order to make a match as the biometric reader at the employee entrance.
Physical and logical convergence can also help organizations create more complete audit trails, enabling them to monitor not only the who, what, when and why when confidential information is accessed, but the where.
At the International Security Conference just two months ago, there was other indications that biometrics is bridging between physical and logical security.
For example, Privaris, a provider of personal, biometric identity verification solutions, won Security Industry Association New Products Showcase award for its plusID 75 trusted biometric token in biometrics product design plusID 75 is a multi-function personal identity verification token that leverages Bluetooth and RFID technology and ensures secure wireless logical (IT) and physical access. It is the latest addition to Privaris’ plusID product line designed to meet the growing market demand for a convenient, yet secure and cost-effective solution to today’s network and facility access vulnerabilities. The plusID 75 identifies itself to PCs and laptops exactly as a smartcard does, and to door readers exactly as a Prox or iCLASS card, allowing for a fast and simple upgrade to biometric logon with no installation or additional middleware required. The solution also works with select single sign-on (SSO) software. The plusID 75 reduces the administrative hassle and the expense of IT password management and eliminates the security issues surrounding lost or stolen cards and passwords.

Fingerprint
biometrics is the leading way to join physical and logical security access
control.
HEALTHY BIOMETRICS
Ingersoll Rand Security Technologies is using an advanced antimicrobial technology to reduce the spread of micro-organisms on its HandKey and HandPunch platens. All recently-ordered Schlage HandKey and HandPunch terminals will incorporate this technology. A special silver-based agent, using BioCote technology, is embedded into the materials used to produce the platen of the biometric hand geometry units, providing a hygienic finish that resists bacterial degradation.West Virginia University’s Student Recreation Center is using its biometric hand reader technology, in addition to the card swiping system already in place, to control access to the facility. HandKey readers simplify credential management and ensure that only authorized individuals enter the recreation center.
“The primary reason that we brought in this device was convenience for students,” said Carolyn McDaniel, assistant director of Student Affairs Business Operations. “The students have said that they don’t want to bring their card. It is one more thing for them to keep track of. The Rec Center is probably the place where cards are most often lost.”
McDaniel said about five lost student ID cards are found by Rec Center employees every day, prompting the switch to biometric access control. Students, faculty and staff interested in using the handreader instead of their WVU identification cards first enroll in the program.
The reader has a flat platen with five metal posts embedded in it. When registering for the service, the user places his or her hand on the platen with each finger touching a corresponding post. Three measurements are taken and the average is saved to the student’s account. Once registered for the program, Rec Center patrons no longer use their ID cards to gain admittance; only the scanner lets them in.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






