IDSystems: Those Risks You Never Anticipate
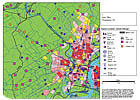
Proximity analysis can aid retailers in determining the security risks relative to a location of a store.
The retail environment is in a constant state of flux. Employee turnover, heavy foot traffic and unconventional operating hours all contribute to the primary focus of most chief security officers, security directors and loss prevention executives: protecting their store’s physical assets.
With the proper event forecasting tools in place, security personnel can address these issues, while preserving and – in some cases – increasing their store’s profitability.
The corporate security/loss prevention department can actually become a profit center. Proper analysis using modern statistical techniques can offer suggestions for security resource allocation and reallocation, both of which not only reduce security costs, but also produce revenue generation by reducing real dollar losses.
Surprisingly, workers’ compensation and general liability claims, as well as associated dollar losses, often exceed the dollar losses of more traditionally crime-based losses. These claim types create an additional profitability impact in the form of increased costs, low employee morale and lost worker time. Inefficiencies and increased corporate liability exposure can also result, each due to the use of inexperienced and/or less adequately trained replacement or temporary employees.
Security can reduce these kinds of losses and their corresponding negative profitability impact by using analytical techniques. These techniques uncover the relationships that exist among workplace characteristics, practices, various workers’ claim types and their dollar value. Experience has shown that such analysis can significantly reduce the numbers and dollar value of workers’ compensation and general liability claims.
Parking lot-related premises liability lawsuits are on the rise in all kinds of business-related environments, including retail operations. The fact remains: The protection of assets, personnel and customers within a store is the most important concern of any security function. But more recently, retail operations are becoming increasingly concerned with parking and exterior common-area security, as well as their associated liabilities. Even more noteworthy is the impact that exterior criminal activity can have on employee morale and business reputation among customers.
Often times, security only considers crime risk of the immediate environment in site selection and security resource allocation. However, research indicates that criminal activities migrate to desirable targets. Therefore, retail site operators may benefit from an assessment of crime potentials, originating from relevant areas beyond the immediate environs of the store.
The need for business analytics and quantitative assessment has never been more vital in the field of security and loss prevention. The ability to anticipate potential risks and develop adequate and operationally feasible safeguards is imperative to profitability and consumer confidence.
National Theft Database Battles Shoplifters
Shoplifting has been around as long as stores and shops have existed. Retailers have always struggled with it and now see organized gangs shoplifting. But recently President George Bush signed legislation establishing an Organized Retail Theft (ORT) Task Force at the FBI and the creation of an organized retail crime database. The development of these databases with information on organized retail theft incidents and patterns is seen by the FBI and retail security as one of the most important tools in the fight against ORT.One ORT example is software from ADT Security Services, Boca Raton, Fla. It allows store personnel to quickly and easily log information about an ORT event. The software takes the salesperson through a survey of preset questions and records information that includes the location, date, time and merchandise taken. Retailers can analyze ORT patterns and identify problem areas or frequently targeted merchandise. It should help the FBI and other law enforcement officials quickly identify hot spots across the country and rapidly send resources to those areas.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!