Locking the Keys Up

Jump to today and most key and lock concerns center on lost keys or how to better manage different levels of keys for a diverse workforce. Some still use lock boxes, manual logs or key identification tags.
Products, systems and services now aim at helping security executives move away from such outdated approaches to embrace electronic key management.
Tracks key users
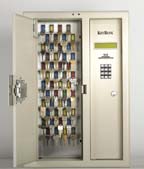
One example is the KeyBank from MorseWatchman, Oxford, Conn. Aimed at multifamily key security, the system is used by security executives at condominiums, retirement complexes, apartment buildings and residential hotels. Electronically monitored, color-coded and tamper resistant so-called “smart keys” reside in a high technology, wall-mounted key storage cabinet. The system records the access history of each key and user with programming and report generation through a built-in keypad and LCD.
On the corporate and commercial side, Morse Watchman has KeyWatcher. In this design, there are extensive key management reporting options, centralized programming, advanced networking capabilities and real-time transaction polling.
The BodyTag BT-002, for instance, is an intelligent Bluetooth tag from Bluelon of San Jose, Calif. It tracks and indicates the position of personnel, animals or materiel. In can work in combination with the company’s BlueAccess access control systems. The BT-002 is made of shock-resistant plastic and can be attached to an individual’s clothing or worn around the neck using a strap.
An individual wearing or carrying the device will be registered at access points covering the area in question. Bluetooth technology operates locally and is therefore free to use without the need of any external services such as costly mobile subscriptions. In addition to the BodyTag, systems can use a Bluetooth mobile phone or PDA to gain access through door or gate systems where a Bluetooth ID is accepted. Users can get instant access, without further verification, or be requested to authenticate with a predetermined pin code depending on your personal or corporate security requirements.
For More Information
There’s more information on key management from Morse Watchman at www.morsewatch.com while BodyTag and Bluetooth access control details are from Bluelon at www.bluelong.com. Also check the Security magazine Web site at www.securitymagazine.com. Use the LINX service on the opening page. Powered by Google, LINX lets you enter keywords to search the Security archives.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







