Navigating CISOs' top 4 challenges

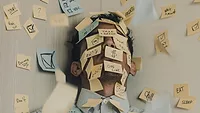
What keeps a chief information security officer (CISO) up at night? We are asked this question frequently, and the answer is complex. The field of cybersecurity is dynamic, with conflicting, high-stakes priorities and never-ending time-sensitive tasks. Working diligently to protect their organizations, CISOs face a variety of challenges without simple answers, and the steps to address them are often nebulous, time-consuming and resource-intensive. Let’s take a closer look at what is top of mind for the CISO community and what strategies they can implement to address these concerns moving into 2024.
The top CISO challenges
Though they may vary across industry and organization size, there are a few universal challenges:
1. The expanding attack surface
We know that threats have advanced. Tools like AI and inexpensive access to phishing kits and ransomware have lowered the barrier to entry for aspiring threat actors. But equally important to the discussion is the expanding attack surface — the area through which a company can be compromised.
The evolution of AI technology is outpacing concerns for security and privacy, which is a top concern for anyone in security leadership. API security is another concern that has become a greater priority in recent years. Not only are there more points of entry, but the bad actors have become more competent and have more tools in their arsenal for API attacks. Also, the pandemic blurred the lines between home and office. Many companies now have employees who may never operate within a corporate network, yet security teams are still responsible for protecting these employees, their devices, and the apps and data they access. Gaining visibility into these systems without real control over them is a significant challenge.
2) Slowed budget growth clashes with increased costs
With each new threat comes a new category of vendor tool to address it, but unfortunately for most, budgets for 2024 are not growing like in recent years. Research from IANS shows budget increases have slowed to an average of 7%, and for some, budget growth has plateaued. Meanwhile, vendors are upping prices because their business costs have increased, leaving security decision-makers in a bind. There is more to secure, new threats on the horizon, and greater operating costs to anticipate, but budgets cannot expand to accommodate necessary changes, and tough decisions must be made.
3) Increased personal risk
CISOs have historically faced substantial pressure, but recent updates to disclosure and reporting compliance highlight the increased personal responsibility that these leaders hold. The new SEC regulations call for faster disclosures with murky guidelines for what constitutes a “material” event. Meanwhile, there are multiple examples now of CISOs being held personally accountable for their actions concerning breaches. Regardless of your stance on guilt or innocence in these specific circumstances, these cases shed light on a pivotal shift in personal risk for security leaders.
4) Just keeping up with the pace of change
One look onto the show floor at any industry trade show will provide evidence of how rapidly the cybersecurity industry is changing. Dozens of new vendors claim to address problems that didn’t exist a year ago — Black Hat booths were full of API and SaaS security vendors, and it was AI before that at RSA. Staying informed about the latest tools, tactics, and threats can seem like a never-ending battle.
Navigating complex cybersecurity challenges
There’s no magic solution when the challenges are complex. Still, some strategies will help alleviate some of the pain as you begin planning for 2024:
1) Reevaluate existing toolsets and capabilities
Budgets are tight. The threat landscape has changed. Is there a costly technology or solution that you deployed five years ago that can be replaced with something more modern? For instance, it could be time to upgrade from traditional antivirus to endpoint detection and response. Review customer and regulatory requirements and check inquiries for specific capabilities or security requirements. Compare your security posture with industry standards and frameworks to see if there are logical places to make changes in your stack, and then realign accordingly to meet or exceed those standards.
2) Revisit existing policies
Just like technology, policies can quickly become outdated. They must be revised, replaced, or even removed. Although this isn’t the most exciting area of CISO work, creating clear policies that are proactive and empowering, not restrictive, can ensure employees gain the benefits of new technology without the risk. For example, generative AI (GenAI) can offer enormous benefits for a company — improved productivity, efficiency, and creativity. But without appropriate guardrails to govern how the technology is used and what data (or code) can be input into GenAI models, a company could be at extreme risk for compromise. Creating a formal policy with input from stakeholders throughout the company enables employee use of the technology while reducing risk.
3) Seek out peer resources for learning
Knowing where to go and who to lean on in a time of need is half the battle. When evaluating new technology or dealing with new malware, chances are high that someone else is facing the same situation and has an effective strategy. Take advantage of peer networking groups and nonprofit organizations (here's a great list for starting) as well as social media groups and Slack channels. Connect with others, listen to podcasts, or visit industry sites for news whenever possible. Push yourself outside your comfort zone to share your own stories and talk about the topic that you're passionate about so that others can learn from your experiences.
Although the CISO role is incredibly challenging, it is rewarding. The complexities grow each day, but the problems are not unsolvable. It can be helpful to gather insight from peers regarding how they prioritize and balance what may seem like infinite responsibilities and concerns — especially when it seems like pressure on CISOs is mounting and the only constant is change. No doubt, the next year will bring unexpected new threats and groundbreaking new tech, but by working together we can successfully navigate the constant changes and challenges of cybersecurity.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!