Product Spotlight: Integrated Intercoms for Robust Security
New intercom technology merges with surveillance, access control and more to create a more unified entryway security solution.

Adds Access Control Readers for Improved Efficiency
Adds Access Control Readers for Improved Efficiency
Additional security system integration is now possible with Aiphone’s IS, IX and JP series audio/video entry systems. The video door stations can be configured to include HID multiCLASS SE readers, which support an array of credential technologies and a variety of access methods, including cards, fobs and mobile devices. These stations can integrate with new or existing access control systems, and they enable enterprises to reduce costs and improve staff efficiency by controlling security needs either from a central location or remote user.
Find out more at www.aiphone.com

Combines Security Functions from One Cat5 Cable
Combines Security Functions from One Cat5 Cable
Audio, video, access control and power are all combined in one cat5 cable in this next-generation update of Net2 Entry from Paxton Access, Inc. The latest versions feature MIFARE® technology, an intuitive panel interface and digital pan/tilt camera functionality. The updated system also includes a versatile grouping feature that enables smarter management and the separation of multiple Net2 Entry systems into multiple groups, allowing the control of selected monitors from selected panels.
Find out more at www.paxton-access.com

Acts as Virtual Guard to Enhance Effectiveness
Acts as Virtual Guard to Enhance Effectiveness
The TCIV IP and SIP video station from Vingtor-Stentofon provides a dynamic HD quality solution that is flexible, expandable and easily integrated. The TCIV mitigates noise and bandwidth issues with active noise cancellation, echo reduction and processing power at the device. Security officers can use this device to see, hear and speak in real time. This critical communication solution was designed to withstand extreme fluctuations in temperature, aggressive vandals, dirty and dusty environments, and water.
Find out more at www.zenitel.com

Works with VMS for Video Evidence Retention
Works with VMS for Video Evidence Retention
This compact video door entry station from Talkaphone works with major video management system vendors to offer greater deployment flexibility to higher education institutions, healthcare and corporate facilities, among others. The station is SIP compliant and allows other IP devices to be connected directly into the unit and share network connectivity. The wide-angle megapixel camera is ONVIF compliant and offers complete entry visibility.
Find out more at www.talkaphone.com
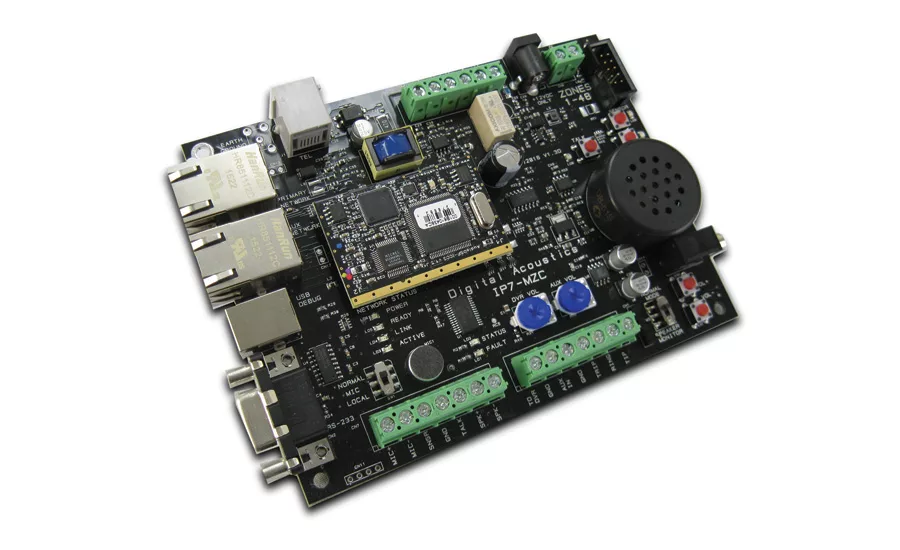
Designed for Remote Monitoring Applications
Designed for Remote Monitoring Applications
This multi-zone controller (MZC-FD) from Digital Acoustics was designed to enable remote monitoring or central station operators to connect over a network to a single endpoint that controls up to 48 zones – simultaneously, individually or in groups – with clear two-way audio. This provides operators with the ability to talk, listen and respond in near real-time without the added cost of phone lines. This product family is the industry’s first IP-to-analog bridge with full-duplex audio, user-configured expansion and digital quality in two-way monitoring zones.
Find out more at www.digitalacoustics.com
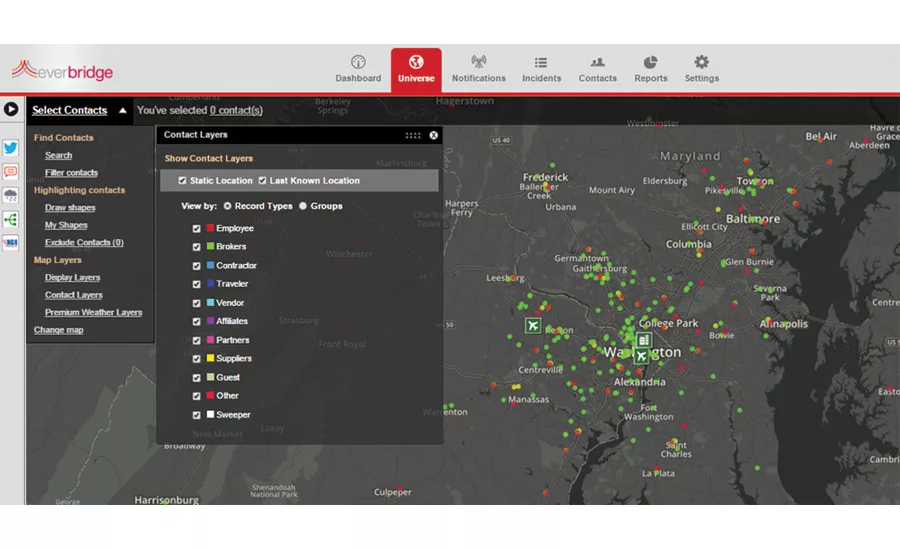
Combines Access Control with Location Awareness to Contact Employee
Combines Access Control with Location Awareness to Contact Employees
In the event of an emergency, the Safety Connection function from Everbridge combines data from physical access control system with multi-factor location awareness data to rapidly find and communicate with employees. This solution improves enterprises’ ability to prioritize safety and communications by coordinating an employee’s last know location, work schedules and travel itineraries. Enterprises can use the system to automate mustering, building evacuations and “shelter in place” commands, and use two-way communication to reach out to specific individuals.
Find out more at www.everbridge.com

Eliminates Need for Regular Maintenance Checks
Eliminates Need for Regular Maintenance Checks
The fault-monitoring and self-reporting feature of these Code Blue IP1500 and IP2500 Voice over IP (VoIP) speakerphones eliminates the need for regular maintenance checks. The speakerphones are available as lightweight surface and flush mounts that are vandal-, UV- and weather-resistant, and suitable for a range of indoor and outdoor locations, including hallways, stairwells, classrooms, subway cars, parking garages, elevators and door entries.
Find out more at www.codeblue.com
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing