Fraud rings: Detecting and defeating cybercriminal networks

Image via Freepik
The biggest key to success for any criminal fraud ring is its ability to exploit weaknesses in identity protection. Fraud rings thrive by cultivating personas that can find their way around traditional fraud defenses of businesses and create multiple false identities within the ring that will max out the amount of acquirable credit. They then vanish into the ether. With this level of coordination, opportunities for fraud rings to do their nefarious deeds are high. Still, there are ways for businesses to fight back.
Exposed Identity Elements
While fraud rings can vary widely in their size and scope, they often share characteristics. Whether the ring is a massive operation or a smaller one, these groups can cause large amounts of financial damage and headaches. This can happen in a short period of time or fraudsters can sit on stolen identity data for years before they attempt to exploit it. An aspect nearly all fraud rings share is that they typically target the bankcard, wireless and retail card industries, with wireless being the most heavily targeted according to internal LexisNexis Risk Solutions data.
One of the biggest factors that allows a fraud ring to flourish is the presence of exposed identity elements. Fraud rings are quite adept at taking advantage of issues like data breaches that expose personally identifiable information (PII), leading to the potential for new account fraud.
When these breaches occur, fraudsters can pick through the leaked information and create accounts with these personal details, evading detection by carefully choosing which personal identity elements to use. Unfortunately, these breaches are oftentimes found when it’s too late, making it difficult to tie the loss back to any person or persons that caused it.
Fraudsters Coordinating to Find Weak Spots
Fraud rings are also adept at avoiding traditional protections against fraudulent activity. These rings are most successful when they use coordinated, organized attacks to cause as much havoc as possible. It’s necessary for businesses to use a multi-dimensional strategy to cover the possible points of weakness in their system. By using an approach like this, we can see risk patterns emerge, including:
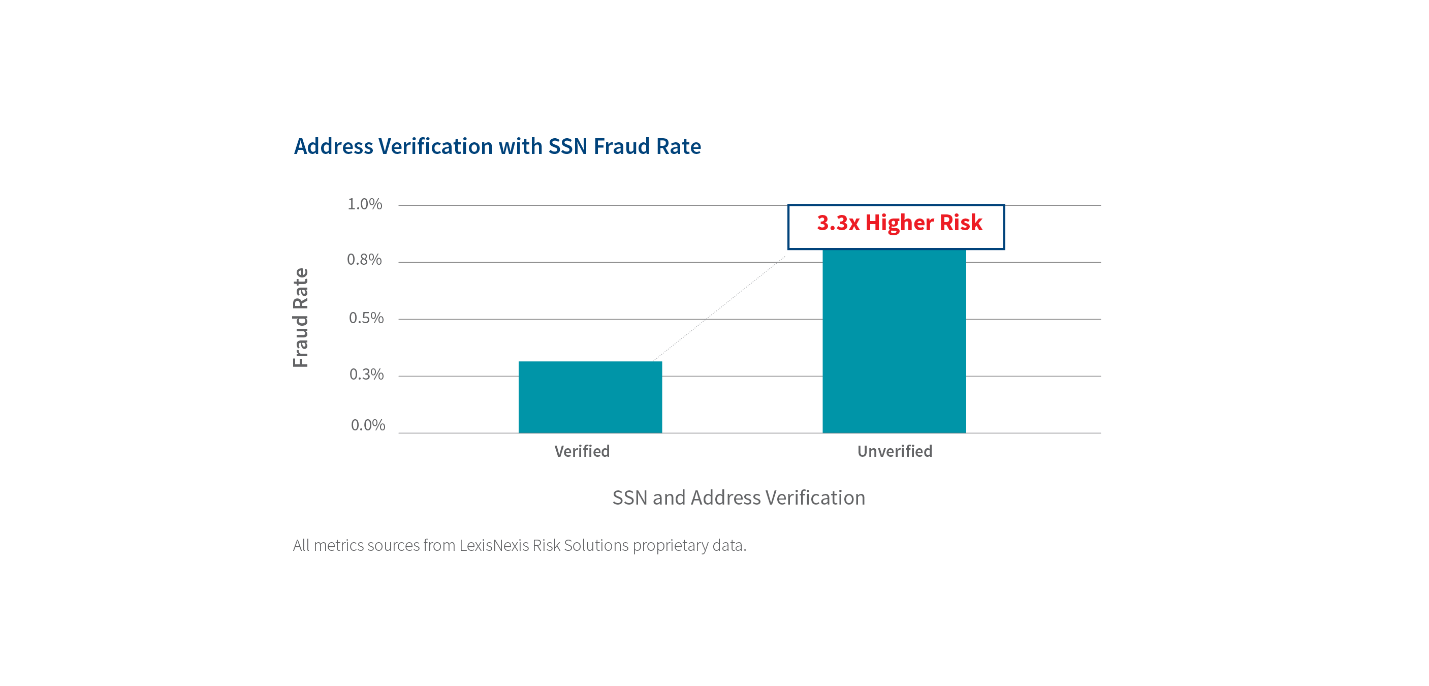
- When a user’s address isn’t verifiable with a Social Security Number (SSN), internal data show that the risk of fraud can increase three-fold. This is problematic because fraudsters can reuse different parts of the PII to create new synthetic identities.
- Fraudulent activity is identifiable when a fraudster keeps the main elements of the PII of a stolen identity the same, but information like home addresses and emails change over time.
- Fraudsters will often use varying email addresses across different applications to avoid detection. However, a sophisticated defense against fraud can detect connections between email addresses and root out nefarious behavior.
Inconsistent and unverified PII connecting applications and identities is very telling. As indicated in the image below, there is a 3.3x higher risk of fraud when an address is not verified with the SSN. This is due to the reuse of PII elements to make new identities.
 The light blue dots below represent the initial application network identified and the green dots are additional identities linked.
The light blue dots below represent the initial application network identified and the green dots are additional identities linked.
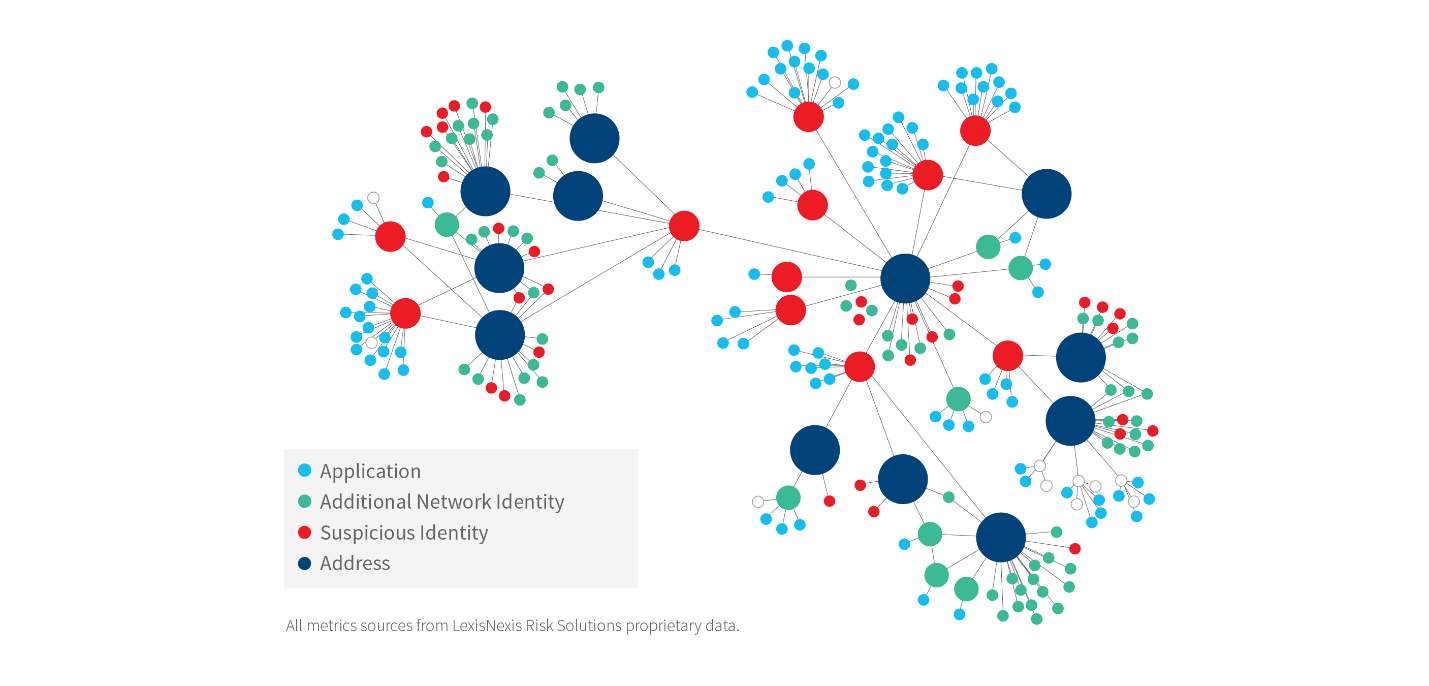
This analysis illustrates the methodical and well-coordinated planning and levels of collusion endemic to typical fraud ring operations and highlights why fraud rings are realizing repeated success in evading and exploiting traditional fraud defenses.
How Businesses Can Protect Themselves
Fraud rings are most successful when they’re organized. However, with a multi-faceted approach to rooting out these rings, it is easier to identify the larger networks of financial crime to which these rings connect. It’s possible to stop these nefarious organizations by using an approach to identity that takes multiple factors into account as opposed to traditional fraud defenses that deploy point solutions.
There are several ways that organizations can apply a risk-based approach to fraud rings and their operations strategy. Businesses can identify a significant amount of additional risk by consolidating data across multiple institutions and linking it with supplemental data and intelligence. Not only can this approach help businesses more easily identify a fraud ring attack, but they also understand which identities within those rings link to larger suspicious networks. This is possible when fraud platforms tie common pieces of a digital identity together like behavioral biometrics and email intelligence to expose as many malicious actors as possible.
Of course, it’s much more beneficial to root out a ring before it strikes. A business may be able to detect identity fraud rings early on by viewing identities associated with known fraudsters and looking for interconnections. When these connections are strong, the individuals are likely participating in a fraud ring. With early identification comes early prevention, which will help protect your company and your consumers.
There’s not one way to stop a fraud ring from attacking a company or organization. A company can set itself up to prevent more fraud by having defenses that rely on the data a business is already collecting. Companies can help put a stop to these malicious actors with proper preparation and a defensive stance that prioritizes digital identities.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!



